 Cisco hosted our first Networkers customer event, now Ciscolive!, 25 years ago. Our first event was small with around 200 attendees focused on multiprotocal routing technologies. This year more than 25,000 Cisco customers, partners, press, and analysts attended live in San Francisco, with over 200,000 participating online with topics ranging from Intercloud, Collaboration, Security, and Application Centric Infrastructure (ACI) to Connected Cities with Smart Parking, Traffic Management and Public Safety, Connected Transportation, and Connected Government driving mission success to protect, educate, and serve.
Cisco hosted our first Networkers customer event, now Ciscolive!, 25 years ago. Our first event was small with around 200 attendees focused on multiprotocal routing technologies. This year more than 25,000 Cisco customers, partners, press, and analysts attended live in San Francisco, with over 200,000 participating online with topics ranging from Intercloud, Collaboration, Security, and Application Centric Infrastructure (ACI) to Connected Cities with Smart Parking, Traffic Management and Public Safety, Connected Transportation, and Connected Government driving mission success to protect, educate, and serve.
I attended my first Cisco Networkers event 20 years ago in San Francisco and have worked on many exciting initiatives during my career the past 2 decades. The role of networking technology as a platform for the Internet of Everything continues to evolve and accelerate more quickly being adopted and deployed in countries and communities around the world.
The week kicked off with keynotes and demonstrations highlighting the advances in technology as well as the potential for transformation in business and public sector.
- John Chambers Welcome Address and Keynote Vision that explored the human face of technology and how the Internet of Everything has already begun to transform the way people live.
- Public Sector Keynote with live demonstrations and discussions for how the “Internet of Everything” will impact Public Sector desired missions to protect, educate, and serve.
- Collaboration Keynote with live demonstrations of new desktop collaboration experiences, including the DX80, DX70, and Collaboration Meeting Rooms.
- California Department of State Hospitals roundtable shared story about the power of technology to deliver a safer work environment.
- Security Keynote vision for new security model for the IoE world that’s threat-centric with visibility across the entire attack continuum—before, during and after.
- Sal Kahn, founder of The Kahn Academy, and Author of The One World School House keynote Reimagining Education.
Continue reading “Ciscolive! 25 Years of Networkers”

 Written By Dan Kurschner, Senior Manager SP Mobility Marketing
Written By Dan Kurschner, Senior Manager SP Mobility Marketing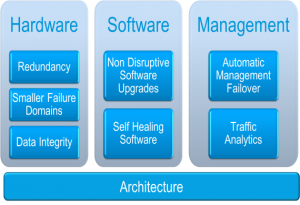 So let’s continue our discussion. There is no doubt when it comes to High Performance SAN switches there is no comparable to Cisco MDS 9710. Another component that is paramount to a good data center design is high availability. Massive virtualization, DC consolidation and ability to deploy more and more applications on powerful multi core CPUs has increased the risk profile within DC. These DC trends requires renewed focus on availability. MDS 9710 is leading the innovation there again. Hardware design and architecture has to guarantee high availability. At the same time, it’s not just about hardware but it’s a holistic approach with hardware, software, management and right architecture. Let me give you some just few examples of the first three pillars for high reliability and availability.
So let’s continue our discussion. There is no doubt when it comes to High Performance SAN switches there is no comparable to Cisco MDS 9710. Another component that is paramount to a good data center design is high availability. Massive virtualization, DC consolidation and ability to deploy more and more applications on powerful multi core CPUs has increased the risk profile within DC. These DC trends requires renewed focus on availability. MDS 9710 is leading the innovation there again. Hardware design and architecture has to guarantee high availability. At the same time, it’s not just about hardware but it’s a holistic approach with hardware, software, management and right architecture. Let me give you some just few examples of the first three pillars for high reliability and availability.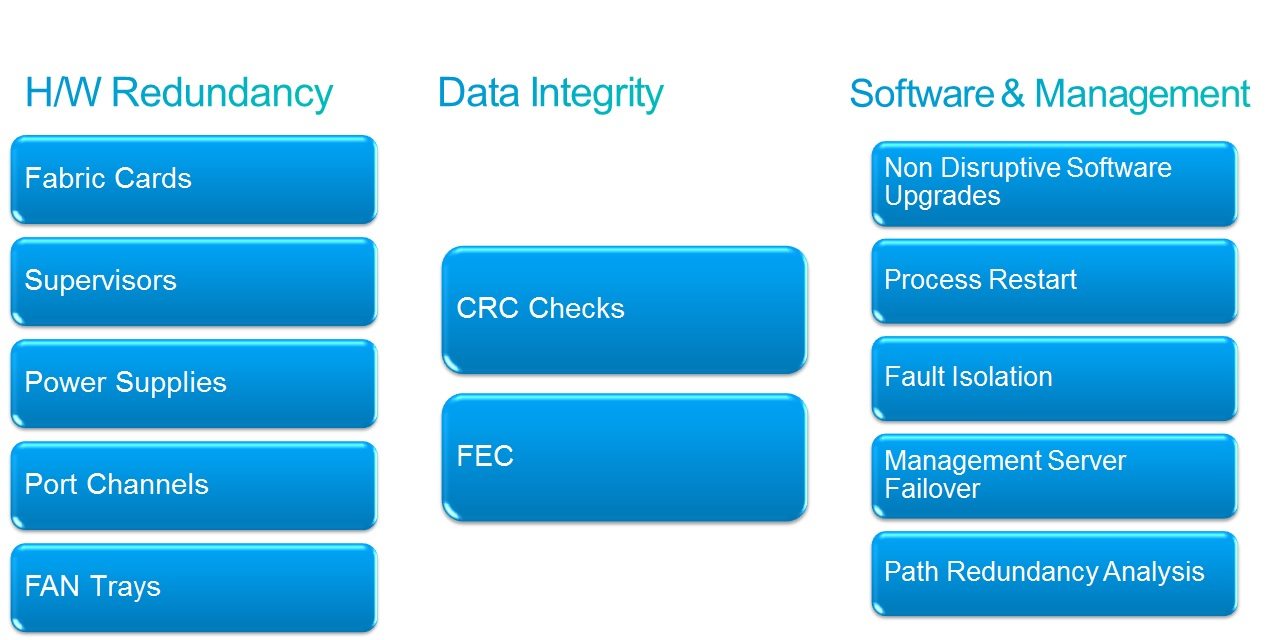





CONNECT WITH US