Yesterday was “Back to the Future Day.” Michael J. Fox had a glimpse into his futuristic world. What if you too had the same capability? Imagine this: you’re an astronaut on a time travel space mission. You come upon a futuristic world years from today, and this is what you see.

Armed with this vision, what would you do if today, October 22, 2015, is your “Back to the Future” day?
This is a continuation of a previous post by Hugo Vliegen, Digital Vortex, Part I: How Not to Be the 40% That Will Fail. (Re-read that post here). In this blog (part II), I will share four key tenets of a digital business network, a.k.a recommendations for the hypothetical NeedToChange company scenario (as referenced in part I).
In Part I, We Learned That…
No company or industry is immune from the Digital Vortex. To cope with the vortex, businesses must innovate vigorously and relentlessly at a fast pace. And the WAN is the common denominator for business to transform into a technology-enabled digital business. Therefore, designing the right WAN architecture is the first – and critical step – in protecting market share and sustaining a legacy.
The Case of Need ToChange
The name implies it – NeedToChange must change. Its workforce becomes more distributed. The proliferation of bandwidth-intensive applications access via the cloud and of devices as a result of mobility and IoT are enlarging the surface areas for security threats. Demands for rich media content (voice, data and videos) cannibalize backhauled bandwidth for mission critical apps. OpEx and CapEx stay flat, and pressure for increased agility is surmounting. NeedToChange’s WAN infrastructure is calling for a transformation and its business impacted by digitalization.
Key Tenets of a Digital Business Network
A digital business centers on the digital experience, and that digital experience requires a combination of 1) voice, 2) video, 3) data services delivered securely on wired and 4) wireless platforms. Traditional WAN architecture already must balance among cost, uptime, performance, and security. Modernizing the WAN for the digital experience adds the need for agility and simplicity. NeedToChange must take a structured approach, one that optimizes performance without compromising reliability and security. Such approach pins on four key tenets:
- A transport agnostic architecture that opens up more connectivity;
- A policy-based application model that provides granular visibility, maximum control and optimizes usage and performance;
- A secure, scalable and resilient infrastructure to expand and contract per business needs and ensures 99.999% uptime; and
- A software-based controller model that promotes greater automation and orchestration.
Steps NeedToChange Should Take
Step I: Migrate to a hybrid WAN
Augment expensive MPLS links with cheaper transport such as the Internet. For disaster recovery and remote connectivity, consider 3G/4G LTE. Use an overlay routing design that allows for any type of WAN transport, which also opens up direct Internet access (DIA) for future cloud access.
Step II: Optimize and Protect Application Performance
Implement a See-Direct-Accelerate approach. The ability to see types of application, their performance, and response-time (AVC) is an integral capability required to plan, verify, and troubleshoot user experience issues. Grouping and directing key applications for quality of service (QoS) is the next logical step as it ensures appropriate bandwidth are reserved for mission critical apps. Finally, optimization is needed to further accelerate traffic and native and cloud apps performance (WAAS + Akamai Connect).
Step III: Protect the Edge and Enforce Centrally
Protect the network edge – from users, to endpoint devices, data, and access control – locally (Firewall, IDS/IPS), but enforce security policy centrally via a cloud-based model. Utilize best of breed cryptographic algorithms and advanced encryption to protect data integrity.
Step IV: Simplify Management via Automation and Orchestration
Leverage a controller-based architecture with open interfaces and an SDN services plane that allows for a) rapid and intuitive WAN deployments and b) fast and simple configuration of advanced network services such as VPN, application visibility, path control and QoS. Build on a price- and performance-optimized platform (UCS-E) that enables expansion beyond network services to unified communications, collaboration, mobility services and location-based analytics, for now, and branch services automation, in the future.
Download 2015 Guide to WAN Architecture and Design for more details on each of the step.
Your Next Steps
The Digital Vortex is in flux, and the “Future” is now for you to act. The WAN architecture you build today will shape your digital business and the innovations enabling that digital experience. Below is a list of recommended call-to-action.
- Move the WAN conversation to the board room; align technology needs with business initiatives
- Weigh the WAN challenges – see Table 2 below

- Define the scope and extend of the analysis
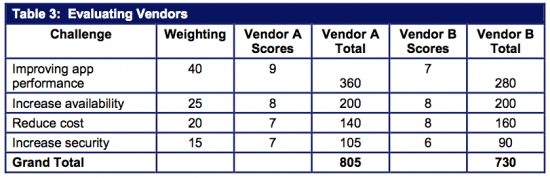
- Weigh vendor selection – see Table 3 below (In this step, organizations often overlook the importance of these factors: solution maturity, scope and scale of vendor’s support model, solution integration with existing WAN environment, longevity of the vendor, and its partner ecosystem. Make sure you don’t.)
- Build a business case that include hard savings in addition to soft savings
See a description of each call-to-action in 2015 Guide to WAN Architecture and Design.
Join the conversation. Comment, share and connect with us on Facebook, LinkedIn, @CiscoEnterprise, and the Enterprise Networks Community.


CONNECT WITH US