In today’s fast-paced and hyper-connected world, gone are the days when deploying network devices required sending an expert to each location — a cumbersome, time-consuming, and error-prone process that caused significant downtime and increased operational costs. To surmount these barriers, Cisco offers a variety of network orchestrators. These included Cisco Catalyst Center (formerly Cisco DNA Center), SD WAN Manager (formerly Cisco vManage), and Meraki Dashboard, which assist businesses in automating their campus network management including Day 0 provisioning. These orchestrators allow network administrators to remotely deploy a large number of network devices quickly and securely, without requiring any human intervention. This not only saves time and money but also liberates IT department resources, allowing them to redirect their efforts towards other critical areas.
Using Catalyst Center PnP, Cisco IT was able to reduce annual deployment costs for some sites by approximately 25%, or more than $1.6 million. Additionally, upgrading our 285 small and medium-sized offices with Cisco Catalyst Center saved 570 man-hours per upgrade[1].
In addition to Cisco network orchestrators for customers employing a Do-It-Yourself (DIY) approach with homegrown tools, Catalyst 9000 series switches offer support for an assortment of open standard-based implementations for Day 0 network automation, such as Preboot eXecution Environment (PXE) and Zero Touch Provisioning (ZTP). So, if you find yourself still manually configuring network devices, it may be time to consider stepping out of the stone age and exploring the benefits of automation.
Day 0 network automation
When delving into the realm of open standard-based Day 0 network automation, it becomes clear that PXE, while a useful technique, comes with a set of limitations, such as only allowing network devices to boot from a network-based source and not being able to send configurations to devices during the PXE workflow. ZTP, on the other hand, can be used to upgrade software images and push configuration files, reducing the chance of human error and ensuring configuration consistency in order to get network devices up and running.
While ZTP and PXE are convenient for automating the provisioning process, they may inadvertently expose network devices to potential threats. Lack of secure authentication and verification mechanisms during the provisioning process is one of the primary concerns with these techniques. Furthermore, ZTP and PXE utilize HTTP/TFTP to download the software image or configuration files, which are inherently insecure protocols because they lack encryption. Due to these limitations, these techniques could result in unauthorized access to the device or a man-in-the-middle attack if the right security measures aren’t put in place during the device provisioning.
Cyberattacks have increased
In today’s rapidly evolving digital landscape, where enterprises are undergoing substantial transformation, cyberattacks have increased amid the rise of cloud computing, hybrid and multi-cloud networks, and the rise of remote work. According to the latest IBM Ponemon Institute 2023 Cost of Data Breach Study, the average cost of a data breach reached an all-time high in 2023 of USD 4.45 million [2]. Furthermore, according to ITIC’s 2022 Global Server Hardware Security report, 76% of firms cite Data Breaches and Human Error as the leading reason of server, OS, application, and network downtime, and the hourly cost of downtime has risen to over $300,000[3].
Given that cybercriminals are constantly devising new techniques to infiltrate networks, the traditional security approach, which assumes that everything within the network perimeter is trustworthy, is no longer sufficient. This is also true for Day 0 network automation, where it is crucial to validate the trustworthiness of the newly deployed device, bootstrap server, and configurations pushed to the device. Without implementing these security measures, our networks are vulnerable to a variety of cyberattacks, including the notorious zero-day exploits. To ensure maximal security and minimize potential risks, the Zero Trust principle of “never trust, always verify” must be implemented throughout the entire provisioning process.
Maintain security throughout the provisioning process
This is where Secure Zero Touch Provisioning comes into play. Secure ZTP, as described in RFC 8572, is an enhanced version of ZTP that emphasizes maintaining security throughout the provisioning process by reducing the likelihood of security breaches. Secure ZTP is a proactive approach that employs robust authentication, a secure boot mechanism, and encrypted communication channels to enhance the security posture of a network while Day 0 network automation is in place.
How does Secure ZTP work?
Secure ZTP employs three-step validation, including device validation, server validation, and artifact validation, to securely onboard the device. The diagram provided below illustrates the various steps involved in the device onboarding and provisioning process within a secure ZTP framework. Let’s take a closer look at each of these steps:
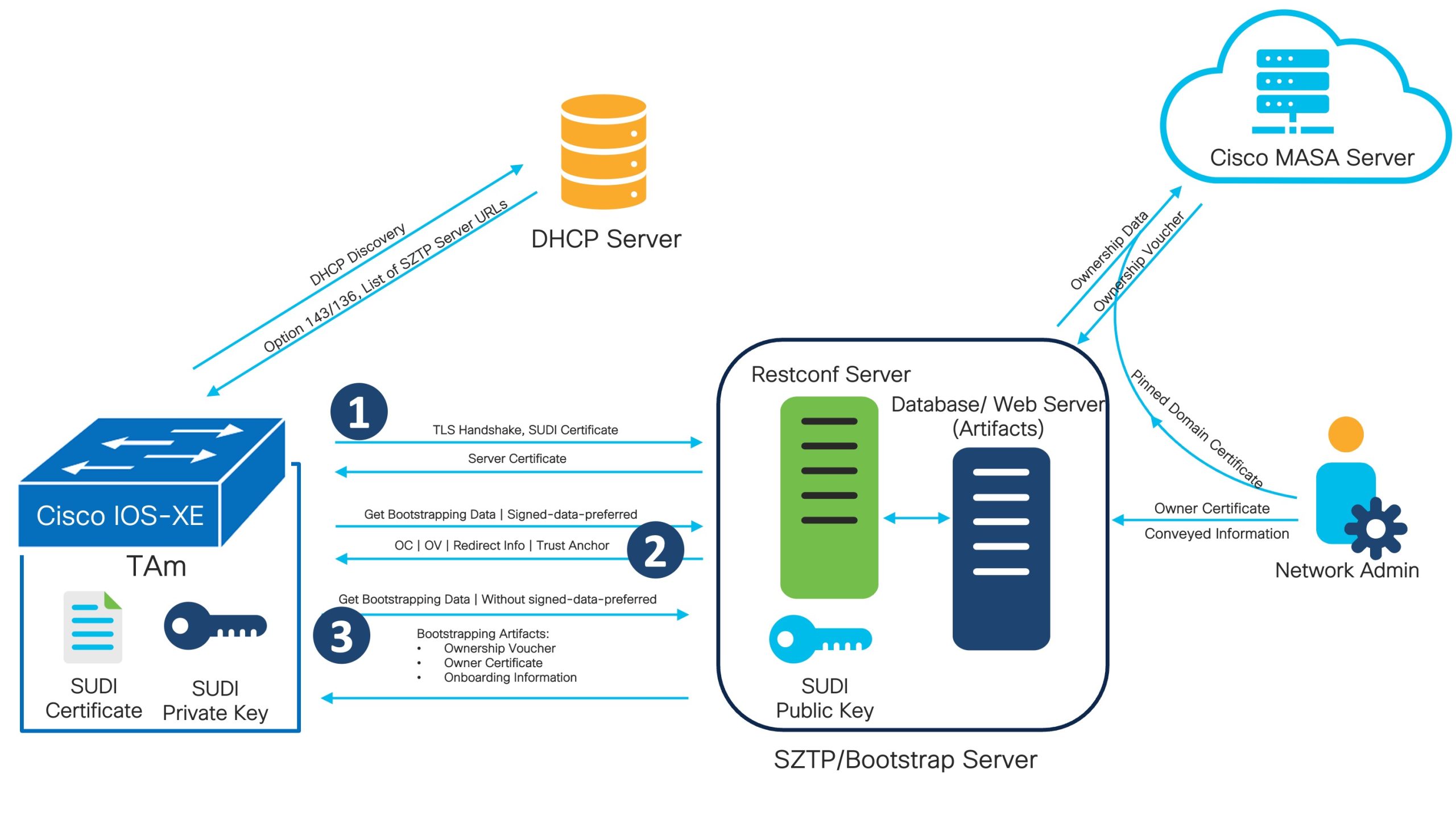
1. Device Validation
Before onboarding a new device on the network, it is crucial to ensure that neither the device nor its firmware has been tampered with or compromised to prevent supply chain or any other attacks, in which malicious actors attempt to introduce modified or malicious devices into the network. Based on the recent IBM report, 15% of organizations identified a supply chain compromise as the source of a data breach [2].Secure ZTP performs device authentication prior to provisioning it in order to verify the integrity and authenticity of a device and to allow only authorized devices to join the network.For device validation, Secure ZTP uses certificate-based authentication where the device sends the Trust Anchor Certificate (also known as a SUDI certificate installed in the device during the manufacturing process) to the Secure ZTP server, and the server validates it with the public certificate (provided by the manufacturer) to ensure the device’s authenticity.
2. Server Validation
Server validation is another vital part of the Secure ZTP. By confirming the server’s identity, the device can assure that it is communicating with an uncompromised, trustworthy server. This prevents unauthorized or malicious servers from intercepting or manipulating the provisioning process. After verifying the device, bootstrap server sends server certificate. The device requests bootstrapping data with the flag “signed-data-preferred” after receiving the server certificate, indicating that the device does not trust the server. In this case, keep in mind that server validation is optional in Secure ZTP. If the network administrator decides to perform server validation (which entitles server to receive bootstrapping progress report), the server will send the “redirect-data” with other bootstrapping data to the device, providing its own address and the trust anchor. The device verifies the server’s certificate and marks it as trusted server after receiving the trust anchor. Here, if the system administrator opts not to validate the server, the server will instead pass on bootstrapping data in place of the “redirect-data”. In addition, the device will continue the bootstrapping process assuming the server is untrusted.
3. Artifact Validation
Artifact validation is important to ensure that the configuration files or software images used to provision network devices are authentic and have not been tampered with. Once the server validation is complete (or skipped), the bootstrap server will send the owner certificate, ownership voucher, and onboarding information to the device as bootstrapping data. Let’s discuss them closely to gain a better understanding.
- Ownership Voucher (OV): The ownership voucher artifact validates the owner certificate to verify the identity of the device’s owner. The device manufacture signs the OV and provides it to the customer based on the request. To generate the OV, the customer must provide the pinned-domain-cert and serial number of the device to the Cisco MASA server.
- Owner Certificate (OC): Owner Certificate is an X.509 certificate that binds an owner identity to a public key, which a device can use to validate signature over the conveyed information artifact. The owner certificate also holds all intermediate certificates that led to the “pinned-domain-cert” certificate specified in the ownership voucher, allowing the OV to validate the OC.
- Conveyed Information/Onboarding Information: Onboarding information provides data necessary for a device to bootstrap itself and establish secure connections with other systems. Onboarding information specify details about the boot image a device must be running, an initial configuration the device must commit, and scripts that the device must successfully execute. The onboarding information must be signed by the device’s owner using OC.
Zero Trust is crucial when performing Day 0 provisioning
In addition to its many features, Secure ZTP goes beyond by offering audit trails and monitoring capabilities. This includes logging all provisioning events, configuration changes, and user actions. By monitoring ZTP activities, network administrators can quickly detect any suspicious activity and take appropriate action.
As we wrap up our discussion, it becomes clear that Zero Trust is also crucial when performing Day 0 provisioning, and Secure ZTP is the best way to ensure that zero trust principles are applied while performing Day 0 provisioning using a Do-It-Yourself (DIY) approach.
With the IOS-XE 17.11.1 release, users can now take advantage of the secure Zero Touch Provisioning (ZTP) capabilities with Catalyst 9000 series switches. This exciting feature aligns with the specifications outlined in RFC 8572, ensuring a secure and seamless provisioning experience. For more details about how to implement Secure ZTP, please refer the IOS-XE 17.11.1 Configuration Guide.
Keep Learning with these resources
- Visit the Zero Touch Resource Hub
- Learn more about Cisco IOS XE
- Cisco IOS XE blogs
- Zero Touch Provisioning blog




