By now, you’ve heard of Encrypted Traffic Analytics, Cisco’s latest innovation that allows organizations to leverage the network to find threats in encrypted traffic.
Wondering why this is big news? Consider these statistics (Gartner and NSS Labs):
… 63 million new devices are attaching to enterprise networks every second by 2020 (Gartner) – that’s a lot of information traversing the internet
… 55% of that traffic is being encrypted. That number is expected to increase to around 80% by 2019
… 70% of attacks will use encryption in 2019
With these numbers in mind, traditional threat inspection with bulk decryption, analysis, and re-encryption will become impractical or infeasible. This is why Encrypted Traffic Analytics, a new innovation in flow analytics, is important. It helps you understand the characteristics of encrypted traffic, without the requirement to decrypt the payload.
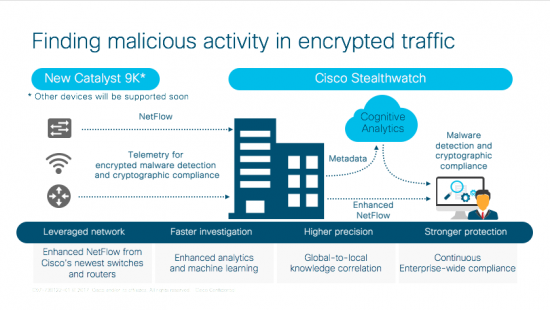
What do you need to enable Encrypted Traffic Analytics?
- The Catalyst 9300 Series Switches. It starts with the network infrastructure. Designed for security, mobility, IoT, and the cloud, these next-generation switches allow organizations to centrally manage policy, simplify operations, handle threats with built-in end-to-end security, and gain visibility into wired and wireless access networks.
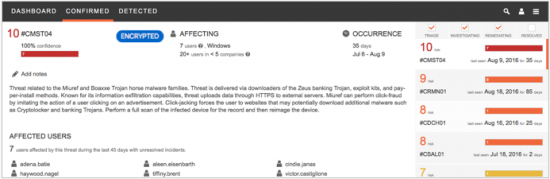
- Stealthwatch then collects enhanced NetFlow from the network and provides real-time monitoring and views into all network traffic. It improves visibility, security, and response times to incidents across the entire network and creates a baseline of normal activity for a user or host, and applies context-aware analysis to automatically detect anomalous behaviors.
- Cognitive Analytics, a cloud-based threat detection and analytics capability now available in Cisco Stealthwatch, allows you to obtain deep visibility into both web and network traffic. This additional contextual information provides visibility and analytics allowing you to identify and prioritize new and emerging threats across the extended network.
Together, these three products deliver Encrypted Traffic Analytics, and help organizations address cryptographic compliance and detect malware within encrypted traffic on the network.
This is network security for a new world. The Network. Intuitive. For more detailed information, check out the white paper here.






Thanks for this overview Jason, I had a colleague of mine who was curious as to just how this could be achieved.
Glad it was helpful, Anthony! Stay tuned for more information and assets about Encrypted Traffic Analytics.
Thanks for the information Jason, it's extremely helpful.
Hi Jason, And thank you for the information. Without decrypting the packets, I can only see where the anomalies could be detected in the cryptographic requirements in the headers and trailers. Will this be explained in more detail in the rumored Cisco Cyber Ops certification? I am excited to see what comes out.