During World War I, British artist and navy officer Norman Wilkinson proposed the use of “Dazzle Camouflage” on ships. The concept behind Dazzle Camouflage, as Wilkinson explained, was to “paint a ship with large patches of strong colour in a carefully thought out pattern and colour scheme …, which will so distort the form of the vessel that the chances of successful aim by attacking submarines will be greatly decreased.” The Dazzle Camouflage was not intended to hide the presence of the ships themselves, but instead was created to hide the ships size, shape, direction, and speed from would-be attackers.

- Razzle Dazzle Camouflage applied to a ship
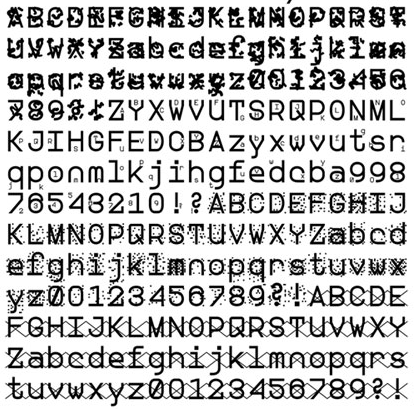
Fast forward to the 21st century, and there are new forms of Razzle Dazzle being deployed. At the end of May, 2013, artist and former National Security Agency (NSA) contractor Sang Mun published a collection of fonts called “ZXX”. ZXX is a typeface designed to be unreadable by Optical Character Recognition (OCR) software, yet retain its legibility to the human eye. Mun uses several different techniques to add distortion to the characters in the ZXX fonts. There are font characters containing camouflage prints, false characters, noise patterns, and even characters crossed out with X’s.
Those with tin foil hats may note that converting text documents to these new ZXX typefaces does nothing to obscure the (typically) ASCII binary data underneath the hood. It is the ASCII-encoded representation of the letters and words that carries the important data when text is not converted to an image format. If raw text data is going to be sent over a network, it must be encrypted to be secure.
However, encryption is no silver bullet. The end points where a message is encrypted and decrypted are still vulnerable to attack. For example, all computers run on electricity, and as a consequence generate electromagnetic radiation. This radiation can be captured from a distance, allowing an eavesdropper to reconstruct meaningful information about the data being processed on the device. To protect information from such electromagnetic leakage, Ross Anderson and Markus Kuhn of the University of Cambridge proposed using a font called “Soft Tempest” which is very similar to, but more advanced than the ZXX noise font. Soft Tempest is a font that is made up of grayscale glyph images that are individually tailored to add random noise to the least significant bits (LSB) of the image. Unfortunately most modern operating systems are neither equipped to handle grayscale fonts, nor designed with the capability of adding custom noise to each individual font character.

The steps necessary to achieve a modicum of privacy and security in the digital age are ultimately up to the individual or organization. However, we should all take the opportunity during the month of October, National Cyber Security Awareness Month (NCSAM), to reflect on the contents of our digital information. Once digitized, data can be snatched from the ether, and distributed around the world in milliseconds. What amount of protective security is necessary?
References
http://www.cnrs-scrn.org/northern_mariner/vol19/tnm_19_171-192.pdf
http://z-x-x.org/
http://www.cl.cam.ac.uk/~mgk25/ih98-tempest.pdf
http://www.cl.cam.ac.uk/~mgk25/emsec/softtempest-faq.html
http://staysafeonline.org/ncsam/about


CONNECT WITH US