In Part 1 of this blog series, we looked at Gartner’s definition of Fabric based infrastructure (FBI). In part 2, we explored the benefits of service profiles and automation of server management. In this last installment, we will look into the benefits of fabric extension to virtual machines.
According to an IDC report (New Economic Model for the Data Center), the rate of growth of virtual machines is much higher than physical machines. The life cycle of virtual machines is more dynamic than physical servers. Virtual machines may need to be moved from one network to another for data access. Additionally, typical deployments of virtual machines have an extra layer of switching in the hypervisor. The software switches in the hypervisor emulate hardware at the expense of application performance. Cisco UCS solves these problems with the Cisco Virtual Interface cards (VICs) acting as adapter fabric extenders (fig 1) and bringing the network to virtual machines (VMs).
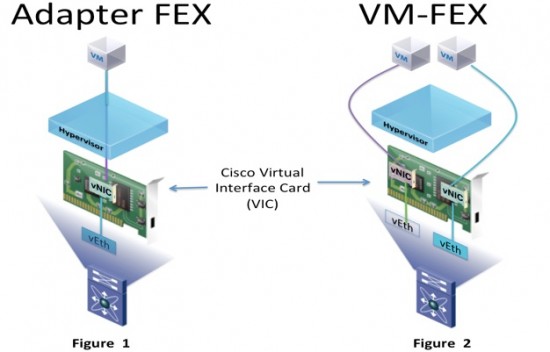
Another problem is that network administrators have no control on the soft switches in the hypervisor, which makes monitoring of network traffic to individual VMs very cumbersome. Cisco VICs use the VN-Tag standard in IEEE 802.1 BR standard to manage each link from the VM as if it were a physical link. The VICs can provide dynamic interfaces to virtual machines allowing the network to bypass the hypervisor and directly connect to the VM. This VM fabric extender (VM-FEX) technology (fig 2 above) allows VMs to connect to networks like physical servers. Network administrators can now monitor the ports easily. Additionally, the VMs can move from one Cisco UCS server host to another with the same security policies and no compromises on the overall network security to allow the move. For a more detailed discussion refer to the white paper – Delivering on the promise of Virtualization.
In all data center deployments, performance and monitoring of applications (services) is the ultimate test. As a software practitioner I found that several problems and issues showed up when we scaled applications by adding more users. The defects generally ended up in the “application performance” bucket. In order to solve these problems, the first order of business is monitoring. Once the initial performance problems have been resolved and the application is in production, the monitoring must continue. Service level agreements (SLA) capture application performance requirements in a contract between the service provider and consumer. There are many Service Assurance tools to help IT ensure that services meet SLAs. CA Technologies has tools to monitor and manage applications running on the Cisco UCS (physical or virtual). I am looking forward to CA World 2013 in Las Vegas next week, where we will feature the Cisco UCS in CA’s Service Assurance Pavilion.




Hi Ranjit,
I liked this blog post, thank you.
If VM-FEX hase vSwitches used less, what are some of the potential factors prohibiting or limiting functionality?
For example, aside from cost, how would the VMs using VM-FEX participate in inter-cloud?
Are the VICs able to participate in Fabric-Path and/or do they link up to the Nexus 5k in the same way a 2k FEX would?
thanks! Jay