In my previous Blogs I have talked about Megatrends including BYOD, the Next-Generation Workspace, Video and the Internet of Things. One unfortunate reality all of these trends have in common is that they are going to put additional stress on your current Network and Security Infrastructure and Operational Process.
TrustSec uniquely offers the welcome opportunity to improve and extend Security Policy Control and the same time make it easier to Operate and Maintain. This post concludes the mini-series on TrustSec. Previous Blogs have looked at TrustSec in the DC and applied to VDI. Here I have asked Dave Berry Cisco TSA to take a step back and look at the bigger picture from Network Access to the DC.
First Dave I want to pose the question: Do we really need TrustSec?
Yes! My answer is an emphatic “Yes” Enterprise Information Technology has become so complex and dynamic that traditional mechanisms for access control, segmentation and security policy enforcement are no longer effective. TrustSec uses established protocols such as 802.1X at the wired or wireless edge, adds new capability and new control providing a layer of abstraction; to offer a unique, highly scalable and operationally efficient alternative to Dynamic VLAN or IP/Port ACL assignment.
TrustSec Security Groups are typically evaluated and assigned on access and enforced in the Data Centre and massively simplify end to end policy control and segmentation. TrustSec allows Security and Network operators to efficiently control, manage and monitor access to all resources including Virtual resources, no matter where the user accessed the network, with what device or where the required resource is located.
Dave a recent Gartner Blog suggested that “End to End” is now one of the most useless technical marketing terms. Yet when I hear people talk about TrustSec I always hear them use that term “End to End”! Could you please elaborate?
I use is too and I aim to show that “end to end” might be a tired and widely misused term – but with TrustSec it actually means something and it makes sense. In fact TrustSec is the exception that proves the rule.
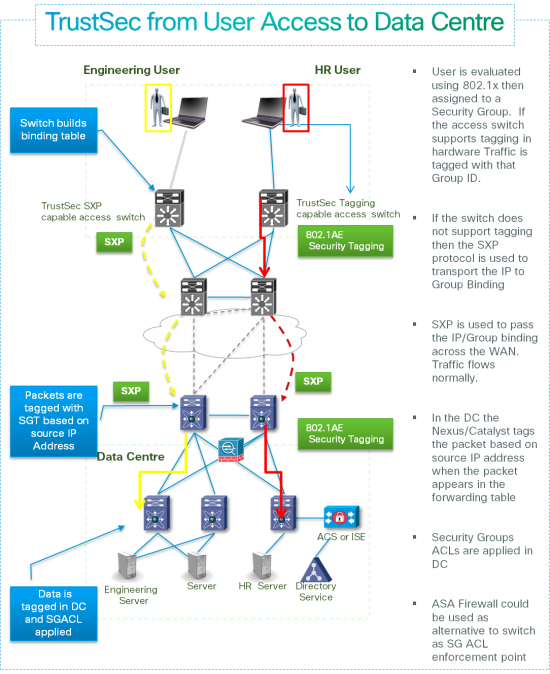
Access Switches and Wireless LANs can support TrustSec 802.1AE based Security Group Tagging in hardware and tag all packets from authenticated users with their evaluated Security Group. Alternatively if the Network Access does not yet support Tagging in hardware it can still assign TrustSec groups if it supports the Security group eXchange Protocol (SXP) which can dynamically inform a downstream TrustSec network device of the IP to Group binding it has learnt.
Data Centre switches across the Nexus and Catalyst product line can be used to read those Tags and enforce Security Policy. Alternatively with the support of Identity Firewall Phase 2.0 on the ASA, Group based security policy can be enforced with Security Group ACLs on the ASA.
What about TrustSec across the WAN for it to be truly End-to-End?
To complete the “End to End” story the intention is to support TrustSec SGT on WAN Routers as well as Campus and DC switches. ISR G2 Routers already support inline tagging using the ESP header in native IPSec and DM-VPN. More recently GET-VPN now supports inline tagging between ISR G2 and ASR with the Group Tag carried in the GETVPN header. By the end of 2013 all of IPSec, DM-VPN, FlexVPN and GET VPN should support native TrustSec on ISRG-2 and ASR1000. But in the example below the WAN doesn’t yet support native TrustSec –so we simply use SXP to pass SGT to IP mappings between the Campus and DC Switches that do support TrustSec.
 What about Policy Control? What are the benefits of using TrustSec in that case?
What about Policy Control? What are the benefits of using TrustSec in that case?
Enterprise Networks Switches, Routers and Firewalls end up with hundreds of thousands of lines of difficult to evaluate, understand and audit Access Control Entries (ACEs) based on Source and Host IP/Port numbers. These IP/Port ACEs can be replaced by ACEs based on intuitive and understandable policies using Security Groups.
TrustSec security groups offer an Architecturally elegant alternative to traditional network segmentation provided by dynamically assigned VLANs, Virtual Routing and VPN technologies. TrustSec SGA can provide scalable traffic separation, segmentation and mitigate the need to extend the use of Segmentation VPN technologies. TrustSec SGT can be implemented end to end without any need to change the current Network Topology.
Dave, how does this help you support Megatrends?
Enterprises and Organisations moving in response to and get ahead of the identified Megatrends will be challenged to maintain and improve Security Policy Control with traditional methods and techniques. TrustSec provides an alternative way to utilise the network and security infrastructure to support these new requirements and maintain control based on Security policy.
More Information
- TrustSec main page: http://www.cisco.com/go/TrustSec
- TrustSec Design zone: http://www.cisco.com/en/US/solutions/ns340/ns414/ns742/ns744/landing_DesignZone_TrustSec.html


CONNECT WITH US