Apache has released a new update for Log4j, version 2.16.0. While the previous release (2.15.0) removed the ability to resolve lookups, and addressed issues to mitigate CVE-2021-44228, this release disables JNDI by default and removes support for message lookups.
Please see the Cisco Talos site for updated and evolving coverage on Log4j
Automating Cisco PSIRT critical alerts via Cisco SecureX and Webex Teams
In this blog post we will cover a SecureX automation that can help security operations (DevSecOps) teams to be alerted when a new Critical Impact Security Advisory is published (or updated) from Cisco PSIRT. A good example has been the recent Log4j library causing a vulnerability for some software around the world (including many Cisco products). Let’s break it down first…
What is Cisco PSIRT?
The Cisco Product Security Incident Response Team (PSIRT) is a dedicated, global team that manages the receipt, investigation, and public reporting of security vulnerability information that is related to Cisco products and networks. PSIRT has over 20 years of experience helping to alert customers about vulnerabilities in Cisco products.
What is Log4j and why are PSIRT Alerts more important than ever for Cisco customers?
Apache Log4j is a Java-based logging utility and is part of the Apache Logging Services, a project of the Apache Software Foundation. Log4j is one of several Java logging frameworks. Logging is extremely important for developer teams, since it can record the activity of an application, which can be used for many purposes, including debugging, performance improvement and auditing/compliance. Logging frameworks make it easier for developers to standardize this process. The good thing is that using a logging service negates the need to explicitly output to a console, and also that the storage of the logs becomes independent of the code and can therefore be customized at runtime.
On Thursday, December 9, the Apache Software Foundation disclosed a security vulnerability in a widely-used Java software library called Log4j. This vulnerability is referred to as a zero-day exploit because it was shared with everyone at the same time — the public, vendors, customers — on Twitter along with software code (referred to as exploit code) to take advantage of this bug and infiltrate an affected product.
Log4j is open-source software, which means that it can be used freely around the world by software developers, including at Cisco. PSIRT is the single entity authorized within Cisco to disclose vulnerability information to customers. It is therefore especially important to keep track of their critical alerts.
How can we automate the PSIRT critical alerts?
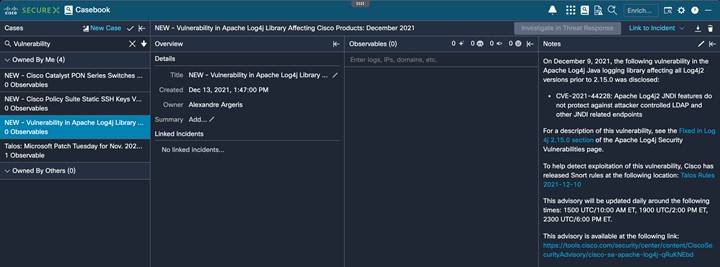
Alexandre Argeris has built a magnificent new SecureX orchestration (SXO) workflow. The workflow (i.e. playbook) fetches Critical Impact Security Advisories from the past week from Cisco PSIRT API, scheduled every hour. If there are any new advisories, or if an existing advisory is updated, a SXO table is updated, a SecureX Casebook is created and optionally a Webex notification is sent.
Automating this, enables SecOps teams to quickly see when there is either a new PSIRT alert, or when one is updated. Updates can sometimes contain crucial information that must be reviewed. It is important to stay up to date with these advisory updates (especially with wide-spread zero-day exploits like Log4j), to minimize the chance of a cyber-attack to your organization.
If you want to see a demo of this cool automation, check this video from Alexandre Argeris! Below is a screenshot of the Casebook being created in SecureX:
This is the v0 version of our workflow, with many cool features to come! We hope it will inspire others to build similar cool integrations using the Cisco PSIRT API and SecureX orchestration. Please find detailed instructions to install this workflow here. Enjoy and stay safe!
Need more information?
Now since the Log4j vulnerability is top of mind for many DevSecOps teams, we want to make sure you have access to the latest information. Please find that below:
- Read the full Cisco Security Advisory
- Review the Event Response page and FAQ
- Find the latest updated Talos Threat Advisory
- Review the Cisco blog post with guidance for software developers
- Review Cisco’s Security Vulnerability Policy
- Watch a short video tour of Cisco SecureX
Stay connected with Cisco DevNet on social!
Twitter @CiscoDevNet | Facebook | LinkedIn
Visit the new Developer Video Channel




