A few months ago, Cisco Security announced the SecureX platform with two core capabilities: threat response and orchestration. In that announcement, we brought attention to nearly two dozen integrations with SecureX threat response, formerly Cisco Threat Response.
With SecureX, you can accelerate threat hunting and incident response by seamlessly integrating SecureX threat response and your existing security technologies. You have the flexibility to bring your tools together, whether it’s with integrations that are built-in, pre-packaged, or custom. If you have Cisco Stealthwatch, Firepower, AMP for Endpoints, Umbrella, Email Security, Web Security, or Threat Grid; SecureX threat response is included with your license at no additional cost.
- Connect your entire security stack–Cisco or otherwise–for faster investigations
- Aggregate and correlate security context from multiple technologies in one view
- Get the most out of your existing security investments, including from our technology partners
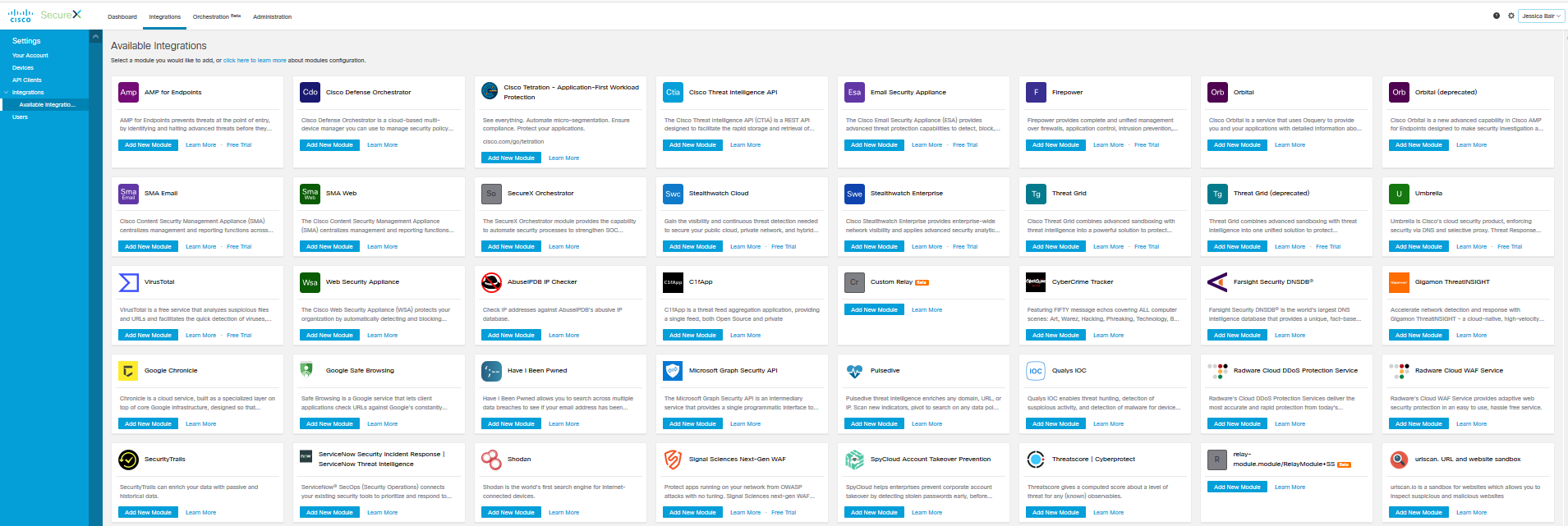
The SecureX platform has three categories of integrations:
- Built-in integrations are developed by Cisco, or select technology partners, for customers to instantly configure. These typically are integrations where SecureX threat response produces threat intelligence to be visualized in the partners’ user interface. Though there are some exceptions like VirusTotal or when a partner builds the threat response APIs into their core code.
- Pre-packaged integrations are developed by Cisco or technology partners for customers to use ready-made scripts that they install into cloud infrastructure, which they maintain. The time spent is minimized, as you don’t need to learn any APIs or write any code. These typically are SecureX threat response modules that produce threat intelligence to be visualized in SecureX. These are available modules in SecureX.
- Custom integrations can be created by customers leveraging Cisco and technology partners’ open APIs. The time spent on integration is reduced by using our resources on DevNet to quickly get started, including training, links to code on GitHub and extensive use case and workflow documentation on ReadtheDocs.
We made a promise in late April: “… we’re speeding up detection, investigation, and remediation across your environment with many more pre-packaged integrations. We are pleased to announce that time is now.
Built-in integrations
VirusTotal is a free service that inspects items with over 70 antivirus (AV) scanner and URL/domain blocked list services. The threat response VirusTotal module allows you to query a URL, IP address, domain or file hash, in the incident response process, to gain additional context from the AV scanners and services as to the threats associated with the sample. You can register for a free VirusTotal account and receive an API key. Threat Response uses the API key on your behalf to include VirusTotal query results in any investigation.
The threat response extension provides the capabilities to right-click pivot from an IP Address in QRadar into an investigation in the Threat Response console and hover over 100+ property field types and query threat response for Verdicts.

The threat response integration allows Polarity to search the Threat Response Enrich API to return information about various indicator types.
ServiceNow Security Operations
ServiceNow Security Operations (Security Incident Response and Threat Intelligence) can leverage the Verdicts, Refer and Response capabilities provided by threat response to assist the security analyst in their investigation workflow. This enables the analyst to take response actions from within ServiceNow to remediate threats.
SecureX Threat Response Add-On for Splunk provides a custom search command allowing users to query threat response for targets and verdicts from observables within a Splunk instance.
Phantom threat response plug-in enables a user, or an automated playbook/action, initiates a query to threat response for Verdicts or Sightings of an observable and render in a table.
Swimlane Security Operations Management
Swimlane threat response plugin allows connection to the Threat Response API, to extract and enrich observables.
TheHive Project – Cortex Analyzers*
The threat response analyzer connects to TheHive, a scalable, open source and free Security Incident Response Platform, tightly integrated with MISP (Malware Information Sharing Platform), designed to make life easier for SOCs, CSIRTs, CERTs and any information security practitioner dealing with security incidents that need to be investigated and acted upon swiftly.
Pre-packaged integrations
To utilize the pre-packaged integrations, you must first deploy a cloud infrastructure to implement the threat response serverless relay API. We created a step-by-step installation guide and recorded tutorials to make it easier and code on GitHub, that is pre-configured for AWS Lamba. The API itself is just a simple Flask (WSGI) application which can be easily packaged and deployed as an AWS Lambda Function, working behind an AWS API Gateway proxy using Zappa. An already deployed Relay API (e.g., packaged as an AWS Lambda Function) can be pushed to threat response as a Relay Module using the Threat Response Relay CLI. The threat response python API module is available with pip install.
Threat response module for the investigation of IPs and URLs. AbuseIPDB supports both IP and IPv6. API limits: 1000 / day. Returned Entities: Verdicts, Judgement, Sighting, Indicator.
Threat Response module to query AlienVault OTX for observables (IP, IPV6, domain, hash values) and return Sightings and Indicators from the “Pulses” in AlienVault. Pivot to AlienVault OTX UI via refer actions.
Threat Response module for investigations of IPs or domains and receives Sightings response from APIVoid blocklist aggregation.
Threat Response module for investigation of IPs. Query Auth0 Signals for an IP address to find out if it is on any blocklists. Return verdicts for the IP based on the scoring provided. Returns Open-Source Intelligence (OSINT) context from over 100 curated and normalized blocklists.
Threat response module for the investigation for verdicts on IPs and URLs, receiving Cybertracker Verdicts and Judgements.
Threat response module for the investigation of IPs, domains, hashes and file names. Returned Entities: Verdicts and Judgements.
The Farsight Security SecureX threat response module enables a user to initiate an investigation for verdicts on IPs and Domains. Farsight Security DNSDB provides enrichment data about IP Addresses (IP and IPv6) and Domains. Certified as Cisco Compatible.
The Gigamon ThreatINSIGHT module enables threat response to query network and threat data for Sightings of observables from the Gigamon intelligence. Gigamon completed the Cisco Compatible Certification for the integration and published a joint solution brief.

The Google Chronicle threat response module enables queries for Sightings of observables (IP, domain, hash, file name, file path) within the SIEM. Also, List Assets, obtain IOC Details, to List Alerts within a time range, and to List IOCs within a time range.
Threat response module for the integration of Google Safe Browsing; a blacklist service provided by Google that provides lists of URLs for web resources that contain malware or phishing content. The Google Chrome, Safari, Firefox, Vivaldi, and GNOME Web browsers use the lists from the Google Safe Browsing service for checking pages against potential threats, and this integration enables the user to have the blacklist intelligence in threat response.
Threat response module for the investigation of a SHA256. The module adds context around a compromised email and username associated with that email and context about a user for an environment. If Cisco Email Security Appliance module is enabled, then it returns that this SHA256 has been sent to identified email addresses, as has been seen in the data breaches. Small monthly for subscription.
The Microsoft Graph Security module queries for Sightings of an observables (IP, domain, hash, file name, file path) within Graph Security Alerts. Threat Response can access large volumes of Microsoft centric data as well as data from 3rd parties in a standardized format.
Threat response module for the investigation of URLs. Returns the Verdict.
The Quays Indication of Compromise threat response module is utilized for the investigation of Sightings of supported observables on Targets. Supports hashes (MD5, SHA256) of the file image on disk, the image on disk for a running process, and the image on disk for loaded modules. Also, File Name (Process Name), IP, Domain, File path and Mutex.
Radware WAF and DDoS
SecureX threat response modules for IP address(es) investigation, for both WAF and DDoS abusive activity, along with Indicators for those Sightings. Certified as Cisco Compatible.
Query SecurityTrails with this module, for enrichment data about Domains and IP Addresses (IP and IPv6). Pivot to Security Trails UI to search for Domains and IP Addresses (IP and IPv6).
ServiceNow Security Operations
The ServiceNow module in Threat Response, enables ServiceNow to be a data source when the analyst starts an investigation in the Threat Response UI or via the API. This enables the analyst to query ServiceNow for historical context from previous incidents that involved a given observable.
SecureX threat response Pivot / Respond menu on an IP address. Shodan is a search engine for Internet-connected devices. Web search engines, such as Google and Bing, are great for finding websites.
Signal Sciences Web Application Protection
Signal Sciences is a leading web application security company, with a next-gen web application firewall (WAF) and runtime application self-protection (RASP) solution. Through the threat response integration developed by Signal Sciences, your Security Operations team will have immediate visibility into attacks across all web application workloads With the integration, you can take immediate action. Certified as Cisco Compatible.
The SecureX threat response SpyCloud module empowers users to initiate an investigation into a SHA256. The module adds context around a compromised email and username associated with that email and context about a user for an environment. If Cisco Email Security module is enabled, then it returns that this SHA256 has been sent to e.g. these email addresses have been seen in the data breaches.
ThreatQuotient Security Operations Platform
ThreatQuotient periodically posts Judgements and Verdicts of observables to Cisco Threat Intelligence API, for visualization in threat response. In addition, ThreatQ uses threat response as an enrichment source for threat intelligence.
SecureX threat response module to submit URL(s) into urlscan.io for threat intelligence context.
The SecureX ecosystem will continue to grow, with additional integrations in development now, both by Cisco and our technology partners. You and your organization are also empowered to build your own. The power of the SecureX platform is yours.
Acknowledgements: My thanks to Michael Auger, manager of ecosystem integrations, and my partner in this endeavor. Michael designed the relay architecture that made rapid development possible, between SecureX and technology partners. Michael led a team of a dozen developers, program managers and quality assurance engineers, and worked closely with partners’ engineering teams; to build 27 integrations with 24 partners for the initial SecureX release. Well done!!
*Community/open source


Jessica and Michael,
Congratulations on a great SecureX Threat Response launch and making the life of security practitioners easy with these pre-built integration modules.
We are very excited about Gigamon ThreatINSIGHT and SecureX Threat Response integration and wish to solve the day-to-day security operational complexities of our joint customers.
Regards,
Ranjan & rest of Gigamon team
Thank you
Thanks Jessica and Michael for the continued and great partnership here. We look forward to continuing to drive repeatable security outcomes for out joint IBM & Cisco clients leveraging our complementary portfolios.
thank you