Blog co-authored by Pramod Chandrashekar.
Over the past year, cyber attacks have become increasingly common and sophisticated, they were carried out by not only individuals, hacker groups but also nation actors that are well equipped and financed. The sheer scope and audaciousness of these attacks and their impact on the lives of normal users have made them command public attention in 2017.
Cyber attacks been aided by the availability of leaked NSA tools Eternal Blue, Double Pulsar on the internet. We have seen ransomware attacks like WannaCry, Nyetya and their variants, utilizing these tools to cause wide spread havoc. These attacks are not only being used for monetary gain via encryption of user data on the affected system and demanding the payment of a ransom for it’s decryption but also used to cripple enterprises and competitors for political gain by nation actors.
Another trend has been the emergence of IOT devices as a new attack vector for threat actors to exploit. According to Gartner there will be about 20.8 billion IOT devices in use by 2020. These devices are always connected, operate autonomously and are designed without security in mind, providing an easy gateway into a network. Most have been shipped with hard-coded default credentials that make them inherently unsecure and hard to patch. This lack of security was most famously exploited by Mirai, a malware that enslaved hundreds of thousands of IOT devices and utilized them to launch massive DDoS attacks on Dyn affecting access to Netflix, Twitter, Github etc., Krebs on Security and Rutgers University.
Another troublesome trend is that cyber attacks are no longer solely the domain of professionals with advanced programming skills, with the availability of leaked NSA tools, the release of the Mirai source code on GitHub anyone can whip up their own custom malware or simply pay to hire malware as a service to launch sophisticated attacks. This easy accessibility to advanced tools and techniques has not only increased the quality and volume of attacks but has resulted in constantly mutating variants of ransomware and malware that pose a significant challenge to the detection and mitigation systems of security groups and enterprises.
With these new challenges, security practitioners need to constantly keep their security devices up-to-date by publishing new and updated indicators of compromise (IOCs) to keep up with emerging and mutating threats. With the increased volume of attacks, security groups must be able to handle the large volume of events detected by security devices and correlating across multiple independent events to quickly match them to identify an attack in progress and prioritize detected incidents so that they can be quickly acted upon.
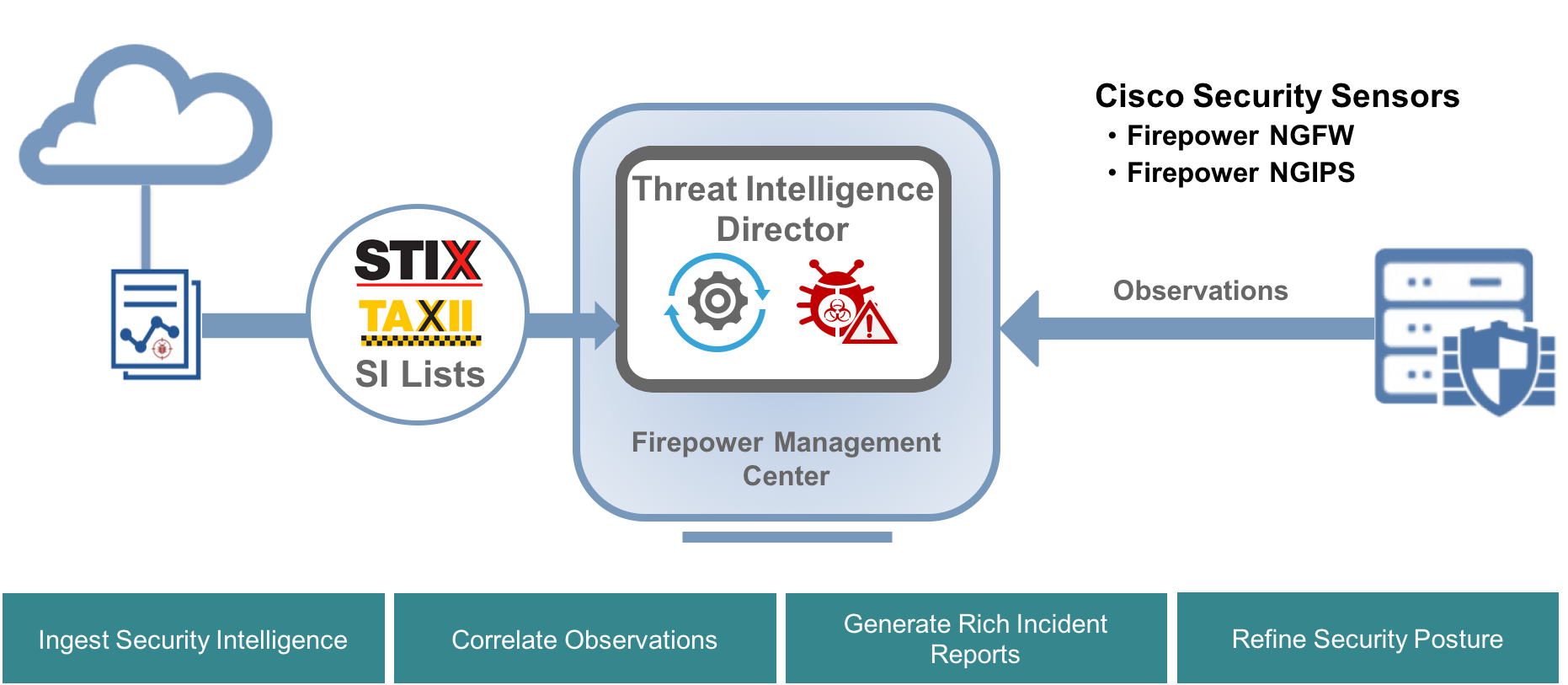
At Cisco Live Barcelona, please stop by Introduction to Cisco Threat Intelligence Director APIs [DEVNET-1774] on Wednesday, Jan 31, 09:00-9:45 a.m where we will showcase Cisco Threat Intelligence Director (CTID) an exciting feature on Cisco’s Firepower Management Center (FMC) product offering that automates the operationalization of threat intelligence. TID has the ability to consume threat intelligence via STIX over TAXII and allows uploads/downloads of STIX and simple blacklists. TID can be integrated with existing Threat Intelligence Platforms (ThreatQ, AlienVault, Infoblox etc) deployed by your organization to ingest threat intelligence automatically. All the imported intelligence is automatically ingested and distributed to Cisco’s Next Generation Firewall (NGFW) product allowing the customer to configure defensive actions. The detection of ingested intelligence on the network automatically generates incidents in real time that can be analyzed by customers. TID also has a rich set of APIs that can be leveraged to automate ingestion of intelligence, its management and the retrieval of incidents using 3rd party applications.
See you in Barcelona!
We’d love to hear what you think. Ask a question or leave a comment below.
And stay connected with Cisco DevNet on social!
Twitter @CiscoDevNet | Facebook | LinkedIn
Visit the new Developer Video Channel




