This post was authored by Armin Pelkmann.
On September 8th, Cisco’s Talos Security Intelligence & Research Group unveiled the existence of the “Kyle and Stan” Malvertisement Network. The network was responsible for placing malicious advertisements on big websites like amazon.com, ads.yahoo.com, www.winrar.com, youtube.com and 70 other domains. As it turns out, this was just the tip of the iceberg. Ongoing research now reveals the real size of the attackers’ network is 9 times larger than reported in our first blog. For more details, read the Kyle and Stan Blog.
The infographic below illustrates how much more of the malvertisement network was uncovered in comparison to our first assessment. We have now isolated 6491 domains sharing the same infrastructure. This is over 9 times the previously mentioned 703 domains. We have observed and analyzed 31151 connections made to these domains. This equals over 3 times the amount of connections previously observed. The increase in connections is most likely not proportional to the domains due to the fact that a long time that has passed since the initial attacks.

Identifying all domains used by the attacker’s infrastructure helped us get a better view of the attack timeline. The first attempts to spread malware, spyware and adware are dating back to January 2012.
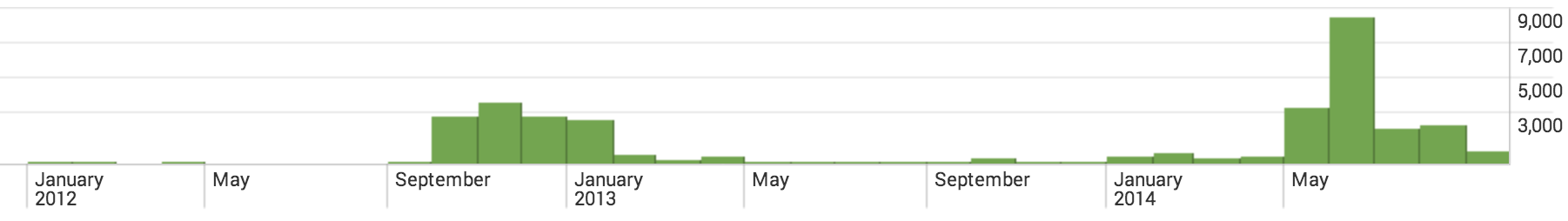
The domains of the type kyle.mxp677.com, stan.mxp681.com and lpmxp47.com seem to have usually a relatively short lifespan until they get replaced. The attacker seems to use them for a short while, burn them and move on to the subsequent number. Domains like megashre.info or file36.com seem to be used for a longer period and are still active.
Noteworthy is that the popular domain www.winrar.com is also part of these attackers network. The website is build to fool visitors into believing they are installing the popular compression tool WinRar, but instead they are downloading malware. This website exhibits a significant traffic load and is a good example on how the attackers behind this network are trying to fool users into installing their malware.

We also found plenty of domains that use a default page like this:
The source of the websites contains a few Spanish words in the JavaScript. Additionally a lot of the Whois records are pointing at services operated out of Spain.

While these indicators may not be entirely sufficient to determine the location of the masterminds behind this network, it is obvious that a part of the operation is run on servers hosted in Spain.
IOCs
Talos Security Intelligence & Research Group has uncovered huge parts of this malvertisement network. The list of domains broken down into different families:
- 1836 Kyle and Stan subdomains File 1
- 1895 mxp and lpmxp and other connected domains File 2
- 2760 pages that are mostly fake download websites File 3
Conclusion
The “Kyle and Stan” network is a highly sophisticated Malvertising Network. It leverages the enormous reach of well placed malicious advertisements on very well known websites in order to potentially reach millions of users. The goal is to infect Windows and Mac users alike with spyware, adware, and browser hijackers. The malware droppers employ clever techniques and encryption to ensure unique checksums to avoid detection.
The latest discoveries of this very blog have proven that the network is far larger than originally reported. The count of websites connected to the attackers infrastructure is now up to 6491 and is growing daily. The fact that parts of this infrastructure date back to January 2012 is concerning, as it shows that the threat actors have been active for over 2 and a half years. We’ve continued to push additional protection into various Cisco security devices to mitigate this threat.
Protecting Users Against These Threats
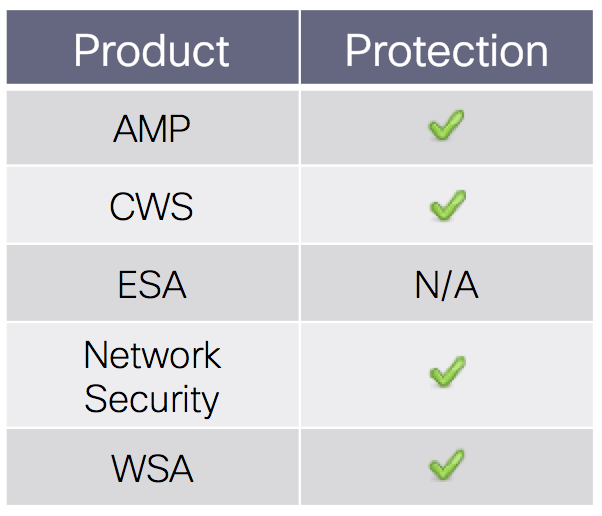 Advanced Malware Protection (AMP) is well suited to detect and block this type of malware.
Advanced Malware Protection (AMP) is well suited to detect and block this type of malware.
CWS or WSA web scanning will prevent access to the websites of the “Kyle and Stan” network.
The Network Security protection of IPS and NGFW have up-to-date signatures and will block this threat.
ESA is not applicable for this attack, because the threat is not using email.





FYI, file36.com (54.218.87.136) is listed as neutral (http://www.senderbase.org/lookup/?search_string=file36.com), hence the wsa will not prevent connections to that URL. The URL filtering functionality on the ESA does not appear to detect those suspicious links.
Hi pipo_knight,
this is odd. Everything in the backend works well and if you are a WSA or CWS customer you can see the reputations work correctly for all domains in this blog.
I informed the SenderBase.org team to check for a problem on their side. I’ll update you once it is fixed.
Thanks for notifying us.
/Armin
All fixed on SenderBase.org !
Thanks again for finding this bug in our web front-end.
Note: The front-end is completely separated from the backend that provides the protection to our customers.
What are the rule SID’s for Sourcefire customers?
Hi Kyle,
For AMP we got some samples here :
Looking up SHA256: 8A9CD910DE0349A1FD67D535E7AB6815E30544DD77D479A07932ECCB3F56E66E
Disposition: MALICIOUS
Detection Name: Osx.Trojan.Downlite.VRT
Looking up SHA256: 89A6827698BDFF134A2400EE5DB7E4B17256693A27107166EBA973E5B340D8CF
Disposition: MALICIOUS
Detection Name: Osx.Trojan.Downlite.VRT
Looking up SHA256: ED45848D90383A7BDB6FF1F0873EECB7C8396CCA425EE490054CD201E88EC6DA
Disposition: MALICIOUS
Detection Name: Osx.Trojan.VSInstaller.VRT
Looking up SHA256: 1DAF05E66F92B41F52860E95507C3D5E342F3582AF3B26A7D88F817FBC9BBB32
Disposition: MALICIOUS
Detection Name: Osx.Trojan.VSInstallerHelper.VRT
Looking up SHA256: 2C7C5D91C68F82F9095EC2FAFDF712D1EF26612017AC1BBAE9958519C7789BF1
Disposition: MALICIOUS
Detection Name: Osx.Trojan.VSearchAgent.VRT
Looking up SHA256: B04033409421AB84DA8882681ACE5B58AB3771199BBB1141F3C7C63CB71C9862
Disposition: MALICIOUS
Detection Name: Osx.Trojan.VSearchPlugIn.VRT
Looking up SHA256: E7EF2971139BCA0F3B4A0B2014522114FAC9792AA9AE61D3D5E0B89368947F75
Disposition: MALICIOUS
Detection Name: Osx.Trojan.VSearchLoader.VRT
Looking up SHA256: A3150AECD5F12B5A4108EF50044FEDC0C7B6B69B3EA83BF1E151AD5330F8FC8C
Disposition: MALICIOUS
Detection Name: Osx.Adware.Conduit.VRT
Looking up SHA256: E06F4340D890384457EF7370ABFE0D5E9D8E22F621A62DE835D589DCDB873155
Disposition: MALICIOUS
Detection Name: Osx.Adware.Conduit.VRT
Looking up SHA256: D1CA836F1D494F03B931550C722EA92B0A027E92C57484903B86DF686E31F2AE
Disposition: MALICIOUS
Detection Name: Osx.Adware.Conduit.VRT
And here is the SID : [SID] 32117-32120
I hope this helps.
/Armin