 Written By Igor Dayen, Manager, Service Provider Marketing, Cisco
Written By Igor Dayen, Manager, Service Provider Marketing, Cisco
Cisco Live! 2014 in San Francisco was bigger, better, and bolder than ever this year. There was a record breaking 25,000 registered customers, partners, press and analysts at the event. The Service Provider Program has allowed the attendees to witness firsthand latest innovations and solutions as the service provider booth made its debut on the show floor. Cisco Live! was packed with educational sessions and our booth staffers ran live demonstrations to solutions to provide visual proof points to the material presented during the breakouts. This was also a debut for the Service Provider to have its own booth in the Main Cisco campus. As the 2014 US edition of Cisco Live! in San Francisco came to a close, I wanted to share a few thoughts and links with our readers so that they can tune into some of the great content and photos of the event.
Watch our postcard video that takes a look at activity in the service provider booth at this year’s show! 
L ike any good story starts, the week for the Service Provider program kicked off with an energizing keynote by David Ward, Kit Beall, and Kelly Ahuja. During the SP Keynote, Kit Beall posed a question once asked by the novelist Victor Hugo: “Will the future ever arrive?” This resonated very well with the theme of the overall program for service providers at Cisco Live. Before the event we had posted an SP community blog where we began exploring the value of SP open network architecture. With the Evolved Programmable Network (EPN) and the Evolved Services Platform (ESP) architectures being the key pillars of SP open network architecture you have more options on how you will architect and build your network so that the applications can be successfully deployed. But is that really enough for the service providers to evolve in the future? Cisco’s answer is agility, lower costs, and new revenue opportunities made achievable with virtualization, programmability, and open standards that come with SP open network architecture. When architected this way, services can be deployed more efficiently, faster and with better SLAs. At Cisco we provide the solution which exactly does that. Overall, during the SP keynote the key message to service .providers was innovation, automation, and virtualization.
ike any good story starts, the week for the Service Provider program kicked off with an energizing keynote by David Ward, Kit Beall, and Kelly Ahuja. During the SP Keynote, Kit Beall posed a question once asked by the novelist Victor Hugo: “Will the future ever arrive?” This resonated very well with the theme of the overall program for service providers at Cisco Live. Before the event we had posted an SP community blog where we began exploring the value of SP open network architecture. With the Evolved Programmable Network (EPN) and the Evolved Services Platform (ESP) architectures being the key pillars of SP open network architecture you have more options on how you will architect and build your network so that the applications can be successfully deployed. But is that really enough for the service providers to evolve in the future? Cisco’s answer is agility, lower costs, and new revenue opportunities made achievable with virtualization, programmability, and open standards that come with SP open network architecture. When architected this way, services can be deployed more efficiently, faster and with better SLAs. At Cisco we provide the solution which exactly does that. Overall, during the SP keynote the key message to service .providers was innovation, automation, and virtualization.
Following the three key announcements Continue reading “Server Provider Has Never Been Better at Cisco Live!”
 It’s also about
It’s also about 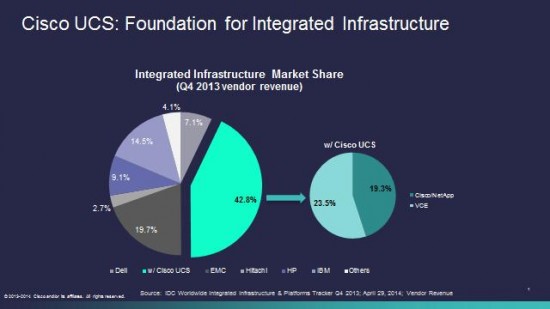
 in the Americas and #2 World Wide (according to the most recent IDC Worldwide Quarterly Server Tracker – May 2014). Cisco UCS has delivered some ground breaking technology. The policy-based
in the Americas and #2 World Wide (according to the most recent IDC Worldwide Quarterly Server Tracker – May 2014). Cisco UCS has delivered some ground breaking technology. The policy-based 


CONNECT WITH US