Modern data centers are under unrelenting attack. East-west traffic security breaches are happening every day. According to Cisco, 75 percent of all attacks take only minutes to begin stealing data but take longer to detect. Once discovered, several weeks may pass before full containment and remediation are achieved. Today’s data centers require a variety of “tools” to deal with sophisticated attack vectors. Network segmentation is a proven tool deployed in data centers.
While the broad constructs of segmentation are relevant, today’s application and security requirements mandate increasingly granular methods that are more secure and operationally simpler. This has led to the evolution of “microsegmentation” to address the following:
- Programmatically define segments on an increasingly granular basis allowing greater flexibility using attributes
- Automatically program segment and policy management across the entire application lifecycle (deployment to de-commissioning)
- Quarantine compromised endpoints and limit lateral propagation of threats
- Enhance security and scale by enabling a Zero-Trust approach for physical, virtual and container workloads.
Cisco’s Application Centric Infrastructure (ACI) takes a very elegant approach to microsegmentation with policy definition separating segments from the broadcast domain.
Figure 1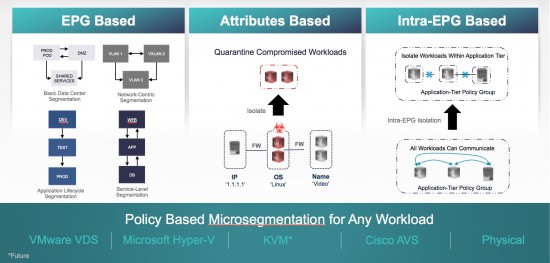
It uses an application-aware construct called End-Point Group (EPG) that allows application designers to define the group of endpoints that belong to the EPG regardless of their IP address or the subnet they belong to (Figure 1). Further, the endpoint can be a physical server, a virtual machine, a Linux container or even legacy mainframes – i.e. the type of endpoint is normalized, thereby offering great simplicity and flexibility in their treatment.
Cisco ACI provides consistent micro-segmentation support for VMware VDS, Microsoft Hyper-V virtual switch, KVM*and bare-metal endpoints and containers, which allows granular endpoint security enforcement. Customers can dynamically enforce forwarding and security policies, quarantine compromised or rogue end points based on virtual machine attributes (such as Name, Guest OS, VM Identifier) and/or network attributes (such as IP address), and also remediation places cleaned end-points back to base EPG.
Key Benefits
ACI micro-segmentation allows users to create micro-segments across multiple VMM and physical domains in a consistent policy driven framework, that allows operational flexibility and choice for customers.
- Micro-segmentation for any multi-tiered application with physical or virtual workloads across any hypervisors
- Use the same policy model to isolate workloads for vSphere, Hyper-V, OpenStack, Containers, and bare metal servers.
- Micro-segmentation classification can use workload attributes such as Virtual-machine attributes and Network (IP, MAC) attributes providing finer grained control at the individual virtual machine(s) level.
- Hypervisor agnostic Intra-EPG isolation policy across VMs and bare metal
- Simple, automatic creation of a quarantine security zone for a multi-tiered application when a rogue end point or threat is identified and automated remediation.
Use Cases
| Micro-segmentation to Quarantine Vulnerable VMs Across Multi-Hypervisor |
|
| Micro-segmentation of a Multi-tiered Application with L4-L7 Service Insertion |
|
| Micro-segmentation of a Multi-tiered Application for Remediation |
|
Cisco ACI micro-segmentation can provide enhanced security for east-west traffic within the data center. Its true value lies in its integration with application design and holistic network policy, and transparent interoperability with a wide variety of hypervisors, bare-metal servers, Layer 4 through 7 devices, and orchestration platforms.
For More Information:
Video: Cisco ACI and IT Security Automation Saves the Day
White Paper: Data Center Microsegmentation: Enhance Security for Data Center Traffic




Talk about Agile IT. Great read.
I have a question about the micro segmentation.
Is the segmentation done on NIC when you use IP-address as a attribute? So can we put one machine in multiple uSeg EPG’s? Our SQL server has multiple instances with multiple NIC’s. We want to put each NIC in a different uSeg EPG’s. Is that possible do you think or is that no the way it works?
Besides the above question.. do you have a case where microsegmentation is working on ACI with a Hyper-V platform? IP-address based micro segmentation isn’t working at this moment on our environment.
Nick, Yes, that is possible. The uSeg EPG classification using IP address corresponds to the IP of the NIC. So, each NIC ca be placed in a separate uSeg EPG using the IP address attribute. Another idea is to use MAC based EPG where each NIC would have a unique mac-address assign it to uSeg EPG. For your HyperV question, Microsoft SCVMM uSeg support was introduced in Brazos release which shipped in December 2015. Brazos supports ACI uSeg for Hyper-V host using IP address attribute as well as VM attributes.