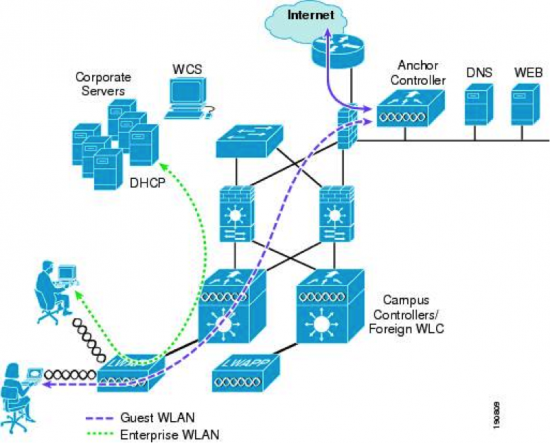
A couple of months ago I designed a Cisco Unified Wireless Network for an enterprise company. One of the big challenges was the ability to serve wireless guest services in the branch offices, which are connected to the headquarters via MPLS. Mostly the MPLS connections are terminated in the LAN zone, so it is difficult to tunnel the guests via the corporate infrastructure to gain internet access. I achieved this in the Cisco environment with the Mobility Anchor feature. With this feature, you can offer a flexible and easy-to-implement method for deploying wireless guest services by using Ethernet in IP within a centralized architecture. Ethernet over IP is a proprietary tunnel across Layer 3 topology between two Cisco wireless LAN controllers. For more Information see: http://goo.gl/6pjXcZ
Now I tried to achieve this tunnel method with the Cisco Cloud Networking (Cisco Meraki) products. I wanted to place these products in an enterprise environment and find a solution to serve wireless guest users in branch offices. My first idea was to use the built-in Identity-Based Firewall (http://goo.gl/nq9Au3) on the Access Point. This is a good solution when there is a homogeneous Cisco Meraki environment, because then you can manage the HQ access rules centralized and generate the wireless guest user in the Meraki Dashboard. Every pro has a con, and this is very critical. Germany is not the only country were there is a liability for disturbance law. In case one of your guests breaks the law by participating in illegal file sharing you have to log the events. So I started again to reflect on the needs and got a brilliant idea!
With the *free* Meraki VPN Concentrator, there is a method to tunnel the wireless guest users in the branch office to the headquarters. In the HQ I created a non-routed VLAN, which is terminated on the Firewall. I assigned the access and logging rules on the firewall and created a captive portal to authenticate the guests. In the “secured” VLAN I installed the VPN concentrator (In a previous post you can read on how easy it is to install and configure the VPN Concentrator http://goo.gl/HsAhWZ). Finally I connected the guest SSID from the branch Access Point to the corresponding VPN concentrator.

With this great Solution, all needs are solved:
– Centralized architecture
– Centralized and consolidated access rule
– Centralized logging
– Centralized guest user management
I work for a system vendor where we have been using, recommending and installing Cisco Meraki Cloud managed products since Cisco acquired Meraki in 2012 and we have been enthusiastic about their products from the beginning. The Cisco Meraki Magic got to us! http://goo.gl/RV5Hej

Feel free to contact me if you have any questions.
@: Sven Kutzer: thanks for post 🙂