In a multi-point TelePresence press briefing on Friday 31st May Cisco Australia and New Zealand (ANZ) Managing Director, Ken Boal, and VP for Global Technology Policy, Dr. Robert Pepper, teamed up to deliver the Australian and New Zealand specific findings of the annual Cisco Visual Networking Index.

The latest forecast paints a picture of a world which is consuming the Internet at an astronomical rate with the Cisco VNI predicting that in 2017 there will be more than 19 billion devices connected to the internet! Dr. Pepper and Ken Boal were quick to point out to the attending media from ANZ that these 19 billion devices will increasingly be made up of devices that many people never thought would be Internet-enabled. As we move into the era of the Internet of Everything, more and more items will be connected to the Internet. Livestock, wearable tech and household appliances were just some of the examples given.


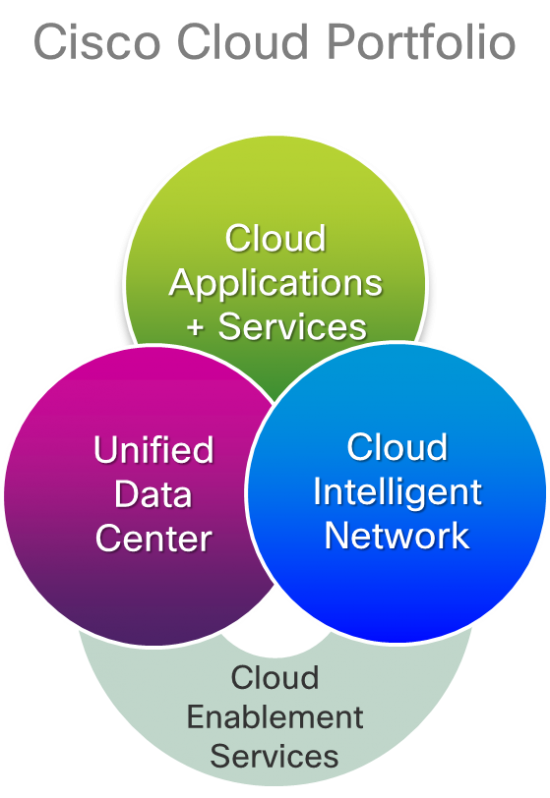 Among all the Megatrends that have significant implications from an infrastructure perspective (as discussed
Among all the Megatrends that have significant implications from an infrastructure perspective (as discussed
CONNECT WITH US