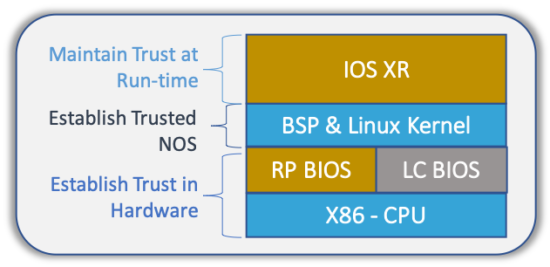
Service Provider networks serve as critical infrastructure, and the security and trustworthiness of the network infrastructure is essential, as explained in both Sumeet’s blog and the Trusted Infrastructure video from Mobile World Congress. Providers of digital infrastructure must be able to verify whether the hardware and software that comprise their infrastructure are genuine, uncompromised, and operating as intended. As shown in Figure 1 below, there are security and trust requirements at every layer of the Network Operating System. I will address each of these layers in this and a subsequent blog.
Note that not all the features listed here are available on all Service Provider platforms. Please contact the sales team for details.
Foundations of Trust
The ability to verify that a Cisco device is genuine and running uncompromised code depends on Cisco Secure Boot and Trust Anchor module (TAm). Cisco uses digitally-signed software images, a Secure Unique Device Identifier (SUDI), and a hardware-anchored secure boot process to prevent inauthentic or compromised code from booting on a Cisco platform.
Hardware Root of Trust
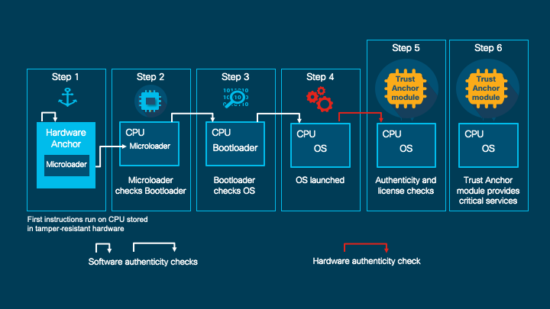
A trusted element in the scope of system software is a piece of code that is known to be authentic. A trusted element must either be immutable (stored in such a way as to prevent modification) or authenticated through validation mechanisms. Cisco anchors the root of trust, which initiates the boot process, in tamper-resistant hardware. The hardware-anchored root of trust protects the first code running on a system from compromise and becomes the root of trust for the system.
Trust Anchor module
The Trust Anchor Module (TAm) is a proprietary, tamper-resistant chip that features non-volatile secure storage, Secure Unique Device Identifier (SUDI), and crypto services including random number generation (RNG). See below for additional information on SUDI. See Cisco’s Trust Anchor Technologies for more information.
Image signing
Image signing is a two-step process that creates a unique digital signature for a given block of code. First, a hashing algorithm, similar to a checksum, is used to compute a hash value of the block of code. The hash is then encrypted with a Cisco private key, resulting in a digital signature that is attached to and delivered with the image. Signed images can be checked at runtime to verify that the software has not been modified.
Chain of Trust
A chain of trust exists when the integrity of each element of code on a system is validated before that piece of code is allowed to run. A chain of trust starts with a root of trust element. The root of trust validates the next element in the chain (usually firmware) before it is allowed to start, and so on. Through the use of image signing and trusted elements, Cisco hardware-anchored secure boot establishes a chain of trust which boots the system securely and validates the integrity of the software.
Secure Boot
Cisco Secure Boot helps ensure that the code that executes on Cisco hardware platforms is genuine and untampered. A typical UEFI-based boot process starts at the UEFI firmware and works up to the boot loader and the operating system. A tampered UEFI firmware can result in the entire boot process being compromised.
Using a hardware-anchored root of trust, digitally-signed software images, and a unique device identity, Cisco hardware-anchored secure boot establishes a chain of trust which boots the system securely and validates the integrity of the software. The root of trust (aka. microloader), which is protected by tamper-resistant hardware, first performs a self-check and then verifies the UEFI firmware, and thus kicks off the chain of trust leading up to the integrity verification of the entire IOS XR operating system.
Secure Unique Device Identifier (SUDI)
The SUDI is an X.509v3 certificate and an associated key-pair which are protected in hardware in the Trust Anchor module (TAm). The SUDI certificate contains the product identifier and serial number and is rooted in Cisco Public Key Infrastructure. This identity can be either RSA or ECDSA based. The key pair and the SUDI certificate are inserted into the Trust Anchor module during manufacturing, and the private key can never be exported. The SUDI provides an immutable identity for the router that is used to verify that the device is a genuine Cisco product, and to ensure that the router is well-known to the customer’s inventory system.
The SUDI-based identity can be used to perform authenticated and automated configuration using Zero Touch Provisioning (ZTP). A backend system can issue a challenge to the router to validate its identity and the router will respond to the challenge using its SUDI based identity. This allows the backend system to not only verify against its inventory that the right router is in the right location but also provide encrypted configuration that can only be opened by the specific router, thereby ensuring confidentiality in transit.
Secure Storage
Cisco’s Trust Anchor technology provides a mechanism to securely store secrets on the router. The encryption of the storage space is tied to the hardware root of trust, and data cannot be decrypted without the specific hardware that was used to encrypt it. The secrets that can be stored include user passwords, customer credentials for authentication protocols such as RADIUS or TACACS, customer certificates, and any type of keys.
The combination of SUDI-based ZTP and secure storage provide very strong protection of customer configuration and secrets.
Hardware Fingerprint
Tampered hardware, particularly in transit, is a clear vector of attack. This is especially a concern when the hardware is in transit from Cisco to our customers and partners; or when a Service Provider ships their router from a holding center to the deployment center. A malicious agent can intercept the hardware in transit and tamper the hardware in a non-detectable manner.
Cisco’s Hardware Fingerprinting technology provides the ability to detect tampered hardware using the Trust Anchor. Cisco fingerprints the critical hardware elements of a router, such as CPUs and ASICs, during manufacturing and stores the fingerprint in the tamper resistant Trust Anchor. This fingerprint is not only immutable once it is inserted into the Trust Anchor but it also cannot be read back from the Trust Anchor.
When the router boots up, UEFI firmware fingerprints the hardware elements of the router at boot and creates a fingerprint of the hardware elements. This fingerprint is sent to the Trust Anchor hardware, which will compare it against the master fingerprint stored inside the hardware. UEFI firmware will only boot the router if the Trust Anchor hardware can successfully verify the observed fingerprint at bootup against the master fingerprint.
As threats evolve, Cisco continues to enhance the security and resilience of our solutions. While no vendor can guarantee security, we are committed to transparency and accountability and to acting as a trusted partner to our customers to address today’s, and tomorrow’s, security challenges.
In the next blog, I will look at the Security and Trust controls introduced in the IOS XR Software. For more information check out how to build Trusted Infrastructure.





Very informative content !!