According to the Cisco 2017 Annual Security Report, security attacks on businesses have significant consequences with nearly quarter of these companies suffering lost business opportunities, 20 percent of them losing customers, and more than 30 percent of them losing revenue. For example, the recent rash of ransomware attacks around the globe are expected to cost businesses more than $5 billion and an unknown sum in their reputations. This doesn’t even count the attacks that happened just last week.
The reality is that security attacks are increasingly becoming a question of “when” not “if” for companies today. Therefore these organizations can no longer simply wish away gaps in security protection, they must take all active measures to defend themselves vigilantly from known and even unknown threats.
Compounding this challenge for businesses is that what constitutes a “security perimeter” is amorphous to say the least these days. Technologies and operational models such as IoT, public cloud, data center virtualization, enterprise mobility, outsourcing, extranets, open source software, etc., while useful, can all undermine the effectiveness of physical security protections. With real threats that can come from inside or outside the “corporate firewall”, companies need more than a trust-but-verify approach to defending themselves from security threats and attacks.
This requires companies moving beyond perimeter security when it comes to protecting their data and their data centers. Instead, security has to be comprehensive and pervasive on every network device (switches, routers, etc.) as hackers get more sophisticated and unpredictable and capable of exploiting both hardware and software vulnerabilities. These attackers, with cutting-edge techniques, can access memory chips, use tools to extract the contents of those chips and then use the content to build/configure systems to act as imposters on the customer’s network. Bottom line – Malware can be installed on a router or switch. Are you protected ?
Building Data Center Trustworthy Systems
What’s needed is a way to verify that all devices in your network and data center are authorized under your control. This is why the trust and transparency of building Cisco Trustworthy systems should be a foundation in a security architecture. These systems are mechanisms to help companies properly identify and validate users and behaviors as they should be. This is analogous to an effective airport security model, where identity verfication happens at multiple stages during the trip from ticketing to boarding. Verify, verify again, and then trust.
The Cisco Trustworthy data center systems are built on a comprehensive and pervasive set of security, data protection and privacy solutions delivering both network and infrastructure-level security, which can get as granular as ensuring that your software code is authentic and no physical or software tampering has taken place. The mechanisms for this are part of a full secure development lifecycle such as secure software delivery as well as secure boot, storage, and data recovery mechanisms.
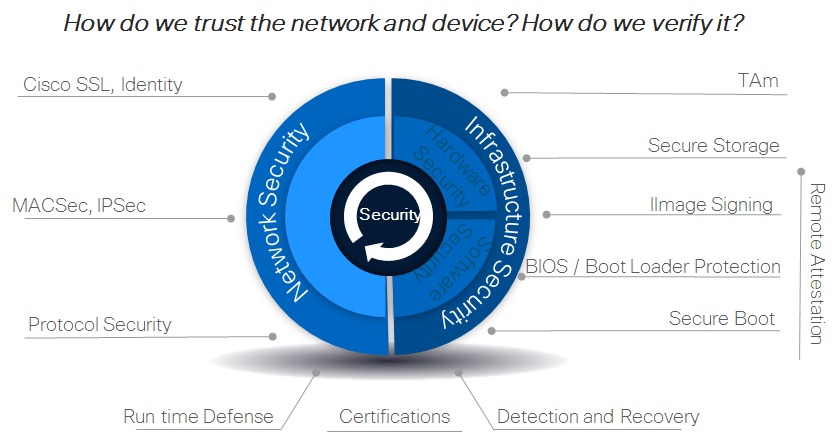
Being Trustworthy also involves authentication and access controls. For this, Cisco Trustworthy systems can verify digital identies to assure that authorized clients are using authorized services at all times. This helps to protect against threats such as false user identity, security breaches, false system identity, and weak cryptography. Specific measures Cisco Trustworthy systems rely on can span from advanced authentication to next-gen encryption techniques.
To manage detection and recovery from incidents, Cisco has also developed a comprehensive Management & Control systems ensuring the integrity of the network in real time. Telemetry-based device-integrity monitoring, assurance, and forensics are among the techniques that Cisco Trustworthy systems use.
Summary
The reality is that no one can stop all attacks, or protect all data or devices at all time. But by directly addressing the “operational space” that cyber criminals must have to be effective and profitable, you can prevent them from reaching critical systems and data without entirely evading detection. This is the true value of Cisco Trustworthy systems in securing your data and data centers from an increasingly diverse number of threats and attacks.
Tony Antony
Sr Marketing Manager




Excellent post, detailed and with very useful links that expands anyone knowledge. Thanks for sharing it. I’m waiting to read more.