It’s time to adopt Infrastructure As Code methodologies
With a projected 500 million apps coming online in the next 3 – 5 years, Enterprise I&O (Infrastructure & Operations) no longer have an option but to move towards programmable infrastructures (PI). This move from ClickOps and ITIL to PI is imperative for I&O to match the pace of application developers in the agile delivery of their cloud native applications. Enterprise I&O organizations that are on a path to delivering PI, realize the importance of replacing their legacy ClickOps and ITIL (traditional I&O service management lifecycle) methodologies. Adopting Infrastructure As Code methodologies allows I&O to view the delivery of infrastructure services as yet another software project and leverage the same best practices of application developers.
HashiCorp Terraform For IaC
While there is a myriad of Infrastructure As Code (IaC) tools in the marketplace, there has been a wide adoption of HashiCorp’s Terraform solution mainly due to its cloud agnosticism, extensibility, and support for pretty much any solution that supports an API. The catalog of Terraform Providers is fast growing and now stands at approximately 800 with close to 5000 modules that can be leveraged by Enterprise I&O for orchestration of their infrastructure services .
Many Enterprises adopting Terraform for IaC have typically leveraged HashiCorp’s open-source offering, Terraform OSS. And similar to many open-source products, these implementations often require bespoke and complex scaffolding to make the product “enterprise-ready”.
However, with access control, state management and native integrations with CI/CD pipelines, Terraform Cloud Business makes it a lot easier for I&O to adopt IaC without the need for such custom scaffolding. For example, some of the features that Terraform Cloud Business provides that is missing from the opensource offering are:
- Team management & governance
- Advanced security, compliance and governance (SSO & audits)
- Performance, scale, and remote connectivity (cloud agents)
- Secrets management and access to Policy As Code engine
Cisco Intersight Service for HashiCorp Terraform (IST)
Intersight Service for HashiCorp Terraform (IST) is a new Intersight service offering announced jointly by Cisco and HashiCorp. IST integrates Intersight (IS) and Terraform Cloud Business (TFCB), bringing together two flagship products into a single end-to-end, hybrid cloud, IaC solution. The integration of Cisco Intersight Assist and HashiCorp Terraform Cloud agents in the private datacenter addresses the challenge of securely connecting and configuring on-premises environments. Such a tight integration greatly simplifies hybrid cloud operations for I&O.
Let’s address a use case to deploy VM’s on a vSphere Infrastructure using IST. We will address the provisioning here with TF Cloud UI (with ClickOps). Please watch out for subsequent blogs that will address the same provisioning to show case the end-to-end programmability using Intersight API’s.
Try it yourself… Go to the hands-on lab to explore this initial use case.
The following assumes that you have an Intersight account with privileges to create Targets and TFCB account with privileges to create workspaces and plan/deploy TF Runs. Also, Intersight Assist with TFCB Cloud Agent should be installed and connected to your on premise vSphere deployment.
These are the steps to provision your first infrastructure service leveraging IST:
- Setup your workspace in TFCB (connect to your VCS containing Terraform HCL for VM Provisioning, set up variables for vSphere access, connect to TFCB cloud agent on premise)
- Setup Intersight Targets for your private datacenter (Intersight Assist, Terraform Cloud Agent, Terraform Cloud)
- Execute Terraform Plan and Deploy for VM(s) Provisioning in TFCB
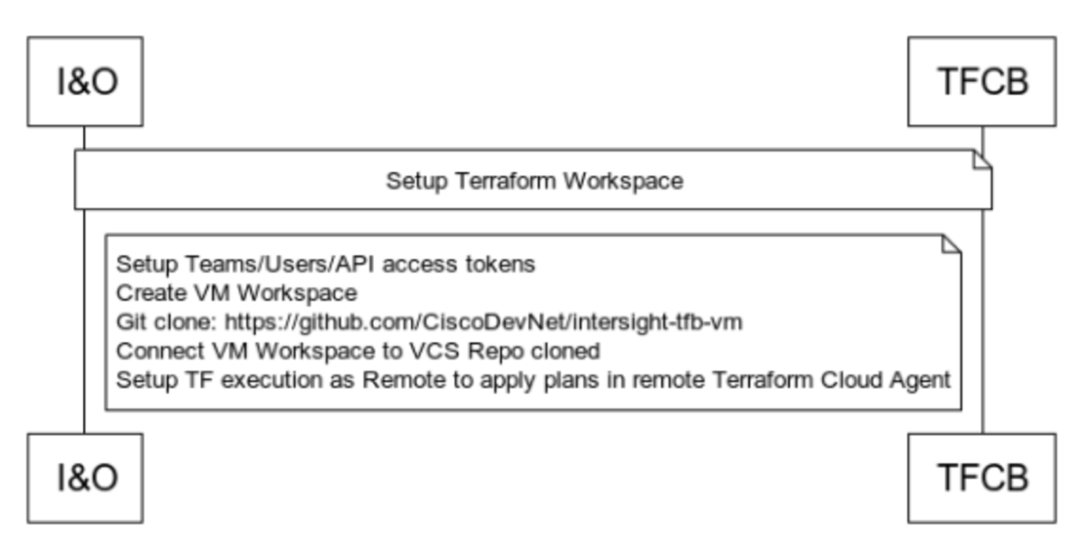
Setup your workspace in TFCB (https://app.terraform.io/)
Setup Intersight Targets for your private datacenter

Execute Terraform Run for VM(s) Provisioning
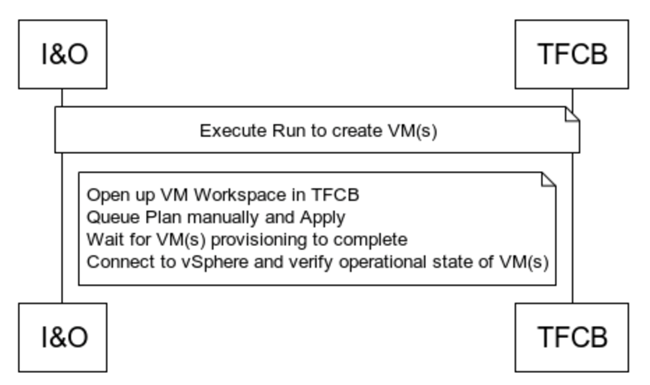
Behind the Scenes…
Following highlights the value add of Intersight and TFCB integrations in simplifying and securely provisioning private cloud resources such as VM(s). The interactions are self-explanatory but would like to highlight the role of Intersight Assist in providing a secure channel between remote TFCB cloud agents and TFCB:

Additional Resources
- Explore Cisco’s IaC tools, learning labs, and sandboxes
- GitHub repo for the VM Provisioning Terraform configuration files
- vSphere Terraform Provider
- Sample sandbox
We’d love to hear what you think. Ask a question or leave a comment below.
And stay connected with Cisco DevNet on social!
Twitter @CiscoDevNet | Facebook | LinkedIn
Visit the new Developer Video Channel

CONNECT WITH US