With the increased interest in cybersecurity and the recent news that utilities are being targeted around the world I’m making sure our readers have seen the latest white paper to come out of the Cisco ‘Brain-Trust’ on security in utilities and the energy industry.
https://www.youtube.com/watch?v=UA5yJLhL00g
As the white paper announces, “Utilities and energy organizations are part of the critical infrastructure of any nation, which makes them a high-profile target for cyber terrorists and hackers alike. Modernization brings gains in efficiency, but it also increases the attack surface through which threat agents can target utility infrastructure.”
It’s tough being a utility. Constant regulations, standards compliance, security and safety issues. Our security experts analyzed the IT security capabilities of the utilities sector in general, using specific data from the Cisco Capabilities Benchmark Study. They looked at the views of both chief information security officers (CISOs) and security operations (SecOps) managers and, different to other industries, seem closely aligned. What are the differences then, versus other industries? Here are some findings:
- 73% percent of IT security professionals at utilities say they’ve suffered a public security breach, compared with 55% in other industries.
- 56% percent of the IT security professionals in utilities say they use cloud-based web security, compared with 36% of the respondents in other industries.
- 64% percent of CISOs and SecOps managers in the utilities sector say they make use of mobile security tools, compared with 50% of security professionals in other industries.
One important note: The study focused primarily on IT security capabilities, not on the state of operational technology (OT) security. There is a growing trend of convergence between IT and OT, and I and others in Cisco have talked about the ramifications of that trend.
Despite my earlier claim that the data supports a similarity of views between CISOs and SecOps managers, interestingly the opinions of CISOs and SecOps managers diverge somewhat when the conversation turns to IT security controls. For example, 67% of CISOs say that their organizations have adequate systems for verifying that security incidents have actually occurred, but only 46% of SecOps managers say they have such systems in place. Also, 73% of CISOs say they have well-documented processes for incident response and tracking, while just 54% of SecOps managers say they have such systems. That’s worrying to me.
The white paper has lots of charts and supporting documentation, and discusses the differences between the utility industry and other industries, especially the readiness of using tools and the availability of funds focused on security. One things for sure: utilities are frequently a target of cyber attacks because of their high public profile and the potentially damaging effects of a data breach or service disruption. That explains the figures in my first bullet above (73% versus 55%). This vulnerability further highlights the security challenges that utilities are facing. In many countries, utilities have to report breaches by law, a requirement that may have contributed to the high number of recorded breaches. Perhaps due to their tightly regulated environment, utilities are also slightly more likely than other industries to use internal security incident teams.
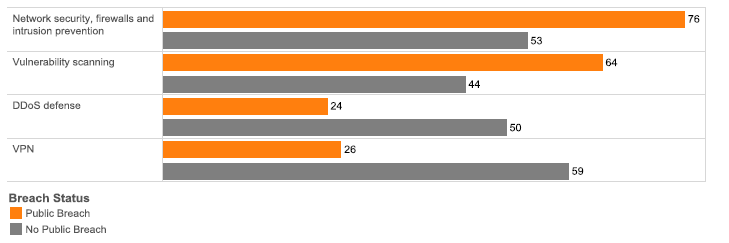
At any rate, utilities seem, in many cases, to learn the hard way. What do I mean? Well, publicly breached utility companies lean more heavily on tools such as network security, firewalls, and intrusion prevention systems (IPS), instead of distributed denial-of-service (DDoS) defenses or VPN security tools. For example:
- 76% of utilities that have dealt with a public breach say they use firewalls and IPS tools, but only 53% of utilities that have not dealt with a public breach use them.
- 64% of publicly breached utilities use vulnerability scanning tools, compared with 44% of non-publicly-breached utilities.
The figure above illustrates the point. Utilities’ Use of Various Security Threat Defenses (in %)
Interesting, eh? Also, public breaches appear to encourage utilities to more closely examine their security processes. For example:
- 64% of publicly breached utilities say they will quarantine or remove malicious applications. Only 41% of non-publicly-breached organizations say the same.
- 49% of publicly breached organizations will use external incident response and analysis teams, while only 21% of non-publicly-breached utilities will do so (see figure 9 in the white paper – it’s a chart that illustrates the above two points. I can’t give away everything here can I?).
You’ll have to view the white paper for yourself: Utility and Energy Security: Responding to Evolving Threats. I will agree with the authors’ final page comments:
…in conclusion, that regulatory compliance can sometimes lead to utilities being overconfident in their IT security infrastructure. New technologies bring new challenges, and threats are evolving faster than regulators can develop new standards. Regulations should be considered a baseline, not an all-encompassing solution. Executives in this industry have to continue to invest their time and effort in understanding how the IT security landscape is changing. They must be quick to adapt, focusing on business objectives and understanding that cybersecurity is an ongoing process.
Utilities may seem better in its security practices than other industries. But they have suffered significantly more public breaches, which indicates that they still have to improve their existing capabilities.
…and the white paper ends with some smart advice:
Utilities should also consider how their investment in security from an IT perspective can support their operational technology (OT) and the continuous modernization and growth of their business. IT and OT convergence is becoming more frequent with smarter grids, and its success relies on strong cooperation between these two areas. This integration should extend to security.
What do you think? Do you think the threat is overstated? As always, let me know by commenting!
quite informative
Thank you for your feedback. Any insight into Utilities in Africa you can share? I notice you’re address is from the School of Economics, University of Nairobi.
Until there is a major breach or attach against utilities most will not take it seriously. It the same as any other industry – until something horrible happens they just keep the lights on and make comforting unproven claims about how secure we are.
Thank you Janice. I’m sad to say you’re probably right. It’s a little bit like when I was a child we were always telling the city that our street was not appropriate for trucks to take a shortcut between major roads. It took the death of my 8 year old neighbor, Brian, who was run over whilst on his bike to make the local government authorities put physical width restrictions on at the end of the street to prevent trucks cutting through. I’m guessing the Western Ukraine power company Prykarpattyaoblenergo that reported an outage on Dec. 23, saying the area affected included regional capital Ivano-Frankivsk, will be taking more protective steps. It’s basically a war zone, of course, but other countries are taking note. The BlackEnergy trojan seems to be the culprit.
Excellent write up. It is very useful in analyzing the state of security in this sector. It seems that more visibility is needed within the infrastructure.
Yes Vinny, I agree – more visibility for sure – we’re working on getting the message out! The Cisco and partner value proposition is all about visibility into the critical infrastructure – the network is key, and real time visibility an essential requirement. There was a great presentation at DistribuTECH around BC Hydro and their 2m meter rollout where visibility can help prevent some of the $100m thefts they suffer from Marijuana Grow-Ops!
Thanks for your clearly written piece on this topic! Such a huge risk…hopefully your article and the white paper are taken seriously and read by those that need to take action.
Unfortunately, I agree with Janice and you, that it will probably take an catastrophe to motivate the necessary changes.
Thank you for the compliment Lori! We hope there will be more proactive measures taken to prevent a disaster, but we all know human nature….
This is so well done! Compelling – hoping it gets more public shares…
Thank you La’Treall – praise indeed from a colleague in Cisco’s Security & Trust Organization (S&TO!