Shutdown. Cleanup. Restart.
This “incident response” approach to cyber security was designed primarily for enterprise networks, data centers, and consumer electronics. It companies perimeter-based protection that uses firewalls, intrusion detection systems (IDS) and intrusion prevention systems (IPS) to prevent security threats.
When threats penetrate perimeter-based protections, human operators typically shut down the compromised system, clean up or replace the compromised files and devices, and then restart the system.
Next is forensic analysis. This, too, requires intensive human involvement to harden existing protection mechanisms and develop future remediation measures.
However, as we move into the next phase of the Internet—the Internet of Things (IoT)—this security paradigm won’t be adequate because of changing form factors and use cases.
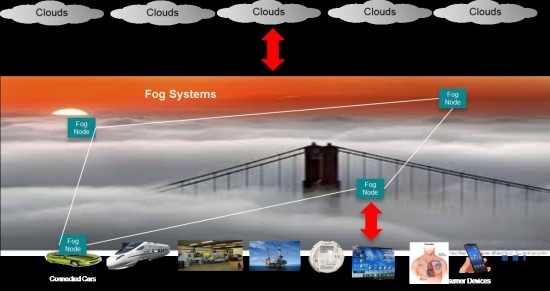
To succeed, we need fog computing. This will extend cloud computing (including security) to the edge of an enterprise’s or consumer’s network. Much in the way cloud technology enabled the Internet, fog will enable an array of secure IoT possibilities.
The Internet of Things has Unique Security Requirements
Many of the new things connected to the Internet will have long lifespans and yet highly constrained computing and memory resources that are difficult to upgrade. For instance, over a car’s lifespan of more than eleven years, security threats will become significantly more advanced and the amounts of resources required to combat the fast evolving threats will increase accordingly.
Other highly vulnerable, or completely unprotected environments, could include bicycles, drones, sensors, wearable devices, smart appliances, and communication devices deployed along roadsides and at traffic intersections to support smart cities. In these cases, traditional firewalls aren’t sufficient.
Fog will provide innovative ways to reduce the security complexity and costs on individual devices and compensate the devices’ constrained security capabilities with off-board security services. As a result, as in the car example, security upgrades will be possible and effective. And, via fog, concerns about scalability and trustworthiness will be addressed.
Reducing human-intensive incident responses is also critical for mission-critical systems, because shutting down some “things” can cause intolerable consequences. By placing fog-based automated security at the edge, we can reduce the human component and replace it with dynamic and risk-proportional incidence response.
In addition, many things won’t be managed by IT experts. Security operations must be significantly more automated and manageable. Remote online threat mitigation will be essential. Again, this is where fog can play a role.
Both industry and academia have been devoting tremendous efforts to build market consensus and develop enabling technologies and standards in support of IoT. An important milestone is the recent introduction of the Open Fog Consortium.
This is an ecosystem of industry and academic leaders committed to resolving the challenges surrounding fog and fostering an open architecture for fog computing. We expect to accelerate IoT deployments—and to maximize the value of these deployments across a wide range of industries.
By working toward a common goal, I’m convinced we’ll find the answers we need in fog computing. As a result, we’ll be in a better position to shift security paradigms—and address the challenges and exciting new opportunities afforded by the Internet of Things.





Tough work ahead I believe.