Providing secure access and a frictionless user experience are typically competing initiatives, but they don’t have to be! Read on to learn why.
In our world today, context changes quickly. We work from home, coffee shops and the office. We use multiple devices to do work. And on the flip side, attackers are becoming increasingly savvy, getting around security controls, such as multi-factor authentication (MFA), to gain unauthorized access.
To quote Wendy Nather, Cisco’s head of Advisory CISOs, “Trust is neither binary nor permanent.” Therefore, security controls must constantly evaluate for change in trust, but without adding unnecessary friction for end-users.
It’s no surprise that the recently published Cybersecurity Readiness Index, a survey of 6,700 cybersecurity leaders from across the globe, revealed that more progress is needed to protect identity, networks and applications.
To address these challenges and to make zero trust access for the workforce easy and frictionless, Cisco Duo announced the general availability of Risk-Based Authentication and enhancements to our enterprise ready Single Sign-On solution at Cisco Live EMEA 2023 earlier this week.
Risk-Based Authentication
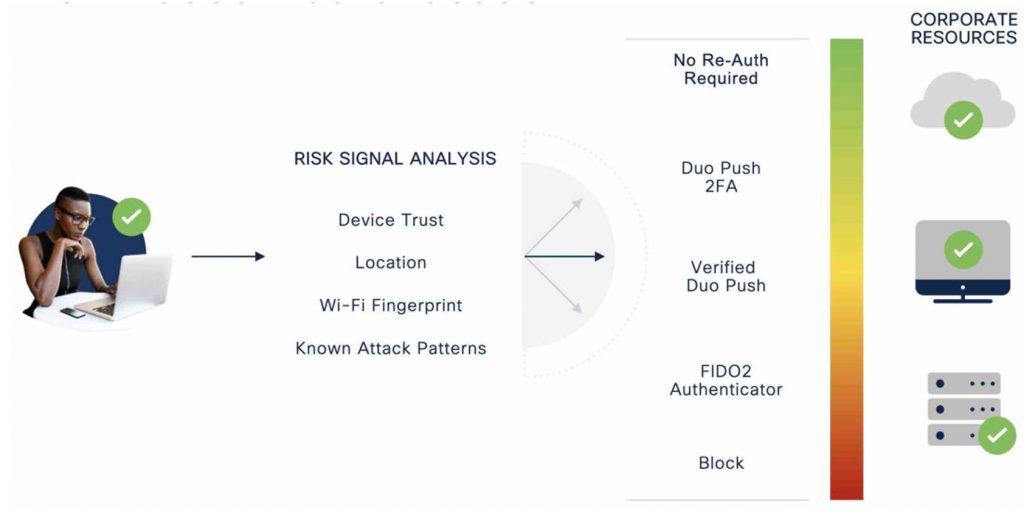
Risk-Based Authentication fulfills the zero trust philosophy of continuous trust verification by assessing the risk level for each access attempt in a manner that is frictionless to users. A higher level of authentication is required only when there is an increase in assessed risk. Duo dynamically detects risk and automatically steps up authentication with two key policies:
1. Risk-Based Factor Selection
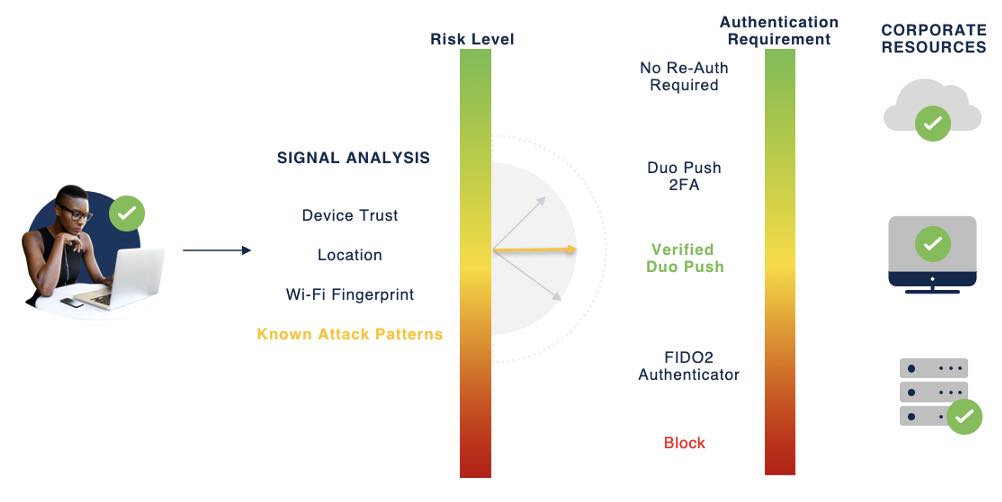
The Risk-Based Factor Selection policy detects and analyzes authentication requests and adaptively enforces the most secure factors. It highlights risk and adapts its understanding of normal user behavior. It does this by looking for known attack patterns and anomalies and then allowing only the more secure authentication methods to gain access.
For example, Duo can detect if an organization or employee is being targeted for a push bombing attack or if the authentication device and access device are in two different countries, and Duo responds by automatically elevating the authentication request to a more secure factor such as phishing resistant FIDO2 security keys or Verified Duo Push.
2. Risk-Based Remembered Devices
The Risk-Based Remembered Devices policy establishes a trusted device session (like “remember this computer” check box), automatically without asking the user the check a box, during a successful authentication. Once the session is established, Duo looks for anomalous IP addresses or changes to a device throughout the lifetime of the trusted session and requires re-authentication only if it observes a change from historical baselines.
The policy also incorporates a Wi-Fi Fingerprint provided by Duo Device Health app to ensure that IP address changes reflect actual changes in location and not normal usage scenarios such as a user establishing an organizational VPN (Virtual Private Network) session.
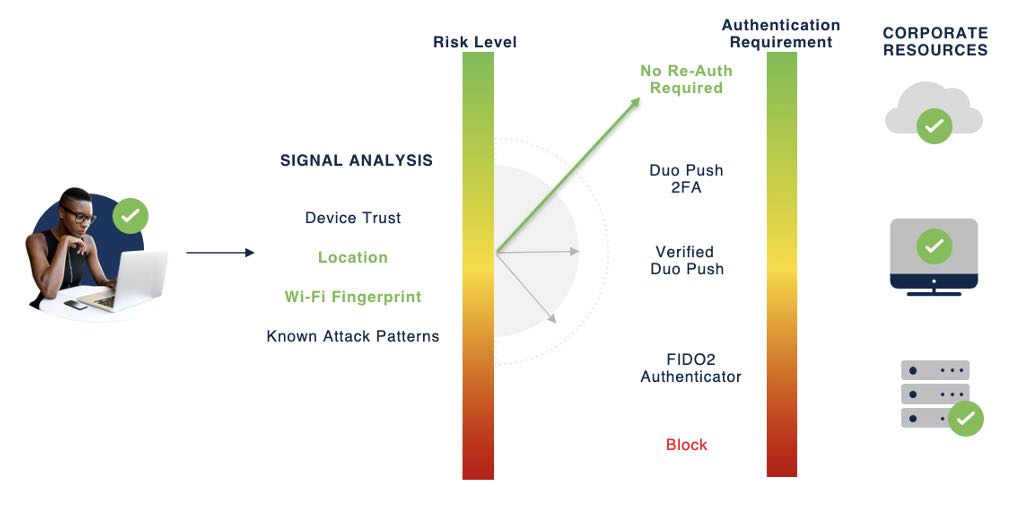
Duo uses anonymized Wi-Fi Fingerprint to reliably detect whether the access device is in the same location as it was for previous authentications by comparing the Wi-Fi networks that are “visible” to the access device. Further, Duo preserves user privacy and does not track user location or collect any private information. Wi-Fi Fingerprint only lets Duo know if a user has changed location.
Single Sign-On
A typical organization uses over 250 applications. Single sign-on (SSO) solutions help employees access multiple applications with a single set of credentials and allow administrators to enforce granular policies for application access from a single console. Integrated with MFA or passwordless authentication, SSO serves as a critical access management tool for organizations that want to implement zero trust access to corporate applications.
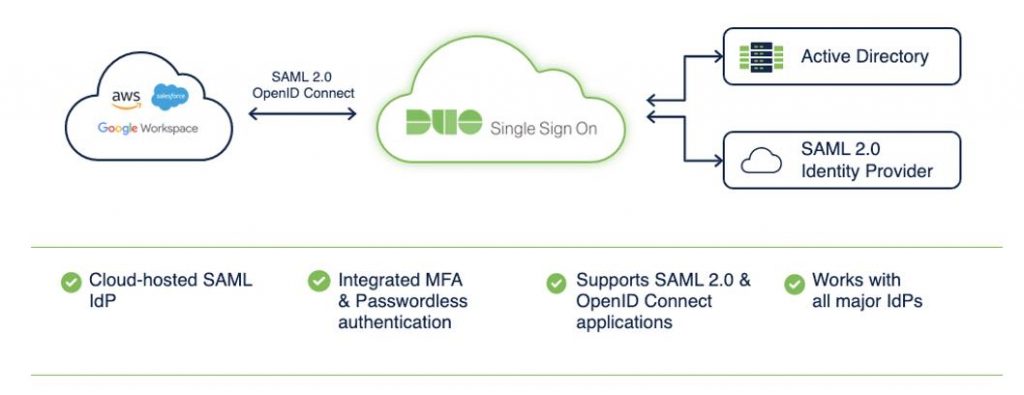
Duo SSO is already popular among Duo’s customers. Now, we are adding two new capabilities that cater to modern enterprises:
1. Support for OpenID Connect (OIDC)
An increasing number of applications use OIDC for authentication. It is a modern authentication protocol that lets application and website developers authenticate users without storing and managing other people’s passwords, which is both difficult and risky. To date, Duo SSO has supported SAML web applications. Supporting OIDC allows us to protect more of the applications that our customers are adopting as we all move towards a mobile-first world and integrate stronger and modern authentication methods.
2. On-Demand Password Resets
Password resets are expensive for organizations. It is estimated that 20-50% of IT helpdesk tickets are for password resets. And according to a report by Ponemon Institute, large enterprises experience an average loss of $5.2 million a year in user productivity due to password resets.
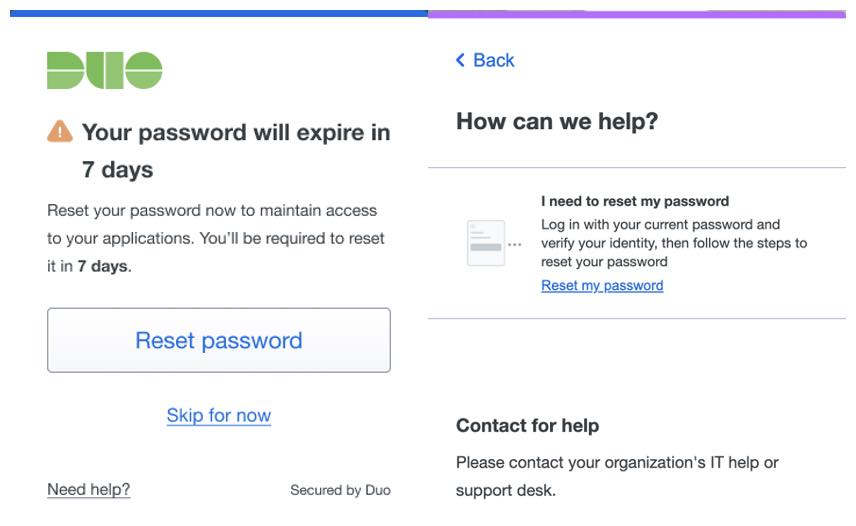
When logging into browser-based applications, Duo SSO already allows users to reset passwords when they have expired in the same login workflow. And we heard from our customers that users want the option to proactively reset passwords. Now, Duo SSO offers the convenience to reset their Active Directly passwords before they expire. This capability further increases user productivity and reduces IT helpdesk tickets.
Risk-Based Authentication and enhancements to Duo SSO are available now to all paying customers based on their Duo Edition. If you are not yet a Duo customer, sign up for a free 30-day trial and try out these new capabilities today!
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Instagram
Facebook
Twitter
LinkedIn


CONNECT WITH US