Update 2014-01-10: This malicious campaign has expanded to include emails that masquerade as bills from NTTCable and from VolksbankU
Update 2014-01-21: We’ve updated the chart to include the Vodafon emails and latest URL activity
English language has emerged as the language of choice for international commerce. Since people throughout the world are used to receiving English language emails, spammers have
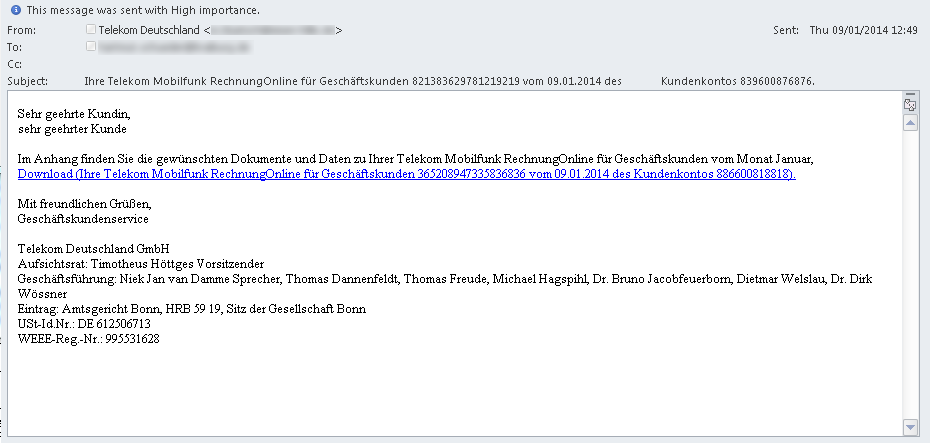
 also adopted the English language as the means of getting their message to large numbers of international recipients. However, spam messages that are written in a local language and that reference local companies can be particularly enticing for recipients to open because they do not expect malicious messages to be written in anything other than English. Cisco has observed and blocked a large number of malicious spam messages written in German language masquerading as phone billing statements. Initially the spam run masqueraded as Telekom Deutschland, with subsequent messages masquerading as messages from NTTCable and Volksbank.
also adopted the English language as the means of getting their message to large numbers of international recipients. However, spam messages that are written in a local language and that reference local companies can be particularly enticing for recipients to open because they do not expect malicious messages to be written in anything other than English. Cisco has observed and blocked a large number of malicious spam messages written in German language masquerading as phone billing statements. Initially the spam run masqueraded as Telekom Deutschland, with subsequent messages masquerading as messages from NTTCable and Volksbank.
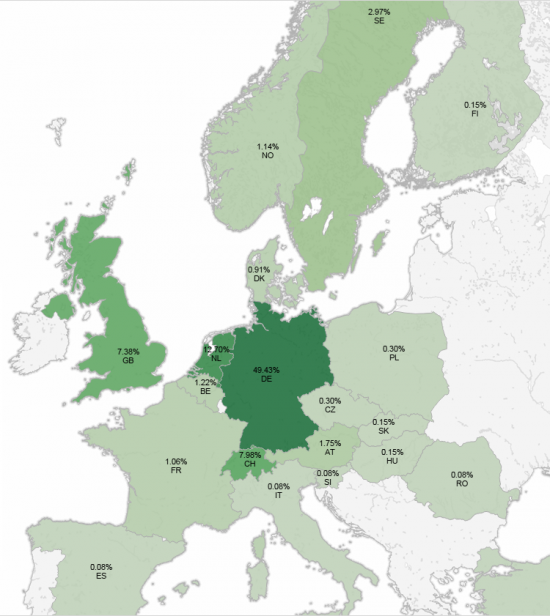
Cisco TRAC was able to locate what appears to be a single attack attempt, likely a test run, on 2013-12-16 however the majority of the attack started on 2014-01-05 and is ongoing. The malware is currently targeting users as depicted in the heap map below. The vast majority of attacks are occurring in Germany. It is reported that the end goal of this malware is to harvest credentials.
This heat-map represents the malicious URL activity we have detected and blocked:
Here is a sample message:
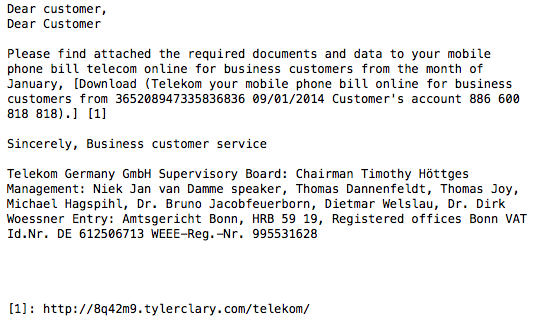
English translation:
All of the URLs involved in the attack follow a very specific format:
0abh26.hmlled.com/telekom/
0zc57s.moni-llc.com/telekom/
54kbpg.pelcastre.net/telekom/
6erdkf.dhc.com.ar/telekom/
6gfu71.xemtatca.com/telekom/
704yyi.garroba.com.ar/telekom/
7db4bb.taihinh.net/telekom/
7ipaeb.toastycomputers.com/telekom/
88a9fo.toolv.com/telekom/
bjr3at.arquidata.com.ar/telekom/
cahyx8.whodatninga.com/telekom/
da48it.xsenergy.ro/telekom/
dezrrn.photospace.biz/telekom/
e4uvqd.u-mine.cl/telekom/
eexlhh.ultimatepropertyevent.com/telekom/
f54z6k.incel.cl/telekom/
gchufm.drippingrockhoney.com/telekom/
gip053.csdue.it/telekom/
i30szj.koson-sf.ro/telekom/
jbvxdr.academyoftruesuccess.com/telekom/
jogyg5.15pifa.com/telekom/
k0dfbi.laughland.me/telekom/
k9kuk5.mikecramer.com/telekom/
mpkq1q.peliculeroweb.com.ar/telekom/
rjq5s1.balserv.ru/telekom/
sd1daa.aidangent.net/telekom/
sel8gi.24fit.tw/telekom/
sifrdz.firstfretmusic.com/telekom/
sm9eh1.theromantichearts.com/telekom/
tk1ud9.basler.com.ar/telekom/
tpf9qt.deadstockrock.com/telekom/
uquh4l.headsup.hk/telekom/
yz6sj0.windsormetalbattery.com/telekom/
ze1mtq.kcfullservice2.com/telekom/
zyctcf.viptt44.com/telekom/
16m0uu.oxip.me/NTTCable/
8pyhku.onesidedbox.com/NTTCable/
8ylz9l.ukmigrationlawyers.com/NTTCable/
alkogs.afrocenter.com/NTTCable/
bmv95b.taliaretelny.com/NTTCable/
dcx80n.worldofiniquity.com/NTTCable/
dl1ntk.kourkouta.com/NTTCable/
f5mg9k.krobath-brunner.ch/NTTCable/
ig27jj.idu.la/NTTCable/
jkcpmr.zabice.si/NTTCable/
jqq1ua.ceatlantida.com.br/NTTCable/
odx1rc.johnrappold.com/NTTCable/
upddezember.com/NTTCable/
xujrle.lapappy.ro/NTTCable/
16m0uu.oxip.me/NTTCable/
eicf1j.uwgraduation.net/volksbank/
newfirefox.ru/volksbank/
oz8pg5.stardustcommercialservices.com/volksbank/
v32gfe.saraplusjustin.com/volksbank/
We’ve associated the following MD5 hashes for the .zip file with this campaign:
40f85f501d17dd580850b47bc6de9da6 6945cb0e6cc05949b6fbf0fd5ff3c675 6a1483e974d6efd590a227c9986bc7c8 a5760773e39ed647d1d0dd4e160f80fa b024e181571132117c2aa6084fef8fde b745e834bf74ff0c5d2b6188d8062279 ff84658263ba9149458514c20f7de8de
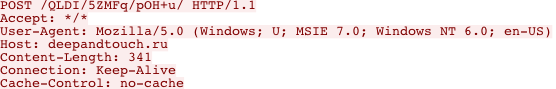
Upon visiting one of these URLs, a user is prompted to download a .zip file. The .zip file contains a trojan executable. The icon for the executable is a PDF file, which may trick some users into clicking on it. Upon execution, the malware immediately attempts to connect to the following servers:
beliyvolkalak.ru Service Port: 80
buriymishka.ru Service Port: 80
deepandtouch.ru Service Port: 80
djubkafriend.ru Service Port: 80
Once connected the bot issues the following POST request to each server:
This malware can be completely avoided if users simply follow best practices and refrain from downloading and running suspicious attachments. A reputable institution will never send an executable via email; users are urged to retrieve any necessary files from company websites. As always, it is a great idea to run software that verifies the MD5 checksum before running any executable file.
Special thanks to Martin Lee for coauthoring this post as well as Andrew Tsonchev for contributing.


Dear Sirs,
I represent the firm NTTCable which is one of the targets
of the campaign described in you article.
We are glad to hear that you are in the position to
block the downloads.
We appreciate your effort very much.
At present we still get many emails related to the spam campaign.
Larger part of the them contain the orginal
spam email as attachment an can be evaluated.
Are you interested in getting the copies of them
as soon as they reach us?
Or at least the download URLs?
We could arrange for this if you want.
With best regards,
Richard Limanowski
IT
____________________________________________
NTTCable Gruppe
Telefongesellschaft der Deutschen Industrie
Escher Str. 19
D – 65510 IDSTEIN
Tel.: +49 (0) 6126 – 9 98 76 – 52
EMail: r.limanowski@nttcable.de
Web: http://www.nttcable.de
Hi Richard,
Thanks for reaching out. I will contact you directly.
Craig
Dear Sir,
also attacked the hackers in Hungary too! They writen in emails German language in name of the Volksbank and HTTCable!
Best regards
Zoltan radvanyi
Hello Zoltan!
We’re tracking those as well. Thanks!
Craig
Could you please publish recently identified links, because at this time, this is the best source of information on the net on this topic. Thank you in advance!
Max,
The campaign seems to have dropped off recently. However, here are some further domains that we have identified.
Martin
0abh26.hmlled.com/telekom/
5c52p3.gingertom.com/telekom/
71ooxq.cyraxpainting.com/telekom/
aycfm5.helivahing.eu/telekom/
basanaj.ru/NTTCable/
cfxosp.addvantive.net/telekom/
fkq975.fernandoarenas.com.ar/telekom/
ik473x.organizacionelpais.com.ar/telekom/
motott.ru/telekom/
mrvn2n.prod-intl.com/telekom/
newfirefox.ru/NTTCable/
newfirefox.ru/telekom/
o5pcap.masvolumen.com.ar/telekom/
oldappstore.ru/NTTCable/
oldappstore.ru/telekom/
olp7o7.newceg.ro/telekom/
rossiusserv.ru/NTTCable/
rossiusserv.ru/telekom/
securesertupdate.com/telekom/
ssl-cheker.com/telekom/
tn1kas.pgd-log.si/telekom/
tryidon.ru/NTTCable/
tryidon.ru/telekom/
ug2poo.xpucmoc.org/telekom/
upddezember.com/telekom/
vj5yii.netcomputer.ro/telekom/
vkokoi.ru/NTTCable/
vkokoi.ru/telekom/
vkokoi.ru/volksbank/
zyctcf.viptt44.com/telekom/
I think the campaign still alive! I have mail from yesterday, but not in my own motherlanguage but german!
Thank you Martin, it seems, that they register new domains every second 🙁
The newest SPAM-URLS end with /vodafon
(without e)
the malware started to come with different mails. The latest is pointed to here:
http://pososh.ru/vodafon/
malware is the same but regenerated again. the MD5 is different .
it have the same options. browser passwd steal, cookie steal, ftp and pop3 steal..
We’re now seeing the following URLs and MD5s as part of the same campaign.
evilzp.tyhe.ro/telekom/
ghpet1.adondejugamos.com.ar/vodafon/
mmc-tt.ru/telekom/
mmc-tt.ru/vodafon/
moiiu.ru/telekom/
moiiu.ru/vodafon/
perzperz.ru/telekom/
perzperz.ru/vodafon/
pososh.ru/telekom/
pososh.ru/vodafon/
upddezember.com/NTTCable/
upddezember.com/telekom/
48d0b4f126d29200f2dc0a692e50a64e
53098f59a5b6706dd58292b685a28ba0
75fca9f254dc0eed51cb651f34e2d475
78d75fb3dd988a536046160c2e9d11b0
7d34e7690ebe9aa4ffe12697f9c4eb18
84f60efd2e13f0cf4eda063bc83cea30
996f0d68d922dbfd9b2422c68cf7f924
a7fd8060c27e2521140304041ece4de1
d818a65dadad40801d8eee6986154417
f4ebeeaac2d85a383f38972d3c0819d5
f526d124b34e1a42c08c05516a4f3321
fc814ae9709ef7c7d1817fd7f959373f
any news? any sigset for it or anything?
If you´ve got spamassassin maybe the following regex will help you:
uri [Name of the rule] /([a-z0-9-]+\.)?[a-z0-9-]+\.[a-z\.]{2,6}\/(telekom|volksbank|nttcable|vodafon)\//i
Can’t we have a universal list in which all these domains are listed and when someone clicks on a link in email, it checks in that list and then opens the page ??
Hi Rohan,
What you are describing is is very similar to how some of the web security appliance (WSA) technology works. If you attempt to click on these links from behind a WSA you will get a security threat detected and blocked message from the appliance. Cloud web security has similar protection.
Thanks
Craig
getting closer… 🙂
00411B5C 47 65 74 50 72 6F 63 41 64 64 72 65 GetProcAddre
00411B6C 73 73 00 00 4C 00 6F 00 63 00 61 00 6C 00 5C 00 ss..L.o.c.a.l.\.
00411B7C 58 00 4D 00 51 00 25 00 30 00 38 00 58 00 00 00 X.M.Q.%.0.8.X…
00411B8C 4C 00 6F 00 63 00 61 00 6C 00 5C 00 58 00 4D 00 L.o.c.a.l.\.X.M.
00411B9C 42 00 25 00 30 00 38 00 58 00 00 00 25 75 2E 25 B.%.0.8.X…%u.%
00411BAC 75 2E 25 75 2E 25 75 3A 25 75 00 00 63 72 79 70 u.%u.%u:%u..cryp
00411BBC 74 33 32 2E 64 6C 6C 00 00 00 00 00 65 00 78 00 t32.dll…..e.x.
00411BCC 70 00 00 00 2E 00 62 00 61 00 74 00 00 00 00 00 p…..b.a.t…..
00411BDC 00 00 00 00 40 65 63 68 6F 20 6F 66 66 0D 0A 3A ….@echo off..:
00411BEC 52 0D 0A 64 65 6C 20 2F 46 20 2F 51 20 2F 41 20 R..del /F /Q /A
00411BFC 22 25 53 22 0D 0A 69 66 20 65 78 69 73 74 20 22 “%S”..if exist ”
00411C0C 25 53 22 20 67 6F 74 6F 20 52 0D 0A 64 65 6C 20 %S” goto R..del
00411C1C 2F 46 20 2F 51 20 2F 41 20 22 25 53 22 0D 0A 00 /F /Q /A “%S”…
00411C2C 43 00 6F 00 6D 00 53 00 70 00 65 00 63 00 00 00 C.o.m.S.p.e.c…
00411C3C 22 00 25 00 73 00 22 00 20 00 2F 00 63 00 20 00 “.%.s.”. ./.c. .
00411C4C 22 00 25 00 73 00 22 00 00 00 00 00 2E 00 00 00 “.%.s.”………
00411C5C 2E 00 2E 00 00 00 00 00 0D 0A 00 00 47 45 54 00 …………GET.
Hi Albert,
I’ll unicast you to see if I can help further, that looks suspiciously like an IPS signature alert 🙂
Thanks
Craig
Today we found a lot of the backdore Software. May some of the first versions, not crypted. Its pretty well programmed.
But my point. We assume that this Spam-Wave are connected to the massive WordPress Botnet attack last autumn.
Does anyone know more?
Best regards.
P.S. All Bot commands come today from Austria.
More URLs this time with a change of format:
frgty.ru/telekom_deutschland/
frgty.ru/vodafone_online/
gorbache.ru/telekom_deutschland/
gorbache.ru/vodafone_online/
gorbache.ru/volksbank_eg/
lopper.ru/telekom_deutschland/
lopper.ru/vodafone_online/
lopper.ru/volksbank_eg/
opa-oba.ru/telekom_deutschland/
opa-oba.ru/vodafone_online/
opa-oba.ru/volksbank_eg/
pivtorakco.ru/telekom_deutschland/
pivtorakco.ru/vodafone_online/
sencert.ru/telekom_deutschland/
sencert.ru/vodafone_online/
sencert.ru/volksbank_eg/
serverrequiestcont.ru/telekom_deutschland/
serverrequiestcont.ru/vodafone_online/
serverrequiestcont.ru/volksbank_eg/
another one I think:
gerbercvt.ru/volksban_eg
It makes so sense to collect the DNS Names. There are already over 100 and every second, there are new ones.
You should trigger the pattern of the link.
Hello,
I’m in France and I’ve received this mail on this afternoon (20 January 2014) and in German language, it is from Telecom Deutschland and seems to be a bill too.
Best regards.
Charlotte
Hello Charlotte,
We’ve updated the heap map to reflect current activity. As you can see the campaign is much more widespread right now.
Thanks
Craig
Hi everybody, I fell in this trap and clicked the link. It directed me to a blank page and a download never started, chrome then told me couldn’t load the page. I use a macbook pro. I am very ignorant of this matter and scared.
The link it directed me to was vkokoi.ru/telekom/. Saw it on the list mentioned by Martin. I found this post when attempted unsuccessfully to see the “bill” for the third time. Any suggestions as to detect something dodgy?
Also, just to clear it out. There is no link in the email to an executable, is merely a link like many providers do with their real invoices.
No I will always check where the address is going to before clicking!
Hi Danilo,
Thats the danger of these kinds of attack, it is so easy to fall for them. If you think that you might have clicked on one, download and install an AV client to scan your machine. The major AV vendors will be detecting these malware.
If you want to prevent users from clicking the links on the first place, install a multi-layered set of filters, include an anti-spam filter to keep the emails away from users’ inboxes and a web filter to block any malicious links. Take a look as Cisco ESA device for emails and Cisco CWS or WSA for web filtering.
Some attack also reported in Poland. Hope my AV Software wont pass this through…
The NOD AV certainly pass this trough. Need some restart but kill them. I dont no the others…
I have a BAT script which can check your device is infected or not 🙂
I believe the best way to stay safe from any malware or phishing site is to never download anything that they force you to do.
But in case you feel, the download is important then make sure to do an online virus total scan of the attachment before downloading it.
I usually follow the same tips when it comes to online security.