Abstract: Always wanted to evolve your network to Cisco SD-Access but afraid of the impact the transition might have to your users? Don’t fear – these three simple steps show you how you can start small and work your way up, and your users won’t even notice!
Why SD-Access and why now?
In 20+ years working in what I thought was an already fast-paced industry, I have never seen the speed at which our customers’ business models were disrupted in just the past year. Suddenly, evolving IT and networking rose to the top of their concerns as they strived to regain a degree of normalcy. What was on the five-year horizon now needed to be done in five weeks!
These disruptions accelerated the pressures that have already been in motion for the past several years that were forcing organizations to re-evaluate their IT strategies to keep ahead of the new challenges brought on by increases in scale, IoT, mobility, and security.
I also observed that networks that relied on manual operations and configurations using Command Line Interface (CLI) had a much more difficult time in coping with the changes. They were not designed for dealing with disruptions. Their IT teams were simply being outpaced. One of the areas they were struggling with was the constant modifications they had to do for securing their enterprises using Access Control Lists (ACLs) and firewalls.
All this brings me to Cisco Digital Network Architecture (Cisco DNA) and Software-Defined Access (SD-Access) and how they have been helping IT teams stay ahead of networking needs in support of their business. SD-Access removes IT’s burden by automating operations and securing the organization through comprehensive segmentation. It does so by giving you unprecedented visibility in who is on your network and how they are using it, helping you define and enforce access policies throughout the network without manual intervention, and monitoring all devices continuously for zero trust security. Access policies segment the network with granularity, separating traffic, reducing the threat surface, and increasing security. For its full set of features and functions, SD-Access depends on the network device, Cisco DNA Center, and Cisco Identity Services Engine (ISE).
Here’s the good news, adopting SD-Access does not mean that you set up your entire infrastructure from the get-go. You can start experiencing some of its benefits rapidly with minimal changes and then, at your pace, comfort level, and business requirements, begin to evolve your network to make your network ever more capable, secure, and agile.
Three steps to get the most out of SD-Access
Change is never easy. We have the natural instinct to leave things be even if they don’t deliver to our expectations, especially if the effort appears massive, and it is as critical as the enterprise’s network.
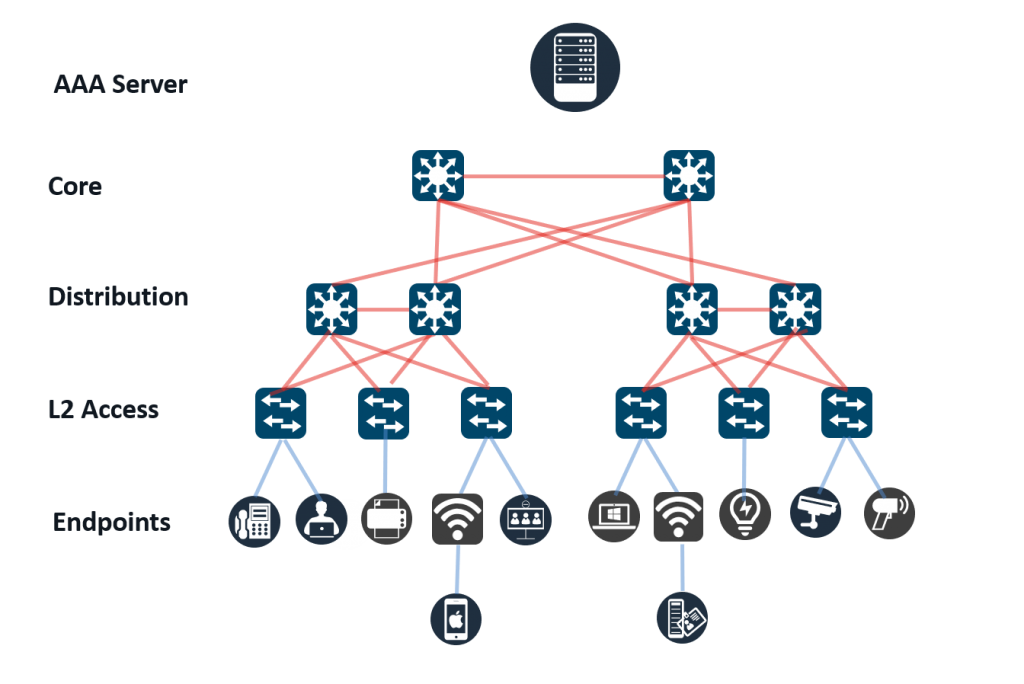
Recognizing this reluctance to change, SD-Access allows you to start small and work your way up. I will illustrate it with an example. Let’s say you are a typical organization with a core, distribution, and access switching layers. You use a AAA server to authenticate users as shown in the diagram above. You are facing business needs of having to add more IoT devices, let users work from places other than their usual desks, and making the network more secure.
Step-1: Segment using VNs but retain your VLAN-IDs
As in a typical organization, Layer 2 access policies using VLANs has served you well. But as we know VLANs are not scalable, require manual configurations, and do not offer adequate security. And yet you cannot simply stop using them as that would cause massive disruptions to your business.
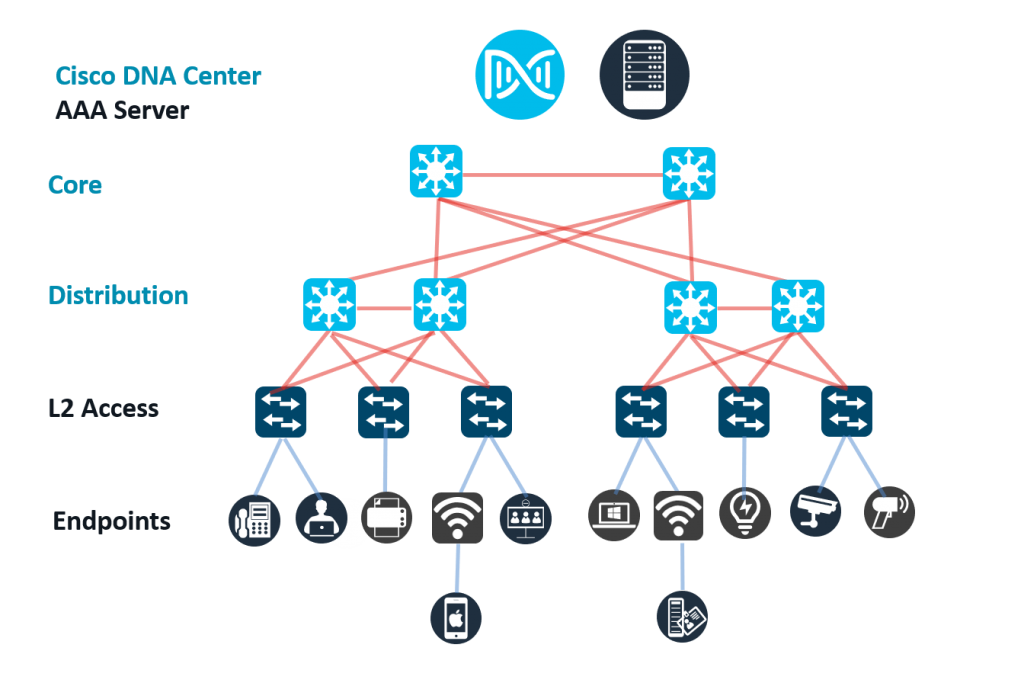
Cisco SD-Access offers you an elegant solution. You can retain your existing Layer 2 access mechanism, VLAN-IDs, and the access switches and convert just the distribution and core switching layers to SD-Access using the Cisco DNA Center. Segment the network automatically using the more scalable Virtual Networking (VN) technology and create logical partitions or as they are called “macro-segments” in SD-Access terminology. Map the VLAN-IDs to VNs and not only you eliminate a lot of manual work, but also increase security and scalability of those VLANs.
“We are convinced that SD-Access will help us make our operational production processes more efficient. Due to its holistic approach and the interfaces to other systems, we will be able to automate a significant part of our daily work. During our Proof-of-Concept testing we confirmed that both connecting L2 non-fabric switches to the SD-Access fabric and utilizing L2-only overlays work as expected. Along with the ability to configure custom VLAN IDs on the SD-Access fabric, these are some of the fundamental features we need to provide the necessary services for our clients.” – Christoph Hofmann, Referent IT-Betrieb Netze, Mitteldeutsche Flughafen AG (Leipzig and Dresden airports in Germany)
Step-2: Move up to granular visibility
If you don’t already have Cisco ISE, now would be a good time to add it into your network. With it you can enable additional SD-Access functions such as AI Endpoint Analytics and group-based policy analytics. These applications that run in the Cisco DNA Center and use ISE, fully profile all connected endpoints, place them into logical groups, and show you communications between groups. This gives you unprecedented visibility into the network – insights that you can use to define and enforce fine-grain access controls for even better security.
“With SD-Access in our new MEB plant, we were able to automate and deploy thousands of devices within hours and greatly reduced our turn-up time. With SD-Access we were able to use our existing access switches which enabled a smooth migration of services and reduced up-front costs. In addition, with our new Cisco DNA Center based network, we can now visualize the status of PLCs and other industrial terminals, greatly improving our maintenance operations.” – SAIC Volkswagen
Step-3: Evolve to micro-segmentation
Once you have introduced VNs or macro-segments into your core and distribution switching layers and added ISE, you can start to reconfigure your Layer 2 access switches to Policy Extended Nodes (PEN). Such nodes retain their VLANs but also start acting on Scalable Group Tags (SGTs) that reside in packet headers and identify the source of the packet. PEN enabled switches can either allow the packet to flow through or reject it based on defined access policies.
With SGTs, you can begin to micro-segment your network that allows you to control communications between endpoints down to the service, transport, and port levels, providing even more protection against threat proliferation.
Micro-segmentation will also help you enforce access policies right into the access level and provide protection in traffic flowing between ports in the same switch which was up until now not possible.
“We were in a large Cisco SD-Access/SD-WAN POC and required VLAN-IDs to be re-used on the border nodes across sites to support the automation requirements. The custom VLAN-ID feature enabled us to re-use the VLAN-IDs across sites and we were able to solve the scalability challenge. This will also be of use to other customers where there is a need to migrate from existing deployment to Cisco SD-Access.” – Anders Marius Jørgensen, Systems Engineer, Conscia
Conclusion
With simple and incremental modifications to your network, converting your network over to SD-Access does not need to be undertaken all at once. The steps I have outlined in this blog may not even be the right ones for you. You have the power to decide what you want to get done and start from where you are now.
Today, there are over 1,650 production level deployments the world over who rely on the visibility-driven policy-based zero trust security that SD-Access provides. After all, it is only solution in the marketplace that provides granular visibility, continuous monitoring, and multilevel automated segmentation.
It is our commitment to you to continue to add value to your investment and to make it easier for you to benefit from our innovations. In the weeks to come, we will follow up this blog post with others that will show you how much easier we are making adoption of the technology.
Please contact your Cisco sales representative to arrange for a briefing or for more information.
To learn more about Cisco SD-Access and how to migrate your existing network to it, please:
- Listen to Cisco SD-Access Migration Strategies – BRKENS-2008 at Cisco Live 2021
- Visit Cisco SD-Access website
- Read the white paper on Removing the Complexities from Network Segmentation
Check out our Cisco Networking video channel
 “We are convinced that SD-Access will help us make our operational production processes more efficient. Due to its holistic approach and the interfaces to other systems, we will be able to automate a significant part of our daily work. During our Proof-of-Concept testing we confirmed that both connecting L2 non-fabric switches to the SD-Access fabric and utilizing L2-only overlays work as expected. Along with the ability to configure custom VLAN IDs on the SD-Access fabric, these are some of the fundamental features we need to provide the necessary services for our clients.” – Christoph Hofmann, Referent IT-Betrieb Netze, Mitteldeutsche Flughafen AG (Leipzig and Dresden airports in Germany)
“We are convinced that SD-Access will help us make our operational production processes more efficient. Due to its holistic approach and the interfaces to other systems, we will be able to automate a significant part of our daily work. During our Proof-of-Concept testing we confirmed that both connecting L2 non-fabric switches to the SD-Access fabric and utilizing L2-only overlays work as expected. Along with the ability to configure custom VLAN IDs on the SD-Access fabric, these are some of the fundamental features we need to provide the necessary services for our clients.” – Christoph Hofmann, Referent IT-Betrieb Netze, Mitteldeutsche Flughafen AG (Leipzig and Dresden airports in Germany) “With SD-Access in our new MEB plant, we were able to automate and deploy thousands of devices within hours and greatly reduced our turn-up time. With SD-Access we were able to use our existing access switches which enabled a smooth migration of services and reduced up-front costs. In addition, with our new Cisco DNA Center based network, we can now visualize the status of PLCs and other industrial terminals, greatly improving our maintenance operations.” – SAIC Volkswagen
“With SD-Access in our new MEB plant, we were able to automate and deploy thousands of devices within hours and greatly reduced our turn-up time. With SD-Access we were able to use our existing access switches which enabled a smooth migration of services and reduced up-front costs. In addition, with our new Cisco DNA Center based network, we can now visualize the status of PLCs and other industrial terminals, greatly improving our maintenance operations.” – SAIC Volkswagen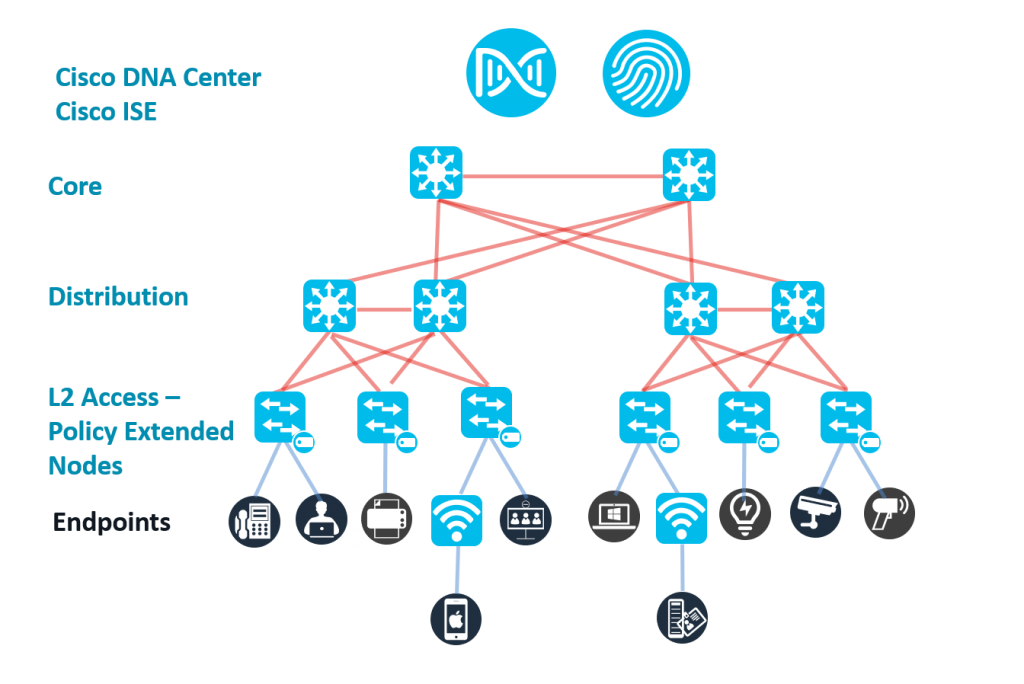
 “We were in a large Cisco SD-Access/SD-WAN POC and required VLAN-IDs to be re-used on the border nodes across sites to support the automation requirements. The custom VLAN-ID feature enabled us to re-use the VLAN-IDs across sites and we were able to solve the scalability challenge. This will also be of use to other customers where there is a need to migrate from existing deployment to Cisco SD-Access.” – Anders Marius Jørgensen, Systems Engineer, Conscia
“We were in a large Cisco SD-Access/SD-WAN POC and required VLAN-IDs to be re-used on the border nodes across sites to support the automation requirements. The custom VLAN-ID feature enabled us to re-use the VLAN-IDs across sites and we were able to solve the scalability challenge. This will also be of use to other customers where there is a need to migrate from existing deployment to Cisco SD-Access.” – Anders Marius Jørgensen, Systems Engineer, Conscia




