Legacy Networking and Operational challenges
In my 25-year networking career working directly with customers I’ve become accustomed to network teams traditionally splitting into separate domains. Larger networks are very often built and operated based on distinct domains, like campus and branch, data center and WAN.
It was sometimes eye-opening for me and even a little awkward when I had the opportunity to introduce members of different domain teams to each other. Oftentimes they were simply working in isolated silos. And that has become a major obstacle to IT and the business.
Agility is the goal and E2E is the way
As we are rapidly learning, network agility is a fundamental requirement to meet the dynamic needs of your digital transformation initiatives – and increasingly your business resilience needs as well. And that agility cannot be served by a single domain alone. It needs to be end-to-end — from the user or device to wherever the application is located.
Time and again, I have witnessed this legacy approach to networking foster a manual operations environment, inefficient deployment procedures, slow troubleshooting and a tactical, inconsistent approach to planning.
IT Operations needs to shift from a break fix mentality to a business alignment mentality
Easier said than done. That shift needs to be done in digestible stages. I’ve always been a proponent of a crawl, walk, run approach – so long as you keep your ultimate goal in site. In this case, that means building the intelligent automation and insights delivered by an intent-based networking (IBN) platform in the individual domains. Each is dedicated to the very specific needs of that domain. For example:
- The access domain needs to focus on automating secure, intelligent on-boarding and segmentation
- The WAN domain on application performance and secure cloud access
- The data center domain on workload performance, security and portability
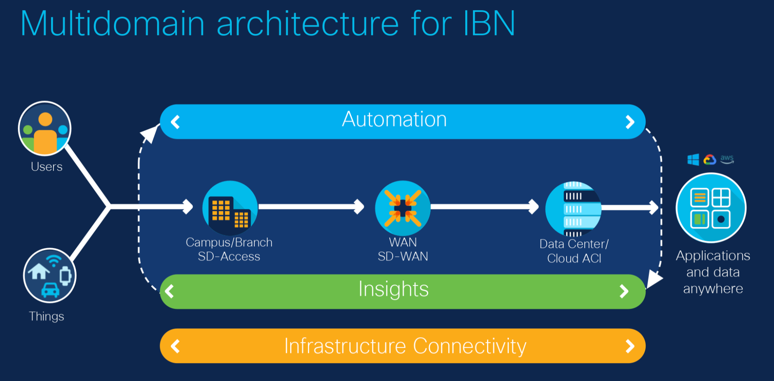
Creating separate domains allow each to focus on the unique job at hand. It is analogous to the move from monolithic applications to containers, in that it takes large tasks and breaks them down into smaller more manageable services, and allows them to focus on specific functions. But when integrated together, they operate as a single larger application. With one or more of these IBN domain platforms in place and by taking advantage of the built-in API’s, you have the opportunity to deliver on a multidomain IBN strategy that aligns the network to application and security policy, end-to-end.
Journey towards a Multidomain IBN Architecture
Moving towards a multidomain architecture will not only ease the demands on your IT team but will deliver a better end user experience. Your journey to multidomain for IBN does not mean you need to incorporate all three domains to enjoy the benefits of automation, visibility, and insights. You can start simple and implement a single domain which best fulfils your business requirements.
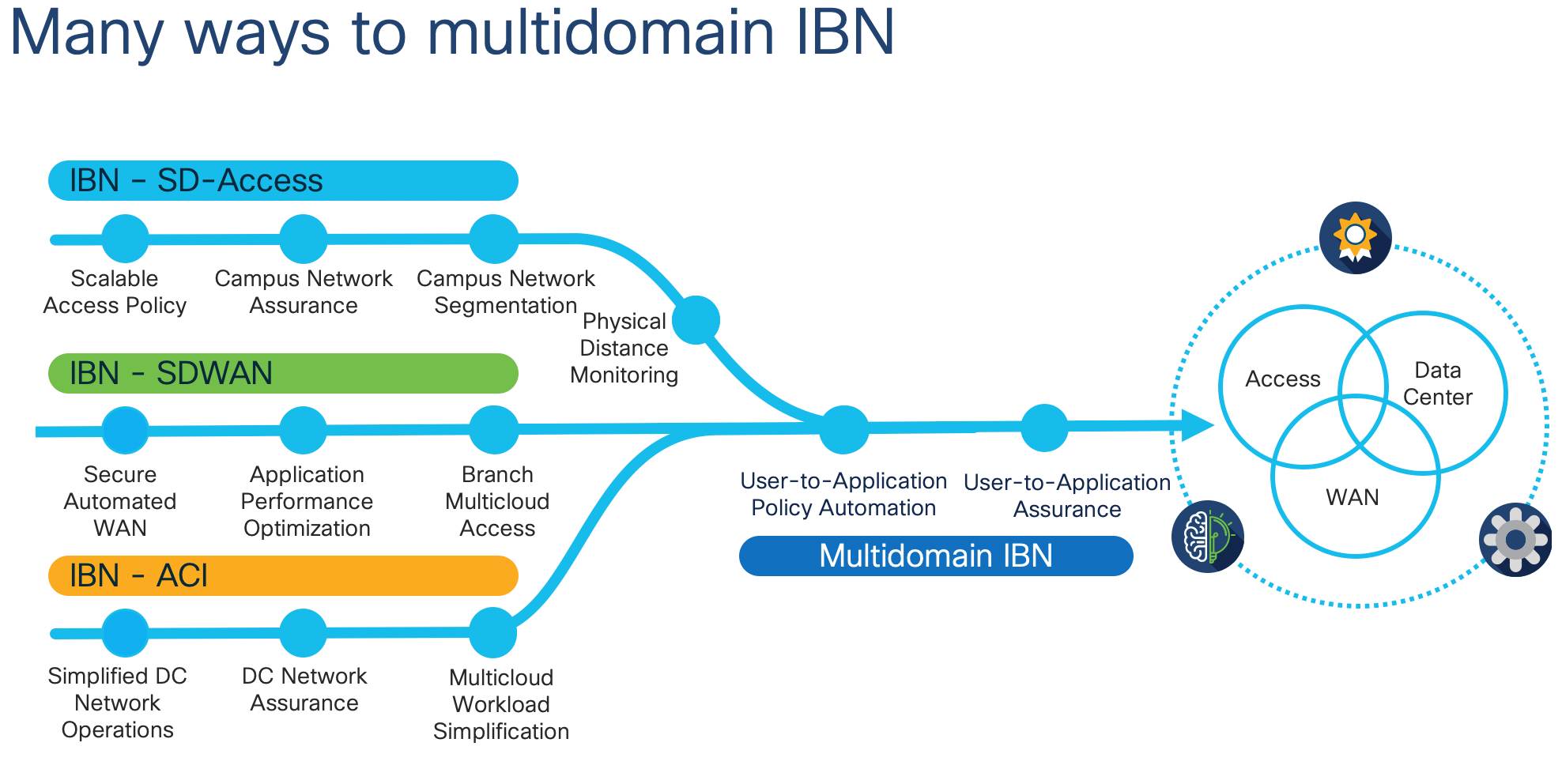
- Start with the implementation of IBN in a single domain – for example, access. Cisco SD-Access enables IT transformation at the access layer by improving user and endpoint visibility, defining and applying group-based access policies, segmenting the network to isolate traffic, reduce risk, and contain threats. SD-Access will allow your teams to improve troubleshooting with assurance. What took your staff and Cisco TAC weeks to resolve, you can now get to root cause in days or hours. There is significant value by simply implementing SD-Access as a single domain.
- In series or parallel, depending on resources and timelines, you can take on a second domain such as the data center. With Cisco ACI and Cisco Nexus Dashboard you can automate and optimize your data center and cloud networks. Cisco ACI will protect your business with a zero-trust model and accelerate the move to multicloud with seamless connectivity across any data center or cloud. Multidomain Integration: Now, by integrating across Cisco ACI and Cisco SD-Access platforms you can automate activation of an end-to-end segmentation policy by exchanging users and applications identification and authorization information.
- At the same time, you should be looking at optimizing the WAN domain for branch connectivity and cloud access. Implementing Cisco SD-WAN in a cloud-based platform provides you with enhanced application experience, full security for internet and cloud, multicloud optimization, operational simplification, and advanced analytics. Multidomain Integration: By integrating Cisco SD-WAN and Cisco ACI your applications will inform the WAN of their SLA requirements.
Next Steps:
- See detailed information on the integration of Multidomain for IBN
- See how Farm Credit Mid-America transformed their business with Multidomain for IBN
- Take an assessment to see where you stack up on the journey to Multidomain IBN
Please do let me know if this blog was helpful or if you have any questions.





