Cisco Umbrella APIs help you create awesome programs
Dear reader. This is the first in a series of blogs where I will discuss Cisco Security solutions and their respective API’s. The goal of these blogs is to enable you to leverage the most out of the various Cisco Security solutions and customize them according to your needs. This first blog in the series is about Cisco Umbrella and how its API’s can be used to create awesome programs. We’ve even produced a series of videos that will allow you to get hands-on with those API’s.
Stay tuned for more blogs in this series about AMP, Firepower and more API’s!
Extend Cisco Threat Response to any HTML based page in Chrome!
Cisco Umbrella is a unique platform which offers both real time Threat Intelligence, as well as the capabilities to mitigate attacks across an organization in a split second. Umbrella combines many sources of data (among which the daily 175B DNS requests sent to the platform) to detect and predict malicious actors on the Internet. On top of that you can leverage Umbrella to block domains instantly for all on-premise and off-premise devices. The Umbrella Investigate and Enforcement API offer these functionalities respectively, enabling developers to take full advantage of these unique capabilities from their own customized programs. To be more precise: developers can now have access to a very rich Threat Intelligence source, while at the same time block domains for their users, both on and off network.
A good example of the use of these Umbrella API’s in action, is Cisco Threat Response (CTR) and the CTR Chrome Plugin (now in beta, try it out!). The Plugin uses both the Enforcement and the Investigate API. It lets users research any observable (e.g. Domain, IP-address, File-Hash, URL, etc.), on any HTML-based webpage, in Chrome by selecting the text and right-clicking on it. Check out the screenshots and descriptions below to understand how it works:
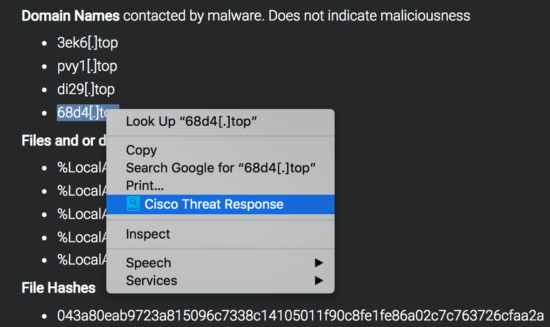
First you select the text (this can also be multiple observables or an entire block of raw text, the built-in parser will take care of the rest), and right click. Then you click on the browser plugin Cisco Threat Response:
After that the well-known pivot menu from Cisco Threat Response pops up natively in your browser window. The Chrome Plugin uses the CTR API (the “Inspect” API endpoint) in the background to parse out the observables from the selected text. This CTR “Inspect” API endpoint takes raw text as input and can parse out and classify observables, like IP-addresses, file-hashes and domains, and return this is JSON format. This makes it very easy to integrate CTR with any other solution, as the data does not have to be in a certain format. As mentioned, the Chrome Plugin allows you to select 1 observable, but you can also select an entire block of raw text and the CTR “Inspect” API endpoint takes care of the rest. As you can see in the screenshot below, the Judgement of this observable can be viewed directly: “Malicious Domain”. This has been queried using the Umbrella Investigate API. Next you are able to directly block the domain, without ever leaving the page you were visiting (in this case the Talos Threat Roundup of November). The domain is blocked using the Umbrella Enforcement API (“Block this Domain”).
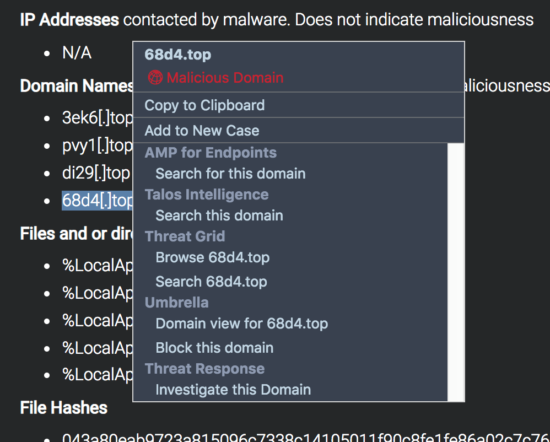
When you would click on “Investigate this Domain” you would cross-launch into CTR and all of the configured modules will be queried for the Observable(s). For example, the Umbrella Reporting API (available with all Umbrella packages) will then also pull in Umbrella events to the Cisco Threat Response dashboard (if there are any sightings of the Observable).
Hopefully this has given you an idea what these Umbrella API’s can do. If you want to learn more about the Umbrella API’s and get hands-on yourself, please check out the DevNet videos below!
If you’re attending Cisco Live in Barcelona, check out the many security related workshops and sessions coming to the DevNet Zone. In the DevNet session “Threat Hunting using APIs – DEVNET-2638” the security API’s will be discussed in combination with Cisco Threat Response. Also, there is a specific Breakout Security session about Cisco Threat Response, where the CTR API’s will also be discussed. Please join BRKSEC-2433 if you are interested!
We’d love to hear what you think. Ask a question or leave a comment below.
And stay connected with Cisco DevNet on social!
Twitter @CiscoDevNet | Facebook | LinkedIn
Visit the new Developer Video Channel





Great blog, Chris! Exciting things happening in Security! Many thanks to you and Veer for ensuring the community has a video series to learn all about the Umbrella APIs! Looking forward to your session at Cisco Live Barcelona on the Threat Hunting APIs.
Awesome Blog Chris!