Gartner recently made three interesting predictions about mobility in the workplace. While the ideas are compelling, they only offer one-side of the story, and the solution.
In this blog post, I’ll take a deeper look at each of these predictions and discuss why the future of mobility rests on IT leaders taking a balanced and strategic approach to security that focuses more on protecting the network and proprietary data and less on implementing overly broad restrictions.
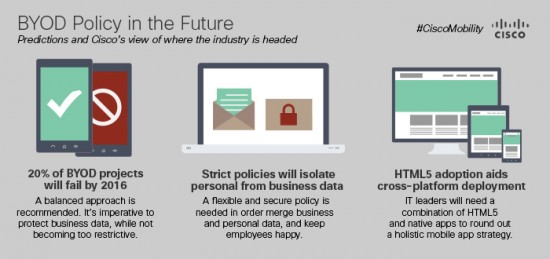
Gartner Prediction #1: Twenty percent of BYOD projects will fail by 2016 due to IT’s “heavy hand.”
While the actual failure rate may be less than one-fifth, mobility efforts will fail if companies are too restrictive with MDM policies. Instead, a two-fold approach to supporting a BYOD environment from a security perspective is essential.
First, IT leaders should take a balanced approach to security that protects business-imperative network solutions and data. In most cases, blocking Angry Birds and Candy Crush is unnecessary and not scalable. With Apple and Google supporting over a million apps each (and counting), it can cost precious time and IT resources just trying to keep up with restricting non-threatening applications.
Secondly, IT leaders should be focused on encouraging users to use secure solutions. This will only grow more important as the explosion of new connections and various devices evident in today’s Internet of Everything world creates more opportunity for malicious actors to utilize even more inroads to compromise users, networks, and data. By educating employees to take an active role in the security of their device, users can be empowered to report suspicious threats and have an open dialogue with IT teams.
Gartner Prediction #2: Strict mobility policies will drive employees to want to isolate personal data from business data.
I disagree that most employees want isolation of all business content. For example, my Contacts data is both corporate and personal. I have friends who work at Cisco and want to be able to access that information on one device. This capability is part of the beauty of BYOD. And as we start to see a merging of the “digital self”, thanks in large part to the growing consumerization of IT and the rise of cloud technologies, the ability to save work and personal information in one place is going to become even more important.
However, this does not mean privacy is not dead. Employees don’t want IT to access or change personal apps and content. In fact, a recent MobileIron study supports that the rising generation of workers value privacy in the workplace more than on social networks. According to the survey of over 3,000 workers across the United States, United Kingdom, and Germany, “employees over 55 were far more comfortable than 18 to 24 year olds with their company seeing their personal data.”
These beliefs and behaviors will continue to help shape the future of mobility. With these concepts in mind, IT leaders must evaluate and deploy and a flexible and secure infrastructure that can support an open BYOD policy and mitigate advanced security threats.
Gartner Prediction #3: Mobile browsers will gain market share for app delivery for multiple platforms, and the role of HTML5 in solving issues that arise with the multiple platform problem.
As the majority of users are accustomed to an App Store delivery model, it is unlikely mobile browsers will become a delivery method for apps. It doesn’t help that web bookmarks on mobile are completely broken. According to Business Insider Intelligence, only 20% of our time on mobile is spent in our browser.
However, all is not lost. HTML5 is a good technology to help solve the multiple platform problem, but it can’t do everything. IT leaders will need a combination of HTML5 and native apps to round out a holistic mobile app strategy.
A good example of this is how at Cisco, our internal apps are designed to deliver mobile moments of productivity to our employees. We don’t want employees spending time finding these apps, which is why we deployed Cisco eStore. Cisco eStore is our new internal app store powered by Cisco Prime Service Catalog. It is an essential part of our overall mobility strategy and one of the ways that we ensure employees are using secure, supported solutions.
As global mobile data traffic is set to significantly increase over the next few years, successful IT teams will continue to place the security and function of applications at the top of their mobility strategy.
The focus should be more on securing enterprise apps and data regardless of delivery method, and less on restricting use of these business-centric applications on employee-owned devices.
What are your thoughts about Gartner’s predictions? Join the conversation, follow @CiscoMobility on Twitter, #FutureofMobility.
Additional Information:
- Cisco Mobility
- Cisco Intelligent Network
- More of my blogs can be found here.


Some alternative thoughts on the Gartner predictions-
#1Twenty percent of BYOD projects will fail by 2016 due to IT’s “heavy hand.”
-Many companies today practice a lockdown strategy-no admin rights, for in general the ability to have a more controlled environment, essentially for their process of updating workstations. This should be blown up with a “BYOD” strategy for corp owned assets–essentially give users rights to install software, with the caveat that the company policy is to reimage the device with a baseline image should issues arise. This would mirror the employee owned personal device “BYOD” , and in the end, improve employee productivity.
#2 Strict mobility policies will drive employees to want to isolate personal data from business data.
-The real concern here is the wipe of all personal data from a device without the user having any backup of it. Better to have a policy that enables wipe of the device, combined with a provided service to Box, Dropbox, etc that provides a backup strategy of the device so the user isn’t petrified to lose all their personal contact data, photos, etc.
#3 Mobile browsers will gain market share for app delivery for multiple platforms, and the role of HTML5 in solving issues that arise with the multiple platform problem
-I think the concept of an in house/enterprise app store is good, but is it core or context to your organization? if they are just users of a service, and not actively developing the service, I would classify this as context-something you should NOT do , and rather find ways to intelligently redirect your users to the Apple/Android app stores, and not spend your resources here.
cheers
Mike
Whilst I agree that Gartner do make some valuable points and on your point, that the focus should be on securing enterprise apps and data regardless of delivery method, I do feel that there are some other key factors that need to be highlighted in respect of why many BYOD projects fail to deliver expected outcomes or lead to an exasperated workforce.
To fully exploit the power of the enterprise mobility in the workplace and to mitigate failure, it is imperative to view any implementation of BYOD, CYOD or hybrid thereof, not as an ad hoc deployment of technology and systems, but as a programme that requires careful business and technology planning. Any organisation embarking on such a programme needs to formulate an Enterprise Mobility Strategy that it includes the business and technology as well as governance aspects of mobility. It should define business goals and objectives, lay out an implementation roadmap, determine policies for governance, define relevant measurement models and address employee usage and adoption considerations. This all-embracing view of strategy is critical to securing the success of impending and future mobile related projects, internal and external focused.
A key consideration for success in any enterprise mobility strategy or indeed programme, often overlooked, or marginalised, is the importance of addressing the people challenge not just the technological one. This challenge is effectively one of a complex series of workspace change management issues encompassing new work styles that employees need to adopt, new technologies, processes and policies they have to learn, and even new ways of people management. Hence usage and adoption education, training and awareness activities need to be a critical part of any mobility initiative, introducing users to security and policy guidelines, potential risks and threats regarding company and client information, ensuring they are adequately briefed to use any tools responsibly, and allowing IT and management to set expectations. It can also provide the opportunity to demonstrate the potential beyond using the mobile device to check email and take the occasional call and for an open dialog between BYOD users, management, and the IT department that can contribute to the success of the program. Beyond programme roll-out, and new employee, training, on-going campaigns need to be considered to encourage utilisation of new enterprise mobile apps/tools, and for user groups to experiment and share their experiences with one another for social enterprise channels.
Here at Logicalis as part of our internal Enterprise Mobility programme, but also for use with our clients, we have developed a consultative strategic approach to the deployment of technologies that support and enable BYOD policies , utilising our “Mobility Experience Framework” which is designed to helping an organisation define and implement their mobility strategy and to offer both practical advice alongside proven solutions and services to make mobility a truly rewarding business experience for users and a less complex experience for the IT departments servicing their needs.
David Bennett
Proposition Manager, Communications & Collaboration
Logicalis UK Ltd