Enterprise network is undergoing digitization through multiple technological transitions that include explosion of connected and IoT devices in the network and the movement of applications and services to the cloud. Of the 29.3 billion networking devices that are forecasted to be seen in the network by 2023, 50% are expected to be IoT devices. Cloud based applications and services are expected to be accessed from multiple sites and locations, both on and off of the Enterprise network. These new trends and network transitions have not only increased the threat surface but also has advanced the sophistication of the attacks. Securing and protecting the Enterprise infrastructure has become top of the mind for network administrators and customers. With the advances and ratifications in the Wi-Fi standard, wireless has become the de facto standard of access technology in the Enterprise network. However, due to the inherent nature of the wireless networks, it becomes even more important to detect and protect not only the network infrastructure and users, but also to secure the air.
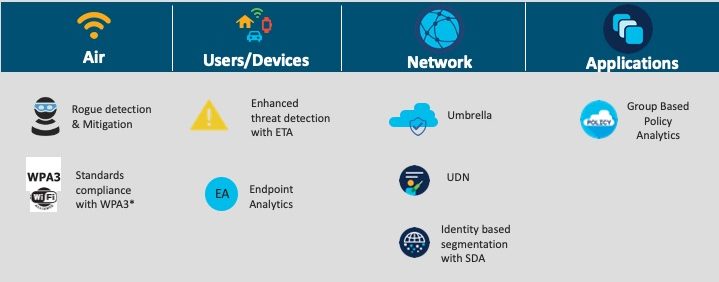
At Cisco, all solutions are built with end-to-end security in mind. In this blog, we discuss some of the security initiatives and solutions that play a role in securing the Enterprise wireless networks. These components form various pieces of the security puzzle addressing over the air security, infrastructure security and provide end-to-end visibility.
Securing the Air using Rogue Management and aWIPS Solution
Rogue management and Advanced Wireless Intrusion Prevention System (aWIPS) is a wireless intrusion, threat detection and mitigation mechanism that secures the air. Rogue management solution provides protection against AP impersonation, AP Mac spoofing, Honeypot and Rogue on wire. Auto/manual containment enables the attacks to be contained before the actual damage happens. Rogue and aWIPS together provides security against denial-of-service attacks, management frame attacks and tools-based attacks to name a few.
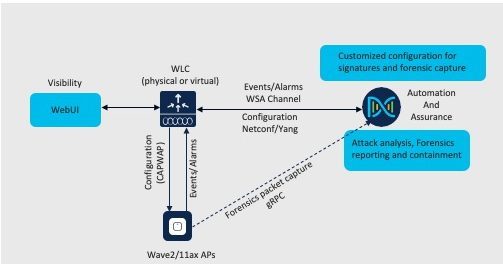
Rogue Management and aWIPS solution architecture comprises of:
- Access points: Monitors the air and detects threats using advanced configurable signature-based techniques
- Wireless controller: Configures the access points; receives aWIPS alarms and rogue information from the AP; does rogue classification and sends consolidated report to the Cisco DNA Center
- Cisco DNA Center: Provides simple and intuitive dashboard for configuration and customization of aWIPS and rogue rules. Cisco DNA Center also monitors, aggregates and consolidates events and alarms in a single pane of glass
In conjunction with Cisco DNA Center, users can customize the Rogue detection and management and also fine-tune aWIPS signatures and thresholds based on individual network needs. To meet compliance requirements and also for post-analysis of the attacks happening in the network, per-signature forensic packet capture knob is provided through Cisco DNA center. DNA Center aggregates, correlates and summarizes the attacks across the managed network on the unified Rogue management and aWIPS dashboard.
Device profiling with Endpoint-Analytics
As we embark the new wave of digital transformation, more and more devices (including IoT devices) are being added to the network. A malicious user in the network is just required to find a single vulnerable entry point in the network to breach and exploit the entire network. Once that is done, the threats can spread throughout the network from device to device in a matter of seconds. Such vulnerabilities in the network mandates granular network segmentation thereby preventing the lateral spread of threats. The first step towards achieving granular network segmentation is to identify and profile the devices and endpoints that are present in the network so that segmentation and other policies can then be enforced on these groups of devices.
Cisco AI Endpoint Analytics is the next-generation endpoint visibility solution. It gathers context from the network and enables the visibility of the endpoints to the administrator through “behavioral-based device classification”. Following techniques are used to achieve that:
- Deep packet inspection (DPI): uses enhanced NBAR technology to inspect and understand the applications and the protocols the endpoints are sending over the network to gather deeper context on the endpoint
- Machine Learning (ML): constructs for intuitive grouping of the endpoints which have common attributes
- Integration with Cisco and third-party products for additional context
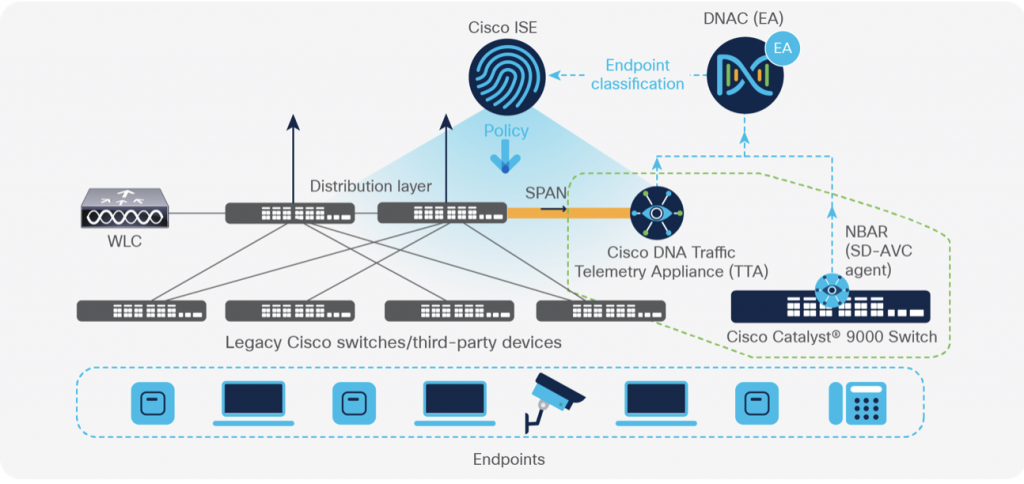
Cisco’s DPI based profiling capabilities is supported in Catalyst 9800 series Wireless Controller platforms. The controller does deep packet inspection and generates telemetry data to the DNA Center to perform analytics. This enables the users to group the endpoints for segmentation and policy enforcement.
Insight into Encrypted Traffic using Encrypted Traffic Analytics
The rapid rise in the encrypted traffic is changing the security landscape. A significant number of services and applications are using encryption as the primary method for securing information. As a result, malware detection using traditional flow monitoring techniques will no longer be feasible. Traditional way of inspecting the flows with decryption, analysis and re-encryption is not always feasible and also compromises on data integrity and privacy. Encrypted Traffic Analytics (ETA) provides insight into the encrypted traffic without decryption using passive monitoring. This insight enables us to identify and detect malware present in encrypted network connections.
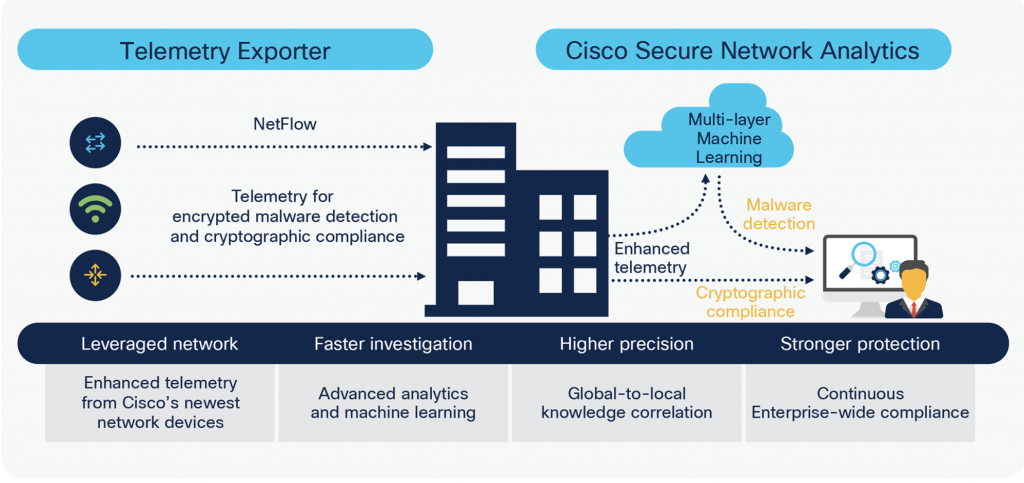
Encrypted traffic analytics (ETA) extracts four data elements: Initial data packet (IDP), sequence of packet lengths and times, byte distribution and TLS-specific features. These four data elements are embedded as vendor-specific data elements in enhanced Netflow records and are sent to Cisco Secure network analytics engine for further analysis. Secure network analytics analyzes these new data elements by applying machine learning algorithms and statistical modeling techniques to pinpoint malicious patterns in the encrypted traffic and help identify threats.
Cisco Catalyst 9800 Wireless Controllers support exporting of the enhanced Netflow records to security network analytics engine for further analytics and threat detection.
Securing the Network using Umbrella
Cisco Umbrella is a cloud delivered network security service that uses DNS queries to determine if traffic to a particular domain should be allowed, dropped or needs to be inspected further. Cisco Umbrella uses DNS to stop threats across all protocols and ports. It stops malware and attackers (in real time) if infected machines connect to the network. Cisco Umbrella uses evolving big data and data mining methods to proactively predict attacks and does category-based filtering.
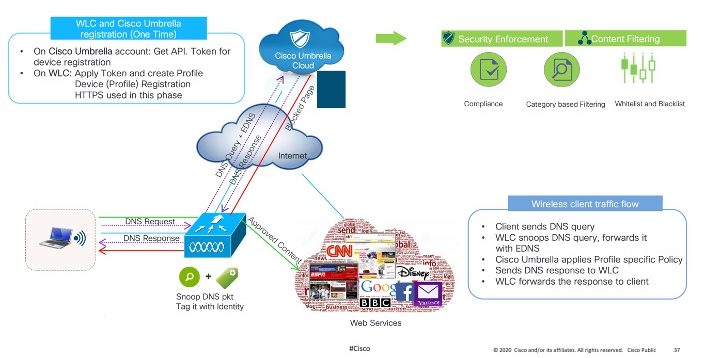
Cisco 9800 Wireless Controllers and Cisco Embedded Wireless Controllers (EWC) support Umbrella network security service. WLC intercepts the DNS requests from the clients and redirects the queries to the Cisco Umbrella server in the cloud, along with the identity. The Umbrella service resolves the query and enforces category-based filtering rules on a per-identity basis. Policies can be enabled on individual SSIDs with separate policy for each SSID.
Umbrella can be enabled using DNA center dashboard and can be actively monitored using simplistic statistics dashboard. Umbrella enables customers to block threats at DNS layer and secures endpoints and users.
Nano Segmentation with User-Defined Network
Wireless being a shared network, there is no easy way for an end-user to communicate only with his devices or deterministically discover and limit access to only the devices that belong to them. This results in security concerns where in, a user knowingly or unknowingly may take control of devices that belong to other users.
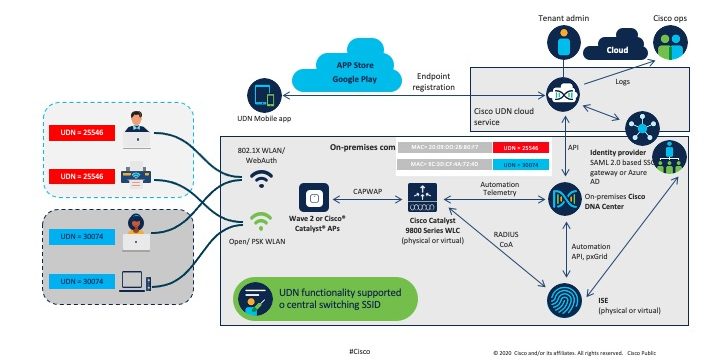
Cisco’s User Defined Network (UDN), enables simple, secure and remote on-boarding of wireless clients on to the shared network environment to give a personal network-like experience. UDN allows an end-user to create their own personal network, consisting of only their devices thereby enabling End-User driven network segmentation. This will help in limiting service discovery scope, realize traffic segmentation and enforcing of access control policies at a group level. This creation of nano-segments in a shared media provides a closed group. In addition, UDN’s ability to invite other trusted users into their personal network gives them the ability to collaborate and share their devices with select set of friends.
Cisco’s UDN solution is supported on Catalyst 9800 controllers in centrally switched mode. Wireless controller along with the APs enables the containment of link-local multicast and broadcast traffic and optionally unicast traffic. This solution works with both Cisco and 3rd party switching infrastructure and for both IPv4 and IPv6 traffic. The SSID on which UDN profile can be enabled should have either MAC-filtering enabled or should be an 802.1x SSID.
Security is the first line of defense for protecting users, devices and data from malicious actors. The wireless security solutions discussed above detect and protect the users, devices, applications and data. It addition, it enables traffic segmentation along with end-to-end user and application visibility and network analytics.
For more Information
Check out our Intent-Based Networking video channel.
Subscribe to the Networking blog






How about focusing on the Fragattack right now instead. 😉
…and after that fixing the horrible mess that BYOD onbording via the ISE platform is and have been for the last 5-6 years……