Network security was much easier when we were dealing with standalone servers hosting a single application and connecting to a dedicated port. As we all know, that’s no longer the case.
Applications and infrastructure have become highly dynamic and distributed. They’re increasingly virtualized and spread among on-premises, cloud, colocation and branch office environments. And the applications are being broken into smaller and smaller pieces using microservices and containers.
While this gives IT professionals, DevOps specialists and business teams tremendous flexibility and agility, it also expands an organization’s attack surface and makes it harder than ever to protect IT resources, users and the business itself.
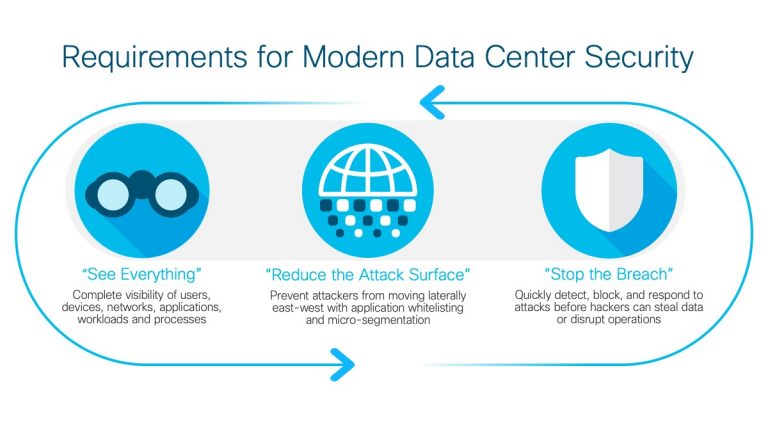
To secure your applications and infrastructure in today’s dynamic, distributed, risk-filled world, you need three things:
Visibility
You can’t defend against something you can’t see. More than ever, organizations need the ability to see every packet and transaction in their computing environment. Not just the North/South traffic coming in and going out, but also the East/West traffic that traverses the network and interacts with a variety of components and workloads.
Segmentation
What can’t be accessed can’t be attacked. Even though computing environments have expanded beyond the data center, the attack surface can be reduced with segmentation. By separating servers, applications, data sets and tenant groups, you can minimize the areas a virus or hacker can access and the damage they can inflict.
Threat detection and response
Last but not least, you need the ability to identify threats as they enter your computing environment, determine what they have touched and act swiftly to throttle the threats and mitigate their impact.
It’s important to note that all three are interdependent. You can’t have effective threat detection and response, for example, without sufficient visibility and segmentation. While there isn’t a single tool that can do it all, there are tools that work together to provide these capabilities across every layer of the network – within the data center and beyond.
- Cisco ACI provides a common, software-defined policy engine that can be extended to cloud, branch office and other computing environments.
- Cisco DNA Center works with Cisco ACI and third-party systems to proactively monitor, troubleshoot and optimize a distributed network.
- Cisco Stealthwatch delivers visibility and security analytics across all network layers and computing environments.
- Cisco Next-Generation Firewalls prevent breaches and provide the visibility and automation needed to detect and stop threats quickly.
- Cisco Tetration extends security policies to the edge and provides enforcement within the virtualization layer.
Software-defined policies are the key. Based on business intent, they establish a baseline of network behavior and provide consistent security across a distributed environment. These capabilities are especially important for companies like Hypoport AG, which is using Cisco ACI to align and secure two data centers that support several autonomous subsidiaries.
“The biggest benefit of switching to Cisco ACI, by far, is that we can confidently identify and state where the traffic is going (and explain why) as well as monitor it in real time,” said Franz Matthies, Senior IT Security Specialist at Hypoport AG.
The company established a DMZ that separates its network into 16 different zones, with firewalls between them for extra security. Each zone – as well as its own dedicated Layer 3 subnet – is stretched across the two data centers.
“Every company has its own tenant and can even have a multitenant setup,” Matthies said. “In each tenant, they can separate the services their application provides. Each tenant has to consider why certain servers are speaking with another server and whether they want that to happen. It would also be impossible for servers from other companies to reach the servers they didn’t own – something that is crucial for our needs.”
Visibility, segmentation and threat detection have always been important. But they’re even more critical as applications and infrastructure extend beyond the data center. As always, our security specialists and partners are available to help.
Learn how to secure the modern data center and check out a new approach to data center security.




Great Article Adam. It is always interesting to hear a customers perspective.