Last time in this space I covered APIGee, a component of the Cisco and Google Hybrid Cloud announcement that enables legacy data stores to be front-ended by a modern, secure API with analytics and monitoring. But if you have business logic running in the public cloud, how can you securely and reliably connect to that modern API?
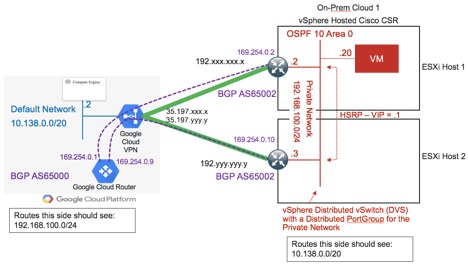
Another component to this relationship with Google is a set of Cisco Validated Designs (CVDs) for setting up redundant encrypted tunnels between Google Cloud Platform (GCP) and the traditional private data center. There are several different combinations of Cisco and Google products that can accomplish this and customers will not be left to their own devices to figure out the right set of configurations to get this right. One such set of products for which there will be a CVD is described here in this excellent diagram drawn by Cisco Distinguished Engineer, Shannon McFarland:
On the left side of this diagram is the GCP setup consisting of a Google Cloud VPN virtual device connecting to a Google Cloud Router. This will enable source/destination traffic on the 10.138.0.0/20 default private network within GCP.
Similarly, on the right side of the diagram sits a pair of CSR1000v virtual devices deployed on separate ESXi hosts for redundancy purposes. They have been configured in active/standby mode so that if one of the CSRs or hosts goes down, traffic continues without interruption. The pair routes traffic on the internal 192.168.100.0/24 private network with a combination of IPSec and BGP securing the connection.
Again, the details of configuring all of this will be provided by a CVD so partners and customers won’t have to do any original engineering here, instead benefiting from set ups tested by Cisco. When complete, and we’ll be releasing videos showing this closer to GA, you’ll be able to show continuous pings on separate terminal windows on VMs on either side of this connection and when rebooting the primary CSR see no packet loss between them as the second CSR picks up the traffic.
But is that enough to simply encrypt traffic between GCP and your private data center? What about more sophisticated security that leverages NetFlow on-prem and its equivalent in GCP? In a future post, we’ll explore the role played by Cisco Stealthwatch Cloud in the Cisco and Google Hybrid Cloud offering, all based on the acquisition of Observable Networks we made last July.