Enterprise IT spends a lot of time designing their cloud networks. This includes thinking about the best way to achieve network segmentation and policy segmentation for workloads, securing workloads by cloud native security policies, and inserting traffic inspection devices such as firewalls for traffic that needs to be scrutinized. While a good design is the first step, choosing a solution that can help automate the configuration for the cloud network is an important next step.
Cisco Cloud ACI automates network and policy configuration for a variety of use cases in the public cloud. Additionally, using the Cisco Application Policy Infrastructure Controller (Cisco APIC), the main architectural component of the Cisco ACI solution, you can find out if your policies have been correctly configured in the public cloud. This is acritical validation because otherwise it’s impossible to find out if all the routes and security rules needed for an application in the public cloud are configured correctly. Discovering discrepancies because of a broken flow is not something anyone wants to experience, whether in test or production environments.
How do you achieve peace of mind in cloud design and deployment? Use Cisco Cloud ACI’s Configuration Drift feature.
How Configuration Drift Works
Configuration Drift is a feature—currently as a beta release—that compares the configuration made in the Cloud APIC to what is actually configured in the cloud. The feature can be turned on from the user settings in the Cloud APIC.
Configuration Drift builds a model of the current configuration on the Cloud APIC and checks it against the inventory that Cloud APIC maintains of the objects it reads from the public cloud. If there is a discrepancy, the configuration drift feature pinpoints the differences. While the drift model is refreshed every 30 minutes, it can also be configured to operate in real-time in response to queries.
OK, Where Can This Help?
While public clouds are expected to be up all the time, it is inevitable that service outages will occur. A public cloud may experience downtime in a particular region or in a particular availability zone and the configuration pushed by Cloud ACI to the cloud in the affected region may be unsuccessful. The Configuration Drift feature catches this failure and reports it as an anomaly. Meanwhile, Cloud APIC will keep retrying the configuration push and once the cloud is back up again, the configuration drift should be cleared.
Another example of the usefulness of the configuration drift feature is during deployment of an application, such as a Human Resource Management app, that involves setting up the policies that allow the front-end HR web application to talk to backend applications. The HR application talks to the Finance backend application to report pay information. It also connects to the Legal backend application. Both communications happen over secure port 443. Cloud APIC translates this into two rules on the security group of the HR application. One rule allows traffic on port 443 from HR to Finance and the other rule allows traffic from HR to Legal on port 443.
Figure 1 shows a snippet of the rules programmed in the HR web network security group. Rule 101 allows traffic from HR to Finance and Rule 104 allows traffic from HR to Legal.
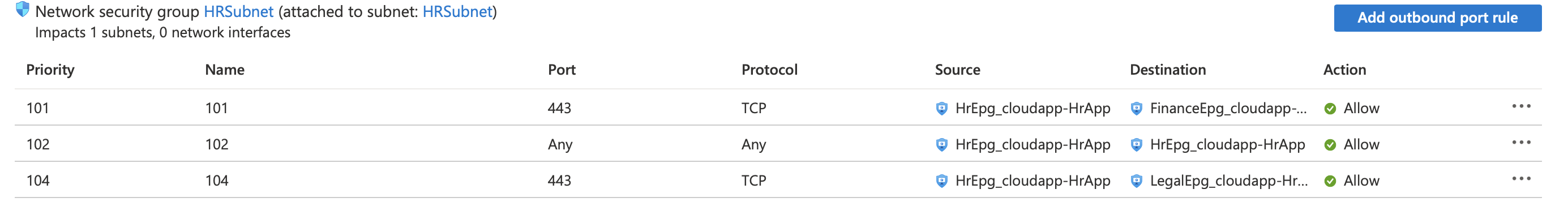
Once the rules are configured, the HR application can talk to the backend applications. A few days later, the cloud network administrator looks at these rules and notices the two rules that allow traffic on port 443. Without paying attention to the destination in the rules (which are different) the admin deletes rule 104, thinking it is redundant. The configuration drift feature will notice that a rule programmed by the Cloud APIC has been deleted and is flagged, as shown in Figure 2.
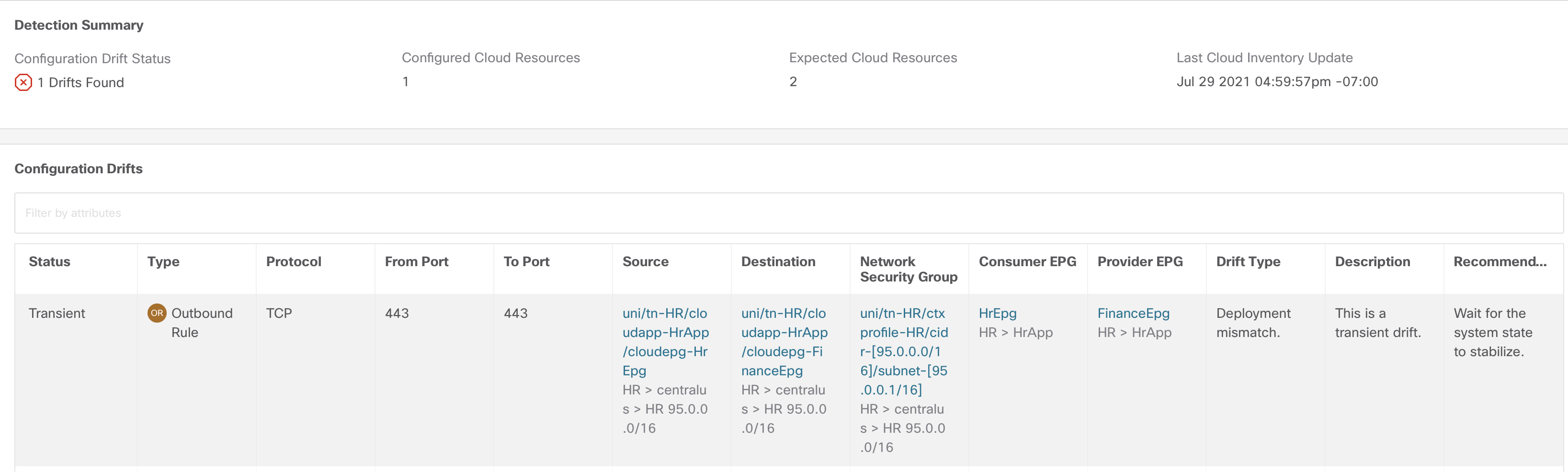
The network operator responsible for using the Cloud APIC can catch this issue before users start reporting issues with the HR application—issues might go unnoticed for days until someone accesses a page in the HR Web application that talks to the Legal backend.
Today, the Configuration Drift feature monitors the drift in endpoint groups, contracts, and virtual routing and forwarding (VRF) resources. Enhancements are under way to provide insights with a Layer 4 to Layer 7 service graph configuration, and for better troubleshooting and visibility into what’s happening in a cloud fabric.
Are there any specific features you would like to see in Cloud APIC? Leave us your comments.
Resources:
Find out more about Cisco Cloud ACI.
Read more details on the Configuration Drift feature in Azure Cloud.




Nice article !!
Thank you Kailash
This will be a great addition to cloud monitoring, especially for security compliance. Nice article!