Cisco is unquestionably leading in enterprise SDN adoption with over 1,000 ACI customers, 150+ customers in production, 45+ ecosystem partners benefiting from the ACI policy driven automation approach.
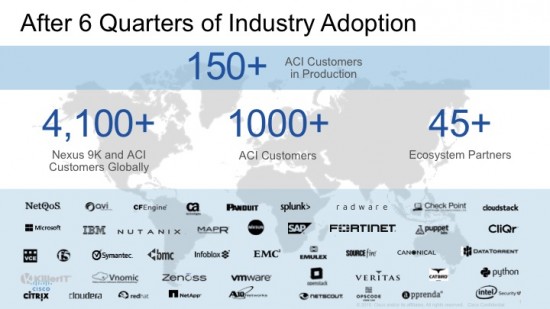
The robust and open APIs made it easy for the technology partners to rapidly integrate with ACI. The result is customers have the broadest set of security, monitoring, orchestration, and automation choices with the ability to adapt the ACI implementation to their own operational model.
And the best part is that we know that what we have built is working because our customers and partners are telling us (See List).
This dramatic pace of adoption has been noticed by the research and advisory firm, Gartner Group, and Network World that stated Cisco ACI is outpacing VMware NSX 2:1 in SDN.
Why is ACI Winning
Cisco ACI delivers an agile, open, and secure solution for deploying applications across any physical, virtualization or cloud technology being used for data center infrastructure.
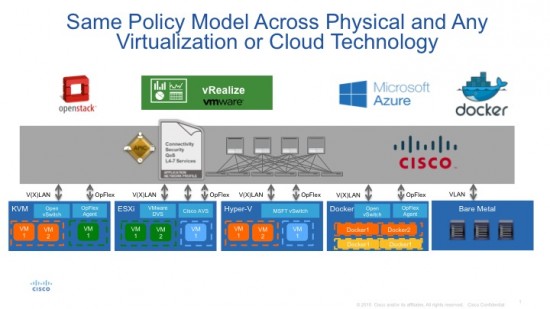
Cisco ACI provides consistent policy and operational flexibility for the leading cloud management platforms, for multi-hypervisor and bare metal server workloads. It is a true SDN solution with built-in secure multi-tenancy.
Arista’s Announcement is “Yesterday’s News”
We watch the industry for current developments in SDN and security and ran across a recent announcement from Arista. As in the past, it is good to see Arista trying to play catch up to what Cisco has been delivering for two+ years.
Curiously, Macro-Segmentation Services (MSS) was introduced by Arista, to support isolation with applications in modern datacenter networks. Based on the announced information, it appears that Arista is just splitting the network configuration job and customers would need two components: Macro-segmentation (Arista) and Micro-segmentation (VMware) in order to deliver on some of the security and isolation needs of applications and tenants.
It looks like Arista is finally agreeing with Cisco in recognizing that software-only micro segmentation offerings are not adequate to address the entire customer security needs and that physical support for isolation and security services is necessary.
Micro-segmentation, Macro-segmentation – What’s next?
Per Arista’s MSS approach, VM-to-VM isolation is handled by Micro-segmentation while VM-to-Physical workloads or Physical-to-Physical workloads are isolated by Macro-Segmentation. This naturally begs the following questions:
- When it comes to containers or micro-services, will customers need yet another form of segmentation? What will be the mode of interactions between these different segmentation technologies?
Clearly, customers can least afford to adopt many different combinations of segmentation for different end-points.
Clearing the Air
Before drawing our conclusion, given some of the FUD that has been used by Arista’s marketing in their announcement, we’d like to clarify a few important things in the best interest of customers.
- Cisco ACI talks standard frame format to any device.ACI can connect using standard VLAN, and VXLAN to virtual and physical end points and services. There is absolutely nothing proprietary in how Cisco ACI networks communicate with the rest of the data center infrastructure. If it were not the case, how would it be possible for over 45 partners to integrate and interoperate with Cisco ACI?
- “Open” to Cisco ACI’s 1,000+ customers means the ability to choose not just security services, but any L4-L7 services such as ADC, load balancing, firewalls, IDS/IPS, and more.
We provide choice of three modes of services operations to customers:
a. Complete automation: Fully automated service chaining with managed L4-L7 devices enables cloud automation, consistent policy across Physical+Virtual+Containers
b. Manual: Manually stitch any L4-L7 device into the service chain with any vendor, suited for customers migrating to network automation models.
c. Hybrid Model: Preserve current operating models for services admins but ACI will provide automation – for example, Security admins can continue to manage their services devices, while ACI automates service chaining.
All three modes can co-exist in the same network to preserve customers operating models and to allow the adoption of policy automation at a customer’s own pace. Oh by the way, we let customers have the flexibility to adopt this transition on an application by application basis, if desired!
- Unlike our competitors, we believe the network is in the best position to carry Application Policy because it touches every end point in the infrastructure. This architectural approach allows customers and ecosystem partners to apply policy consistently, automate enforcement, and simplify operations.
Conclusion
The future is already here — it’s just not very evenly distributed.
— William Gibson
Cisco is two years ahead of its competition, and with its customers and partners it is leading the SDN industry. Ironically, our competitors are supposed to be the disruptors, but they are focusing a lot on legacy solutions.
With Cisco’s 80% share of the network installed base, we knew we had to support existing operational models better than anyone. Therefore our architecture offers customers from Day One the choice and flexibility to preserve their existing operational models, and also provide a path forward to transform their datacenters with a common, consistent policy and security posture for physical, virtual, and containers, for their on-premise and hybrid cloud.
For More Information
Micro-segmentation: Enhancing Security and Operational Simplicity with Cisco ACI
New Innovations for L4-7 Network Services Integration with Cisco’s ACI Approach
An Overview of Network Security Considerations for Cisco ACI Deployments
Episode 4: Cisco ACI and IT Security Automation



