Un-boring new employee on-boarding
“A good start is a half win.” Or so they say. So why do we keep losing time on it? In onboarding a new employee, IT administrators typically hop between configuration pages to provision the right accounts and licenses, while constantly circling back to directory information and/or the employee themselves for their birth date, address, or phone number. All before even knowing important stuff, like how they like their coffee! At the other side of the hassle, a new employee’s first week is usually filled with the headache of laptop set-up, memorizing their credentials to different tools, and making sense of the instructions scattered across IT administration e-mails. All before even sharing a coffee with their new colleagues!
Solution description
The rising popularity of automation, scripting, and programmability is often focused on streamlining just one of these tasks, such as the setup of an employee’s Meraki stack, or fetching Active Directory information for e-mail account setup. However efficient those separate tasks become, it serves to keep in mind the extended workflow they sum up. If a single click can be enough to set up either a Webex account or an IP phone, why not both? Taking advantage of Cisco’s cross-architecture portfolio, made up of products that all have powerful programmability features, we created a portal for IT administrators to set in motion all onboarding tasks from a single place.
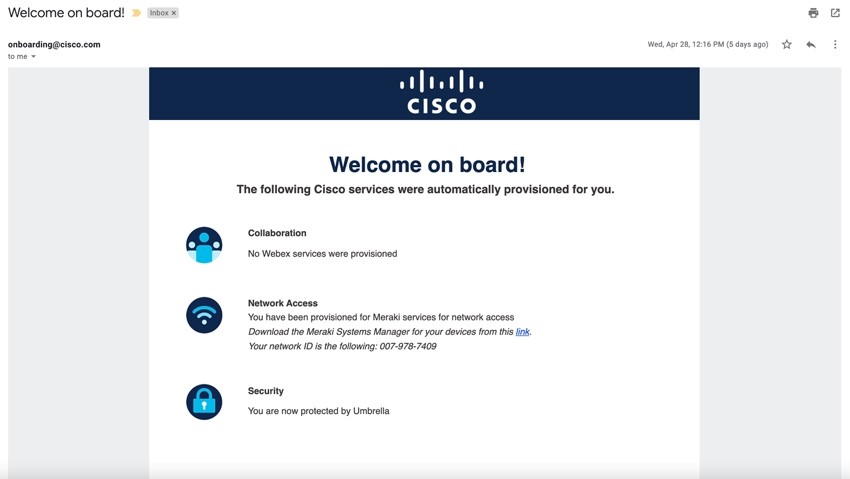
As far as the new employee goes, their brand new mailbox gets just one entry holding all credentials, instructions, and links they need to hit the ground running.
Cross-architecture automation
With the portal in its current status, the team combined Cisco automation features across three domains: security, network access, and collaboration. As a result, the portal can perform following actions, and inform the new employee on their corresponding outcomes:
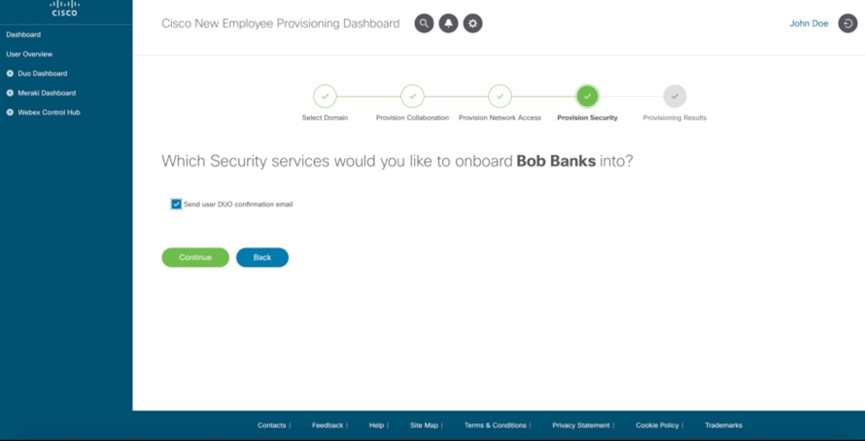
Security
- User account creation in Duo using the Duo Client SDK
-> Employee is provided with a link to download Duo Mobile application
Network Access
- Retrieval of network connectivity information
-> Employee receives network code to connect to corporate network
Collaboration
- User creation in Webex using the Webex Admin API
Employee is provided with a link to download the Webex App - License provisioning in Webex using the Webex Admin API
- Webex video endpoint provisioning using the Webex Device API
Employee receives a 16-digit device activation code - IP phone provisioning using the Cisco AXL SDK ()
Employee’s IP phone shows their name, and is provisioned with an extension
Evidently, each business however uses a different toolset – and therefore has its own set of tasks in onboarding new staff. Therefore, the portal is built with extensibility, customizability, and maintainability in mind. Concretely, the portal backend presumes no specific toolset, and is built such that (non-) Cisco product integrations can easily be added, removed, or updated according to a business’ needs.
To illustrate how the current set of tasks comes together, and allows for being tailored to a specific business, the code snippet below shows part of the provisioning script as executed in the portal’s backend. In short, it receives information from the portal’s frontend (i.e., its interaction with an IT administrator) on which products to provision, then it calls other modules to execute the appropriate tasks, and finally it sends an e-mail to the employee holding the information gathered in executing the different onboarding tasks, as well as reports back to the portal on the status of each task.
@app.route(‘/provision-user, methods=['GET', 'POST']) def provision_user(): # Parse requested services user_items = request.get_json(force=True)["user-products"] # Provision collaboration + network access services … # Provision security services if (len(user_items["Security"]) > 0): duo_user_id = security.get_duo_user (user_info) if (duo_users_id == "Null"): security.create_users_duo(user_info) status_message["Security"] = ["User was provisioned for Duo”] else: status_message["Security"] = ["User already exists in Duo"] # Email the employee email_employee.emailEmpl(user_info['email'], status_message) # Status report to the portal (IT administrator) return json.dumps(status_message)
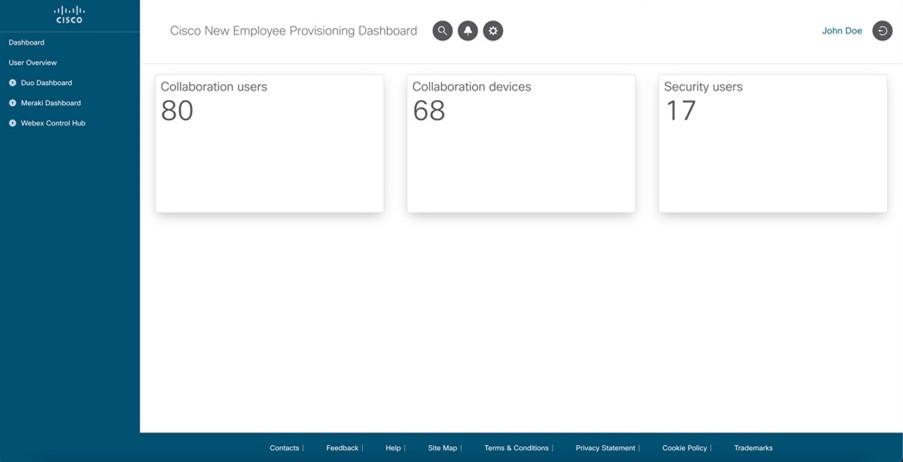
In addition to these automations, the portal also uses the programmability interface of Cisco products for gathering data about the toolset currently in use. For example, it shows the amount of users currently enrolled in an enterprise’s Webex Control Hub, as well as the amount of Duo users currently active. In a very similar way as shown above, and therefore with the same level of modularity/extensibility, the code snippet below illustrates how dashboard data is gathered from different modules, and reported back to the portal.
@app.route(‘/dashboard-data’) def dashboard_data(): dashboard_info = {} dashboard_info['no_collab_users'] = collab.collab_dashboard_info() dashboard_info['no_collab_devices'] = collab.device_dashboard_info() dashboard_info['no_duo_users'] = security.duo_dashboard_info() return json.dumps(dashboard_info)
Active Directory integration
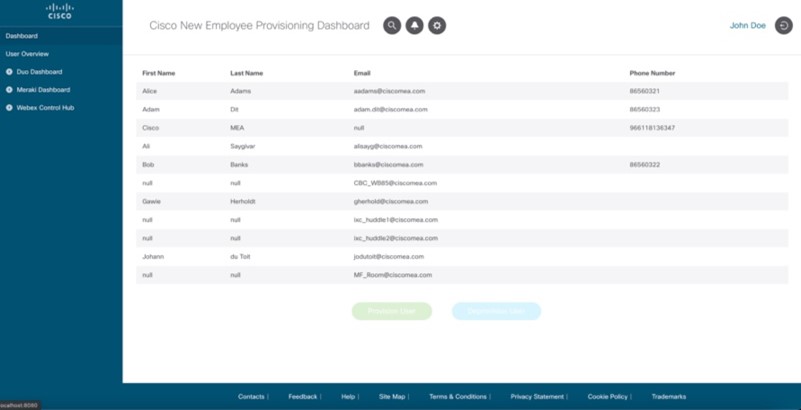
In interacting with different Cisco products, the portal often re-uses the same employee information like their name, phone number, and corporate e-mail address. With the portal holding all onboarding tasks in the same place, that information only needs to be retrieved from Active Directory once, before being fed to the separate automations simultaneously. Hence, we built an Active Directory integration into the portal for making all information fetching transparent to the IT administrator.
To integrate with Azure Active Directory, an application first needs to be created in the Azure dashboard, which involves generating credentials for authentication from the portal backend. Microsoft provides an Office 365 SDK for easy authentication from Python code to Azure Active Directory, which in its turn provides a REST API for fetching user information. Below, a code snippet illustrates the process.
# Import O365 SDK, requests library, environment variables from O365 import Account import requests from .env import config # Use the O365 SDK for app authentication def fetch_azure_users(): credentials = (config['app_id'], config['secret']) scopes = ['User.Read.All'] account = Account(credentials, auth_flow_type='credentials', tenant_id='XXXX’) if account.authenticate(): with open('o365_token.txt', 'r') as fobj: data = json.load(fobj) config['access_token'] = data["access_token"] # Use the Azure AD REST API to fetch user data url = "https://graph.microsoft.com/v1.0/users" payload={} headers = { 'Content-Type': 'application/json', 'Authorization': f"Bearer {data['access_token']}" } response = requests.request("GET", url, headers=headers, data=payload) # Parse and return response data result = [] for user in response.json()['value']: result.append({ "fname" : user['givenName'], "lname" : user['surname'], "email" : user['mail'], "mobilephone" : user['businessPhone'] }) return result
Technical aspects of the solution
Combining the components discussed above, the portal delivers an interface for IT administrators to:
1. Select an employee to provision from a list retrieved from Azure Active Directory
2. Select the Cisco products to provision for that specific employee
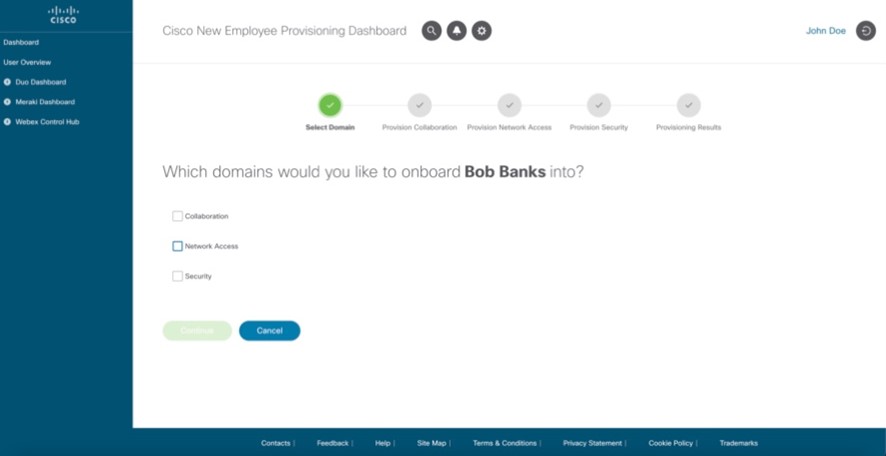
3. Set in motion the automation tasks for the product selection
4. Check on the success/failure of each automated provisioning task
5. Automatically alert the employee of the credentials, instructions and links they need to carry out the rest of the onboarding process
Conclusions + possible other use cases
With this employee onboarding scenario, we showed how Cisco programmability features are more than a sum of their parts. By consolidating automation features across the security, network access, and collaboration architectures, our portal takes away the mutual headache of IT administrators and new staff in the onboarding process – and replaces it with the friendly coffee machine banter you actually need to ease into a new job.
Useful Links
- Project on DevNet Code Exchange
- Live portal demo (needs VPN)
- Demo video
- DevNet Networking Resources Dev Center
We’d love to hear what you think. Ask a question or leave a comment below.
And stay connected with Cisco DevNet on social!
Twitter @CiscoDevNet | Facebook | LinkedIn
Visit the new Developer Video Channel




