It is all about security, isn’t it? Take every other customer survey and ‘security’ bubbles up at the very top of most respondents’ concerns. One of the latest data points I can share is part of an IDC cloud study in which security was cited as an important concern. In fact, 48% of respondents are characterizing security as an important inhibitor to cloud deployments (if you want to learn more about the study you can find the details in my previous blog).
Security Versus Risk Management
As always, under the word ‘security’ most organizations we talk to include a lot more than just security. In fact, if you begin to discuss the topic, additional connotations do surface including and not limited to industry or state laws and regulations such as data sovereignty. Other organizations are quite concerned about data privacy and data leak protection. It would appear that cloud can only amplify these concerns while increasing complexity. And the scope goes well beyond the cloud to include edge and IoT solutions, which dramatically expand the ‘attack surface’ and overall risk.
If we step back, ultimately senior business and IT decision makers seek to minimize ‘business risk’ – while driving the business forward – and security is part of that. Business risk includes all of the above plus business continuity, contingency plans, guaranteed SLAs from cloud service providers, vendor selection risk mitigation strategies and more.
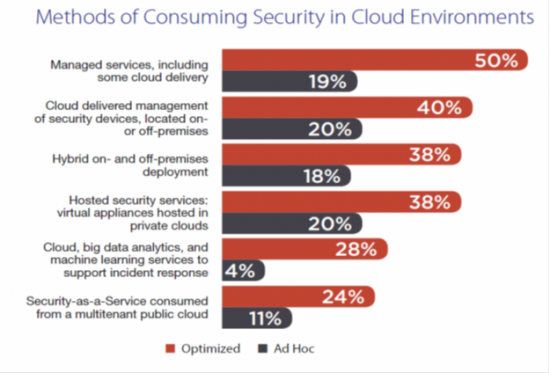
Source: IDC InfoBrief “Cloud Going Mainstream. All Are Trying, Some Are Benefiting; Few Are Maximizing Value”
Security in Cloud Environments
In light of all of this, what seems counterintuitive is a good level of positive correlation between cloud ‘maturity’ and the ability of organizations to consume cloud-based security services. In fact, the IDC study revealed that one approach favored by mature cloud organizations is to consume security services ‘from the cloud’, through methods such as cloud-delivered management of security services, and hosted security services (see chart above).
Many of our customers want to consistently enforce security policies where services and applications are deployed, beyond the data center to include multicloud environments and the edge. This is why we talk about Security Everywhere. With our growing security portfolio we can offer security solutions for the cloud and from the cloud. We focus on three major areas:
- Helping you keep valuable data more secure- Extend data center performance to increase uptime. Control access to your data center, and limit how data is handled. Protect your resources: physical, virtual, and cloud.
- Protecting apps and data in the cloud – Integrate security across all cloud deployments. Deploy security solutions easily across all environments. Gain consistent protection, removing vulnerable coverage gaps.
- Promoting secure access anywhere – Connect new users and devices quickly with the right access. Maintain protection of remote users and devices automatically. See into user behavior and device status.
Cisco Umbrella
For example, many of our customers use Cisco Umbrella: a cloud security platform that provides the first line of defense against threats on the internet. Because Umbrella is delivered from the cloud, it provides the easiest way to protect all of your users in minutes. One of the capabilities we offer is the ability to leverage cloud-based insights on a global scale to prevent security attacks instead of just responding to them. By implementing a cloud-delivered security service possessing predictive capabilities, you can block phishing attempts, bespoke malware, and other evolving threats from the moment attackers start spinning up their attack infrastructure.
Cisco CloudLock
Another solution deployed by over 700 organizations worldwide is CloudLock. There are simple questions we hear from our customers every day:
- How do I protect the application and infrastructure that I buy?
- How do I protect the applications that I build?
- How do I leverage security solutions that I’ve already purchased?
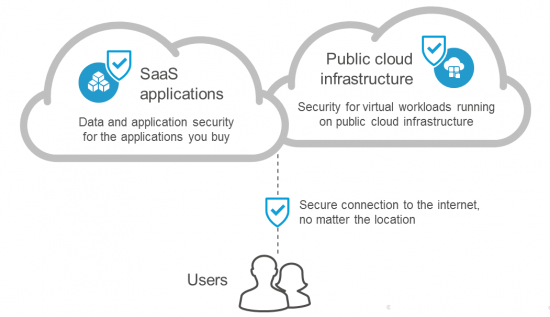
Protecting any cloud application and platform, CloudLock secures SaaS, IaaS, and PaaS environments, and provides unparalleled coverage of cloud traffic, including on- and off-network, retroactively and in-real time. Watch this fun video for real life examples.
Cloud Lock consists of the following three key components:
- Cloud Data Security & Compliance – CloudLock protects organizations against data breaches in any cloud environment through a highly-configurable Cloud Data Loss Prevention (DLP) engine providing excellent coverage of cloud traffic.
- Cloud User Security – CloudLock defends against account compromises with cross-platform User and Entity Behavior Analytics (UEBA) for SaaS, IaaS, PaaS, and IDaaS environments. CloudLock uses advanced machine learning to detect anomalies in account usage, in addition to identifying activities outside of whitelisted countries and actions across distances in an impossible amount of time.
- Cloud Application Security – The CloudLock Apps Firewall discovers and controls malicious cloud applications connected to your corporate environment, and provides the world’s largest crowd-sourced security solution to identify individual application risk, using our Community Trust Rating.
In summary, when it comes to security you can see how cloud-native security solutions delivered from the cloud can indeed lower your overall business risk. Security is a real concern, but you can take steps to mitigate risks across a number of dimensions.
To learn more about our capabilities to deliver security solutions for the cloud and from the cloud you can refer to the list of resources that I included below.
- Learn more about Cisco BCA Cisco Business Cloud Advisor Website
- Determine where you are in your multicloud journey, get the IDC Report Cisco BCA Adoption Report
- Learn more about our security portfolio Cisco Cloud Security Website
- Learn more about our cloud website Cisco Cloud Website



