When working on code to share with our DevNet Community, one thing I always ask myself is, “what’s the best way to secure my API keys?” I can’t tell you how many times I’ve shared code that contains private sandbox credentials onto GitHub. And, as you know, once it’s on GitHub the only way to get rid of it is either by deleting traces of it (rebasing), or by deleting the entire repo and starting from scratch! The Internet never forgets!
I’ve also realized, while working as part of the team that put together the competency
exam for DevNet Partner Specialization, that the partners are expected to properly handle API Token security. Which got me thinking, there has to be a better way to do this properly!
Hide Yo Creds, Hide Yo Token
There are some best practices when it comes to securing your API keys.
- Do not embed API keys directly in code
- Do not store API Keys in files inside your application’s source tree
- Regenerate your API keys periodically
Managing all of this can be tedious. Sure you can have a flat file to house your token and import it as you need in your code, but that’s not very secure either.
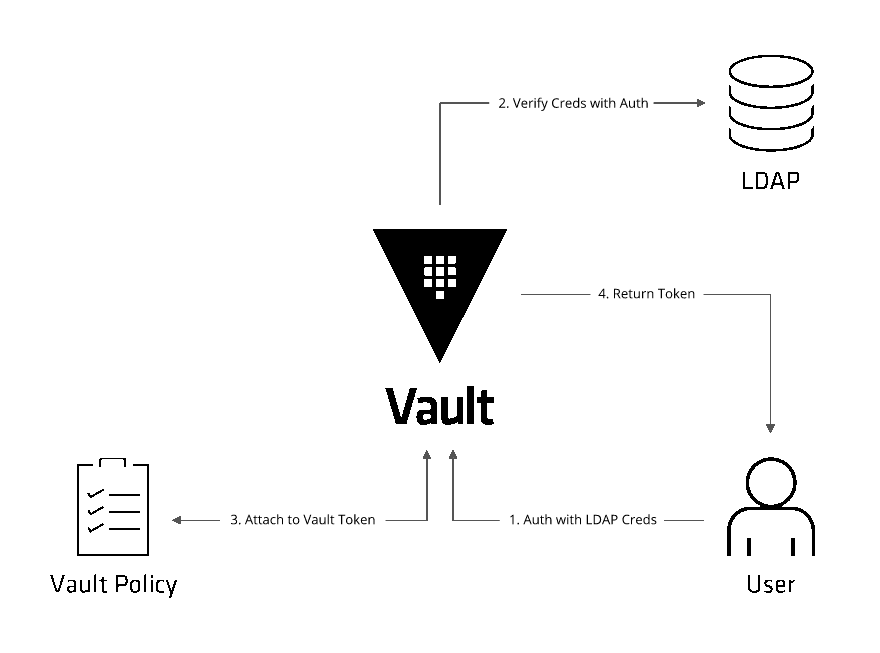
This is where Hashicorp Vault comes into play.

What is Vault?
Vault is a tool for securely accessing secrets. A secret is anything that you want to tightly control access to, such as API keys, passwords, or certificates.
How do I get started?
I’m glad you asked. I’ve put together a quick and easy guide on how to integrate Vault within your code. Head over to DevNet Automation Exchange and see the code in our DevNet Code Exchange.
To make things simple for you in the guide you will find:
- Postman collection and environment variables that get you up and running in no time.
- Sample code to get you started with vault and Cisco DNA Center SDK
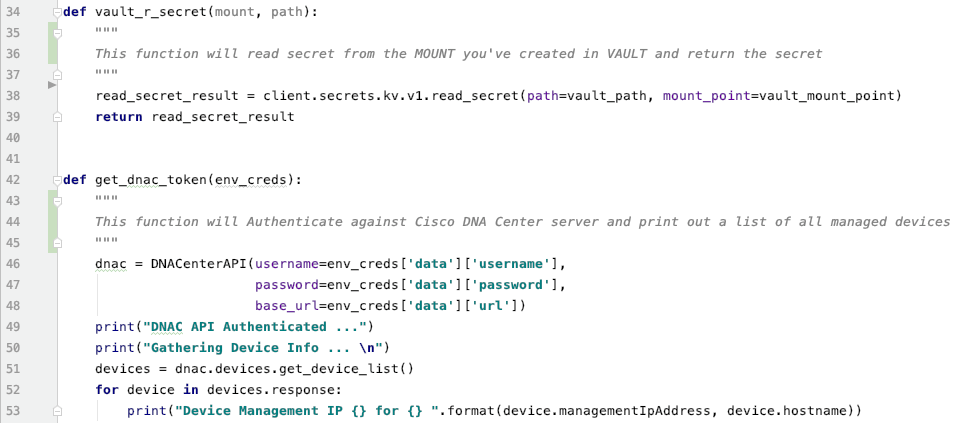
Even though I’m using Vault against Cisco DNA Center APIs, Vault can be used with any product.
I know I’ve learned a lot in the process, and I look forward to seeing what you’ve done with this. so please leave me a comment on this blog, or tag me on twitter. I’m curious to hear your feedback!
We’d love to hear what you think. Ask a question or leave a comment below.
And stay connected with Cisco DevNet on social!
Twitter @CiscoDevNet | Facebook | LinkedIn
Visit the new Developer Video Channel





Thank you, Kareem!
Learning so much about #CiscoDNACenter from you.
https://www.youtube.com/watch?v=OWy5YzWGP0M&list=PL2k86RlAekM-mHZ5Kr2DthHhaoEdfALFc&index=67