The VP of Data Center Operations at a B2B cloud provider cannot guarantee that his enterprise customer’s sensitive records are protected from attacks — even with his arsenal of threat detection and mitigation tools. Amongst rows of opaque racks with thousands of consolidated workloads, he cannot fully catalog the vulnerable machines nor the processes running on them, nor the data bases they are accessing, nor their owners.
This is the irony of Digital Transformation is — that its actually making many data center operational tasks harder. We see three broad causes.
- First, there is too much new or transient traffic due to the rising internal bandwidth, new Hadoop workloads and many more endpoints including micro-services and containers. Over 70% of data center traffic is internal and growing.
- Second, there is business pressure to move applications to new resources with security – to hybrid clouds, programmable networks, hyper-converged infrastructure or, simply, to fewer data centers (as in the case of a merger). How do architects and security admins know what dependencies to move with the application or whether they can trust the flows on newly consolidated resources.
- Third, the rapid dev-to-deploy cycles for applications is outpacing compliance and audit controls, in addition to creating production instability. For example, we see large development teams inadvertently mis-applying communication policies in the process of re-using them resulting in major compliance violations and vulnerabilities.
In each case, digital transformation promises high agility and ROI but the actual “transforming” journey is fraught with risk. The root cause is the lack of real-time, actionable visibility in increasingly dynamic environments. We see this in every enterprise but particularly in regulated industries, such as service providers, financial services, healthcare and government agencies.
Tetration Analytics delivers real-time, actionable visibility
Cisco Tetration Analytics was designed to see every activity in the data center, every flow, every packet coming from every source, going to every destination. Operations can instantly see traffic as its occurring, at line rate, and forensically analyze flows and packets a year in the past, with no loss of information. (watch video)
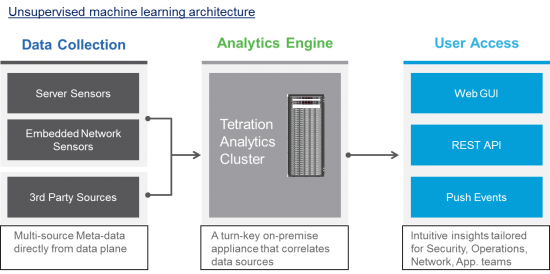
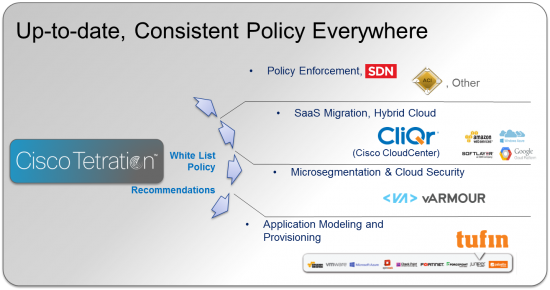
Deep visibility to all traffic enables Tetration to discover all the application policies and dependencies in real-time, even as they change in dynamic environments. This means you can see vulnerable machines, check compliance, maintain correct micro-segmentation and dramatically reduce the risk of application migrations. Tetration APIs enable export of consistent, up-to-date policies everywhere.
To see how Tetration does this and its key use-cases, watch my short video talk at CiscoLive Las Vegas.
For additional information link to www.cisco.com/go/tetration




Cisco Titration looks like an terrific digital asset, which could be a platform with a robust 3rd party application ecosystem built on it, accessed by secure APIs. I’d love to hear more about the 3rd party ecosystem.